Guide quick menu
Always-On Audit Evidence — Access Logs, Retention Records, Encryption Proof, and Change History — Produced Automatically by Your Own AWS Infrastructure
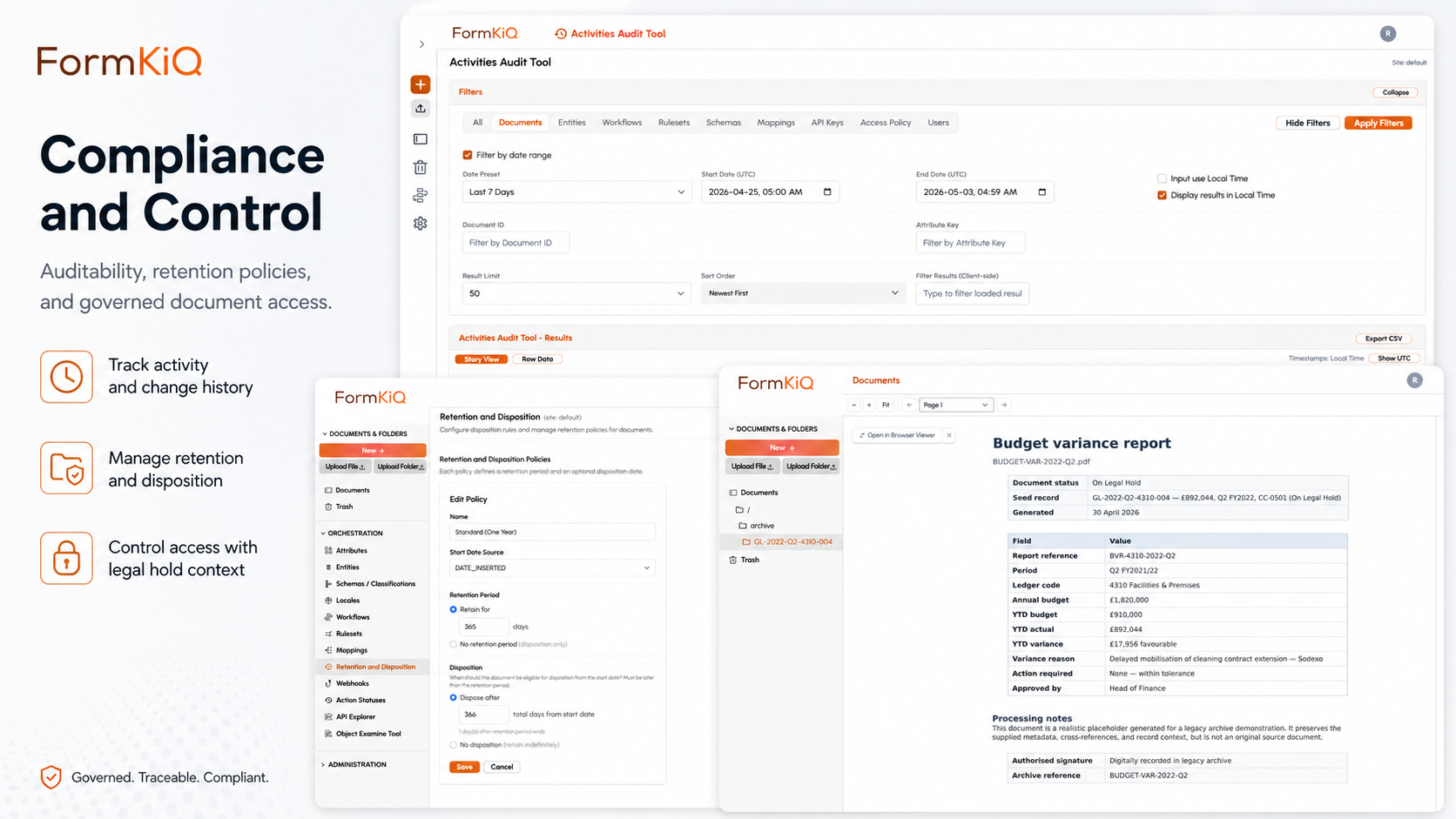
Audits are not events you prepare for — they're events you should already be prepared for. Whether it's an ISO 27001 certification audit, a SOC 2 Type II examination, a regulatory inspection, a financial audit, or a litigation discovery request, the underlying question is the same: can you produce evidence that your documents were managed properly? Who accessed them, when, under what authority? Were they encrypted? Were they retained for the required period? Were they disposed of lawfully? And can you prove all of this with contemporaneous records — not reconstructed narratives?
Most organisations discover the gaps in their document management evidence when the auditor asks for it. Access logs are incomplete or stored in a system the organisation doesn't control. Retention evidence is a spreadsheet maintained by someone who left the company. Encryption is claimed but the key management evidence is in a vendor's environment. The result is weeks of audit preparation, emergency evidence gathering, and qualified findings that could have been avoided.
FormKiQ produces audit evidence continuously, automatically, and within your own AWS account. Every document access, modification, workflow transition, approval decision, retention event, and disposition action is logged with timestamps and actor identification in infrastructure you own. CloudTrail records infrastructure-level events. FormKiQ's document audit trail records document-level events. KMS records encryption key usage. CloudWatch records availability and operational metrics. When auditors arrive, the evidence is already there — produced by the platform's normal operation, not assembled after the fact.
What Makes Document Management "Audit-Ready"?
Audit readiness is not a feature — it's a property of how the system operates. A document management platform is audit-ready when it produces the evidence auditors need as a byproduct of its normal operation, without requiring manual evidence collection, screenshot gathering, or report generation before an audit.
| Audit-Ready Property | What It Means | How FormKiQ Delivers It |
|---|---|---|
| Continuous evidence | Audit evidence produced in real time, not assembled retrospectively | CloudTrail, FormKiQ audit trail, and KMS logs operate continuously within your AWS account |
| Infrastructure ownership | Audit evidence stored in infrastructure you own and can query directly | All logs, metrics, and audit records in your AWS account — not in a vendor's |
| Tamper evidence | Audit logs protected from modification or deletion | CloudTrail log file integrity validation; S3 versioning; KMS-encrypted log storage |
| Completeness | Every relevant event recorded — no gaps in coverage | Document-level audit trail captures every access, modification, and lifecycle event |
| Granularity | Evidence at the level of detail auditors require — who, what, when, where, why | User identity, action type, document identifier, timestamp, source IP, and session context |
| Retention | Audit evidence retained for the period auditors examine | Configurable audit log retention independent of document retention |
| Queryability | Evidence searchable and filterable — not just raw log files | CloudTrail Lake, CloudWatch Logs Insights, and FormKiQ's API enable structured queries across audit data |
The Five Evidence Categories
Auditors — regardless of framework — evaluate document management across five evidence categories. FormKiQ produces evidence in all five automatically.
1. Access Evidence
Access evidence answers: who accessed which documents, when, how, and under what authority?
| Evidence Element | Source in FormKiQ |
|---|---|
| User identification | Amazon Cognito user identity — unique per user, linked to SSO provider identity |
| Document identification | FormKiQ document ID, document type, classification metadata |
| Action type | View, download, modify, delete, classify, approve, reject, distribute |
| Timestamp | ISO 8601 timestamp with timezone — from AWS infrastructure clock |
| Access method | API call, web console, integration framework — recorded in CloudTrail |
| Access policy | ABAC policy that permitted the access — documented in the access control configuration |
Access evidence is the single most requested evidence category across all audit frameworks. With FormKiQ, it's produced automatically for every document interaction — not sampled, not estimated, not reconstructed from email threads.
2. Encryption Evidence
Encryption evidence answers: is data encrypted at rest and in transit, and who controls the encryption keys?
| Evidence Element | Source in FormKiQ |
|---|---|
| Encryption at rest | S3 server-side encryption with KMS customer-managed keys — verifiable in S3 bucket configuration |
| Encryption in transit | TLS for all API and console communication — verifiable in API gateway and CloudFront configuration |
| Key management | KMS key configuration, key policies, and key rotation schedule — in your AWS account |
| Key usage | KMS key usage logs — every encrypt/decrypt operation recorded with timestamp and requesting service |
| Key access control | KMS key policies restricting which services and roles can use the key — auditable in your KMS configuration |
Unlike vendor-hosted platforms where encryption is claimed but key management is opaque, FormKiQ's encryption evidence is in your KMS — auditors can examine key configuration, key policies, and key usage logs directly.
3. Change Management Evidence
Change management evidence answers: how are system changes controlled, authorised, and tracked?
| Evidence Element | Source in FormKiQ |
|---|---|
| Infrastructure changes | CloudFormation stack events — every deployment, update, and configuration change recorded |
| Configuration changes | CloudTrail API events — every configuration change to FormKiQ, Cognito, S3, DynamoDB, and other services |
| Document changes | FormKiQ version control — every document modification creates a new version with before/after state |
| Access control changes | CloudTrail and FormKiQ audit trail — every change to access policies recorded with prior and new state |
| Deployment history | CloudFormation stack history — complete record of every deployment with template version and parameters |
4. Retention and Disposition Evidence
Retention evidence answers: were documents retained for the required period and disposed of lawfully?
| Evidence Element | Source in FormKiQ |
|---|---|
| Retention policy | Configurable retention policies documented within FormKiQ — applicable policy recorded per document |
| Retention period served | Document creation/trigger date and disposition date — proving the retention period was served in full |
| Legal hold status | Hold application and release records — proving no active hold existed at the time of disposition |
| Disposition authorisation | Authorising actor and approval workflow evidence — proving disposition was authorised |
| Disposition confirmation | Audit-logged disposition event with document identifier, action, policy, timestamp, and actor |
5. Availability and Operational Evidence
Availability evidence answers: was the system available and operating correctly during the audit period?
| Evidence Element | Source in FormKiQ |
|---|---|
| System availability | CloudWatch metrics — uptime, error rates, latency, and service health |
| Monitoring and alerting | CloudWatch alarms — configured thresholds, triggered alerts, and response records |
| Incident records | Incident documentation within FormKiQ — incident reports, root cause analyses, remediation evidence |
| Recovery capability | CloudFormation reproducible deployment; S3 versioning; multi-AZ architecture |
| Capacity management | AWS serverless auto-scaling — Lambda, DynamoDB, and S3 scale automatically without capacity planning |
Audit-Ready by Framework
Different audit frameworks emphasise different evidence categories. FormKiQ's continuous evidence production supports all of them from the same evidence base:
| Framework | Primary Evidence Focus | FormKiQ Evidence Sources |
|---|---|---|
| ISO 27001 | Controlled documented information, access controls, risk treatment, internal audit, management review | Document audit trail, version control, ABAC policies, workflow records |
| SOC 2 Type II | Continuous control operation over the audit period — access, encryption, change management, monitoring | CloudTrail, KMS logs, CloudWatch, FormKiQ audit trail — all continuous |
| HIPAA | PHI access controls, audit controls, integrity controls, encryption | ABAC policies, document-level audit trail, KMS encryption, version control |
| GDPR / UK GDPR | Processing records, data subject rights fulfilment, retention enforcement, data protection measures | Processing audit trails, rights request workflows, retention records, encryption evidence |
| ISO 9001 | Document control, quality records, internal audit, corrective actions | Version control, approval workflows, audit records, corrective action tracking |
| Financial audit | Transaction documentation, authorisation evidence, segregation of duties, retention compliance | Approval workflows, access controls, document-level audit trail, retention records |
| Regulatory examination | Compliance evidence, record-keeping, access controls, retention, correspondence | Full evidence base — all five categories applicable |
The Evidence Ownership Advantage
The most significant difference between audit-ready document management on AWS and audit-ready claims from vendor-hosted platforms is evidence ownership.
When your document management runs in a vendor's environment, audit evidence is the vendor's to produce. You request access logs — the vendor generates a report. You need encryption proof — the vendor provides their SOC 2 report. You need retention evidence — the vendor produces their compliance documentation. At every step, you depend on the vendor's willingness, timeliness, and accuracy.
When your document management runs in your own AWS account via FormKiQ, audit evidence is yours:
In a vendor-hosted platform
- Request access logs — vendor generates a report
- Need encryption proof — vendor provides their SOC 2 report
- Need retention evidence — vendor produces their compliance documentation
- Auditors read a report about a vendor's infrastructure
In FormKiQ on your AWS account
- Access logs are in your CloudTrail — query with CloudTrail Lake or export to your SIEM
- Encryption evidence is in your KMS — show auditors key configuration, policies, and usage logs
- Change management evidence is in your CloudFormation — walk auditors through deployment history
- Auditors examine your infrastructure directly

FormKiQ Editions for Audit-Ready Document Management
| Capability | Core Foundation |
Essentials Operational |
Advanced AI + Automation |
Enterprise Full platform |
|---|
Getting Started
FormKiQ Core can be deployed to your AWS account in fifteen to twenty minutes. Audit-ready capabilities — including KMS encryption, ABAC, document-level audit trails, versioning, and workflow approval tracking — are available from Essentials onward.
Frequently Asked Questions
What does "audit-ready" mean for document management?
Audit-ready means the document management platform produces the evidence auditors need — access logs, encryption proof, retention records, change history, and availability metrics — continuously and automatically as part of its normal operation. No manual evidence collection, screenshot gathering, or report generation is required before an audit. The evidence is always current because it's produced by the platform's operation, not assembled after the fact.
How is audit readiness different when FormKiQ runs in my own AWS account?
When FormKiQ runs in your AWS account, audit evidence is in infrastructure you own — CloudTrail, KMS, CloudWatch, and FormKiQ's audit trail. Your auditors examine your infrastructure directly. With a vendor-hosted platform, you depend on the vendor to produce evidence from their infrastructure — typically through their SOC 2 report, which covers their controls and their environment, not yours.
What audit frameworks does FormKiQ support?
FormKiQ's continuous evidence production supports ISO 27001, SOC 2, HIPAA, GDPR/UK GDPR, ISO 9001, financial audits, and regulatory examinations. The same evidence base — access logs, encryption records, change history, retention records, and operational metrics — serves all of these frameworks because the underlying evidence requirements are consistent across frameworks.
How long is audit evidence retained?
Audit log retention is configurable independently of document retention. CloudTrail logs, FormKiQ audit trail entries, and KMS usage logs can each be retained for the period your audit framework requires — typically covering at least the current and prior audit periods. For SOC 2 Type II, this means evidence covering the full audit observation period.
Can auditors access FormKiQ directly?
Yes. FormKiQ's ABAC model supports auditor access — time-limited, read-only access scoped to the documents and audit evidence within the audit scope. All auditor access events are recorded in the audit trail. External auditors (certification bodies, regulatory examiners, financial auditors) can be granted temporary access without requiring permanent user accounts.