Guide contents
Business Solution Guide
Claims Management on AWS
Multi-channel intake, evidence handling, adjudication correspondence, and audit trails on AWS infrastructure you control.
Claims processing is one of the most document-intensive operations in insurance, government benefits, healthcare, and workers' compensation. Every claim generates a cascade of documents — intake forms, supporting evidence, medical records, police reports, adjuster assessments, correspondence with claimants, denial or approval letters, and appeals documentation — yet in most organizations, these documents are scattered across intake portals, email, imaging systems, and legacy claims platforms with no unified way to manage the full evidentiary record, track adjudication status, or demonstrate defensible decision-making.
FormKiQ's Claims Management solution provides the document layer for the full claims lifecycle — from initial notice of loss through evidence collection, assessment, adjudication, correspondence, payment authorization, and retention — deployed directly into your AWS account. AI-powered claims document analysis using Amazon Bedrock classifies incoming evidence, extracts key data from unstructured claim documents, identifies coverage-relevant information, and flags inconsistencies for adjuster review. Workflow automation routes claim documents through assessment and approval chains. And the entire claims record — every document, every version, every decision — is stored, encrypted, and auditable within your own AWS environment.

The Claims Document Lifecycle
FormKiQ supports each stage of the claims document lifecycle within a governed, auditable platform:
| Stage | What Happens | How FormKiQ Handles It |
|---|---|---|
| First Notice | A claim is initiated through web portal, email, phone transcript, mail, or agent submission | Multi-channel intake via API, email connector, web upload, or scanned document — each submission registered with receipt timestamp, channel metadata, and claimant reference |
| Evidence Collection | Supporting documents are gathered — photos, medical records, police reports, receipts, statements, expert assessments | Document upload with classification, tagging by evidence type, and association to the claim file — with OCR and AI extraction for unstructured documents |
| Assessment | Adjusters and subject matter experts review the evidence and evaluate the claim | Claim file view with all associated documents, AI-extracted metadata, and structured assessment forms — with workflow-driven task assignment to adjusters |
| Adjudication | A coverage determination is made — approve, deny, or request additional information | Decision workflow with approval chains, role-based authorization, decision metadata (outcome, rationale, coverage references), and decision letter generation |
| Correspondence | Letters, notices, and communications are exchanged with the claimant | Document Generation produces determination letters, request-for-information notices, and status updates from governed templates — with dispatch tracking and audit trail |
| Appeal | The claimant disputes the determination and submits additional evidence | Appeal intake linked to the original claim file, with the full evidentiary record and original decision accessible to the appeal reviewer |
| Payment Authorization | Approved claims are authorized for payment | Payment authorization metadata applied to the claim record, linked to ERP/financial systems through Integration Framework |
| Retention & Archive | Closed claims are retained according to regulatory and organizational policy | Configurable retention policies by claim type, line of business, and jurisdiction — with legal hold and defensible disposition |
AI-Powered Claims Document Analysis with Amazon Bedrock
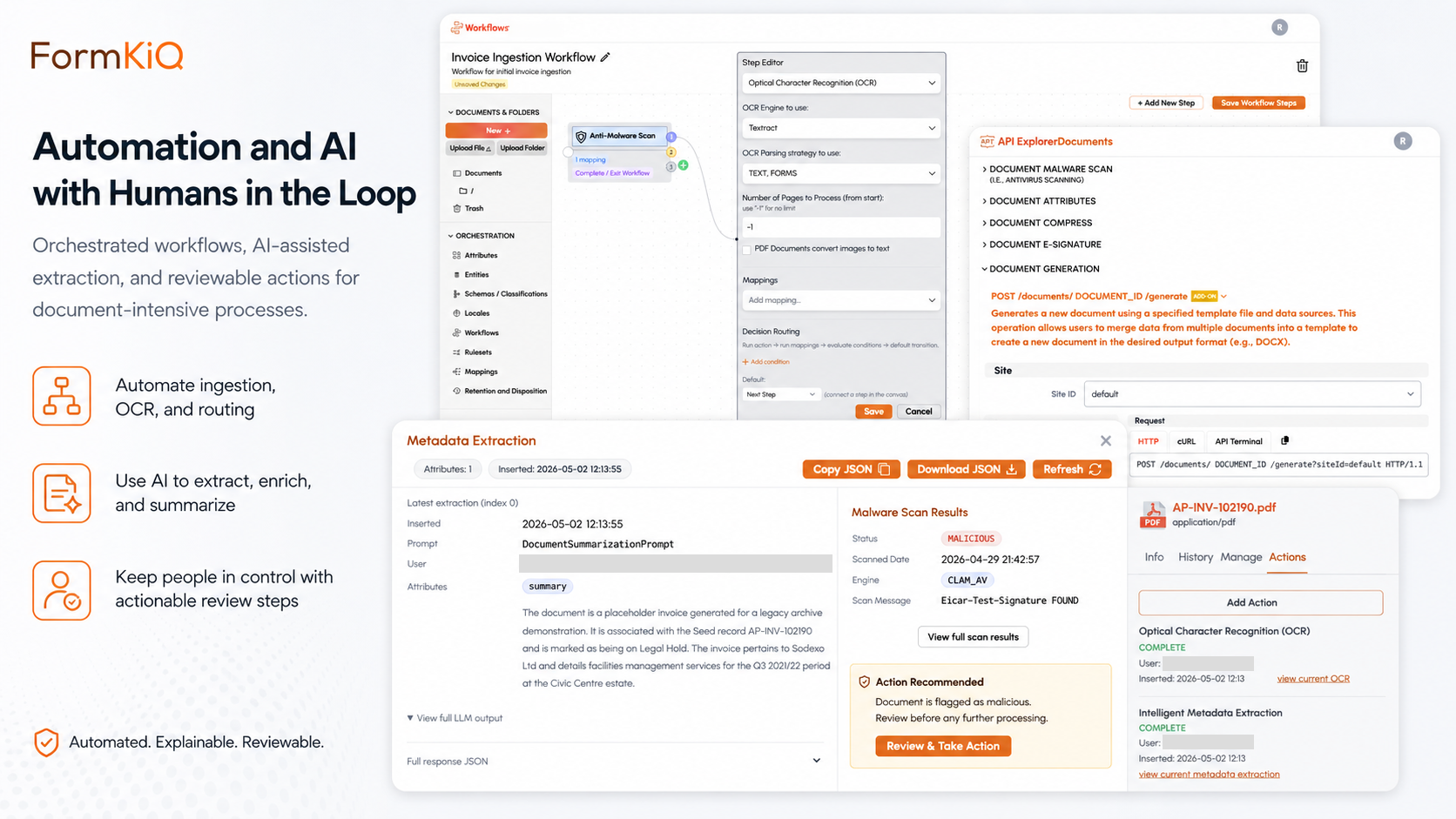
Traditional claims processing requires manual document review — adjusters read each submission, classify evidence, extract key data, and identify relevant facts. FormKiQ's AI Processing and Analysis module — powered by Amazon Bedrock — automates document-level analysis, turning unstructured claim submissions into classified, enriched, actionable records.
All AI processing runs within your AWS account through Amazon Bedrock, using supported large language models including Anthropic Claude, Amazon Nova, and other available models. Your claims content never leaves your cloud environment. Inference region controls allow you to specify which AWS regions are used for model processing, ensuring claims data stays within the geographic boundaries required by your data residency and regulatory program.
What Bedrock Extracts from Claims Documents
| Extraction Type | What It Captures | How It's Used |
|---|---|---|
| Document Classification | Evidence type — medical record, police report, repair estimate, receipt, witness statement, expert assessment, correspondence, legal notice | Classification metadata drives routing, adjuster assignment, and evidence-completeness checks |
| Key Entities | Claimant identity, policy number, date of loss, location, involved parties, provider names, claim amounts | Entity metadata enables cross-referencing against policy records, duplicate detection, and structured search |
| Coverage-Relevant Facts | Injury descriptions, property damage assessments, treatment summaries, repair scopes, cause-of-loss indicators | Extracted facts presented to adjusters as structured summaries alongside the source document for verification |
| Monetary Values | Claimed amounts, billed amounts, repair estimates, medical charges, settlement figures | Financial metadata applied to the claim record for aggregate reporting and threshold-based workflow triggers |
| Inconsistency Indicators | Conflicting dates, mismatched amounts, discrepancies between statements and evidence, unusual patterns | Flagged for adjuster review with confidence scoring — low-confidence extractions and potential inconsistencies routed to a review queue |
How AI Claims Document Analysis Works in FormKiQ
Document intake
A claim document is received via portal upload, email connector, API submission, or scanned mail
AI processing trigger
A document action triggers Amazon Bedrock analysis based on the document's intake channel or claim type
Classification and extraction
Bedrock classifies the document by evidence type and extracts key entities, coverage-relevant facts, monetary values, and inconsistency indicators
Metadata application
Extracted data is applied to the document record as structured metadata, making it searchable and actionable within the claim file
Claim file enrichment
Extracted metadata is aggregated at the claim level, enabling adjusters to view a structured summary of all evidence received
Routing and assignment
Workflow rules use document classification and claim metadata to route items to the appropriate adjuster or specialist queue
Human review
Low-confidence extractions and flagged inconsistencies are routed to a review queue for adjuster verification. AI analysis can be applied selectively — to specific document types, lines of business, or intake channels — rather than uniformly across all claim submissions.
Document Generation for Claims Correspondence
FormKiQ's Document Generation module eliminates manual letter assembly by producing claims correspondence from governed templates with data drawn from claim metadata, policy records, and adjudication decisions.
How Claims Document Generation Works
| Step | What Happens |
|---|---|
| Template definition | Claims operations and compliance teams define correspondence templates — determination letters, request-for-information notices, acknowledgment letters, status updates, appeal response letters — with standard language and variable fields |
| Data input | Variable fields are populated from claim metadata, policy records, adjudication decisions, and claimant information |
| Document production | The Document Generation module produces a formatted correspondence document from the template and data inputs |
| Governed storage | The generated document is stored in FormKiQ within the claim file with full metadata, version history, and audit trail |
| Workflow routing | The generated document is automatically routed into the review and approval workflow — and then to dispatch |
What This Replaces
Manual letter drafting with inconsistent language across adjusters
Copy-paste from previous correspondence with outdated or incorrect terms
Determination letters created outside the claims record and never properly associated with the claim file
Inconsistent regulatory language across jurisdictions and lines of business
Claims Metadata and Search
FormKiQ's metadata architecture provides structured classification for claims records:
| Category | Example Fields |
|---|---|
| Claim identity | Claim number, policy number, claim type (property, casualty, liability, medical, workers' comp, disability) |
| Parties | Claimant name, claimant contact, policyholder, adjuster, supervisor, legal counsel |
| Incident | Date of loss, location, cause of loss, incident description, police report number |
| Financial | Claimed amount, reserve amount, paid amount, outstanding amount, deductible |
| Classification | Line of business, jurisdiction, coverage type, complexity tier, litigation status |
| Status | Open, under assessment, pending information, adjudicated (approved/denied), in appeal, closed, reopened |
| Evidence | Evidence checklist status (medical records received, police report received, estimates received, statements received) |
All metadata fields are searchable through FormKiQ's full-text and metadata search — enabling queries such as:
- All open claims above a specified reserve threshold
- All claims pending additional information beyond a defined age
- All claims in a specific jurisdiction with a specific cause of loss
- All denied claims currently under appeal
- All claims under legal hold or in litigation
- All claims assigned to a specific adjuster with approaching deadlines
Integration with Enterprise Systems
FormKiQ's Integration Framework Modules connect claims document management to the enterprise systems where claims data originates and is consumed:
Claims Platform / Policy Admin
Claim documents linked to claim and policy records in the core claims or policy administration system — document status and AI-extracted metadata synchronized with the claims platform
ERP / Financial
Payment authorization documents linked to accounts payable — reserve and payment metadata synchronized for financial reporting
CRM / Customer Service
Claimant correspondence linked to customer records — claims status visible from the customer service view for inquiry handling
FormKiQ Editions for Claims Management
Claims Management is available as a Solution Layer on FormKiQ Advanced and Enterprise. The modules that power claims document management — AI Processing and Analysis, Document Generation, and Integration Frameworks — are Capability Extension Modules available on Advanced and Enterprise editions.
| Capability | Core Foundation |
Essentials Operational |
Advanced AI + Automation |
Enterprise Full platform |
|---|---|---|---|---|
| Foundation | ||||
| Document Storage, API & Web Console | ||||
| Tagging, Search & Classification | ||||
| OCR (Tesseract) & Multi-Tenant Support | ||||
| Essentials and above | ||||
| SSO (SAML — Entra, Google, Auth0) | — | |||
| Workflows, Queues & Rulesets | — | |||
| Encryption (in-transit & at-rest) & Document Control | — | |||
| Advanced and Enterprise | ||||
| AI Processing & Analysis (Bedrock) | — | — | ||
| Document Generation | — | — | ||
| Integration Frameworks (Claims, ERP, CRM) | — | — | ||
| Solution Layers (Claims Management) | — | — | ||
| Multi-Instance & Multi-Region Licensing | — | — | ||
| Enterprise only | ||||
| Vendor-Managed & Hybrid Deployment | — | — | — | |
| Custom SLAs & Compliance Consulting | — | — | — | |
| Support | ||||
| Support tier | Community (Slack & GitHub) | Support Portal (2-biz-day SLA) | Private Slack + videoconference + 40 hrs onboarding | Rapid response (8-biz-hr SLA) + strategic architecture support |
Compliance and Regulatory Alignment for Claims
| Framework | Claims-Specific Requirements | FormKiQ Capabilities |
|---|---|---|
| State Insurance Regulations (US) | Claims documentation retention, timely response requirements, unfair claims practices statutes | Configurable retention schedules by claim type and jurisdiction · Deadline tracking · Audit trails |
| NAIC Model Laws (US) | Model Unfair Claims Settlement Practices Act — documentation of claim handling decisions | Immutable audit trails · Decision metadata · Correspondence history |
| GDPR / UK GDPR | Claims containing personal data must be processed lawfully with rights of access, rectification, and erasure | Data residency enforcement · Retention controls · Deletion workflows · ABAC |
| HIPAA | Claims involving protected health information (medical records, treatment summaries) require safeguards | KMS encryption · ABAC · Audit trails · BAA-eligible AWS services |
| Workers' Compensation Statutes | Jurisdiction-specific documentation, retention, and reporting requirements | Configurable retention and reporting metadata by jurisdiction · Audit trails |
| OSFI / ICA (Canada) | Insurance regulatory requirements for claims documentation and retention | Regional deployment (ca-central-1) · Retention enforcement · Audit trails |
| FCA / PRA (UK) | Financial Conduct Authority and Prudential Regulation Authority requirements for claims handling and complaints | Audit trails · Complaint-handling workflow support · Retention enforcement |
| Solvency II (EU) | Documentation requirements for claims provisioning and reserving | Retention enforcement · Audit trails · Access controls |
Whether a FormKiQ deployment satisfies any specific framework depends on configuration and must be validated by your legal and compliance teams.
Who Uses Claims Management on AWS
Property & Casualty Insurance
Claims types
Property damage, liability, auto, homeowners, commercial, specialty
Key drivers
State insurance regulations, NAIC model laws, audit readiness, data residency
Health Insurance
Claims types
Medical claims, dental claims, pharmacy claims, behavioral health
Key drivers
HIPAA, state insurance regulations, CMS requirements
Life & Disability Insurance
Claims types
Life claims, short-term disability, long-term disability, AD&D
Key drivers
State insurance regulations, ERISA (employer-sponsored), audit readiness
Workers' Compensation
Claims types
Workplace injury claims, occupational disease claims, return-to-work documentation
Key drivers
State workers' compensation statutes, OSHA recordkeeping
Government Benefits
Claims types
Social benefits claims, veterans' benefits, disability benefits, unemployment insurance
Key drivers
Federal and state/provincial program regulations, audit readiness, data residency
Reinsurance & Self-Insured
Claims types
Treaty and facultative claims, self-funded health plan claims, general liability, property claims
Key drivers
Reinsurance contract terms, ERISA (health plans), internal governance, audit requirements
Deployment Models
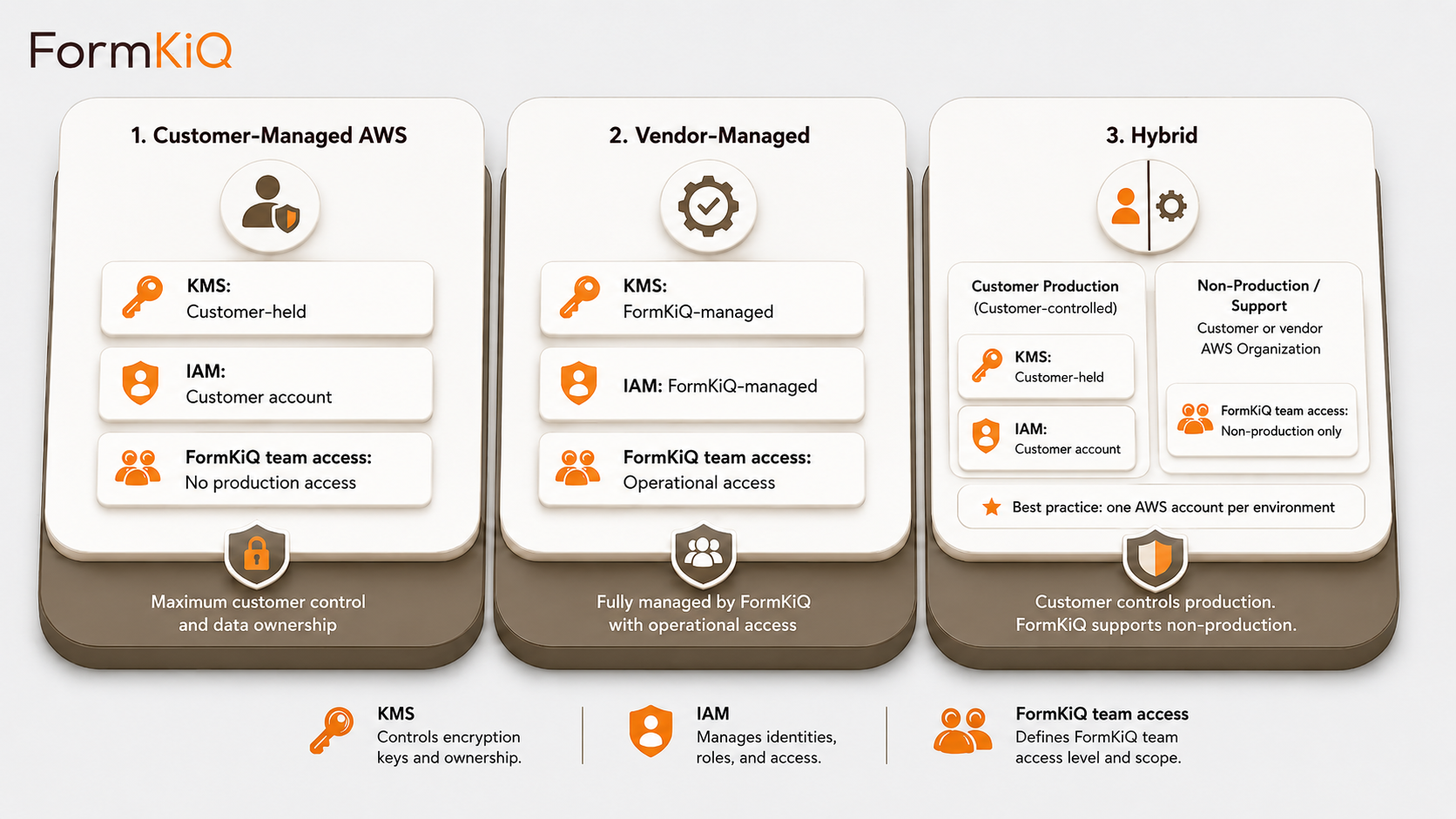
Every deployment is a dedicated, isolated instance in an AWS account owned by or designated by the customer. FormKiQ does not operate a shared multi-tenant environment.
- Customer-Managed AWS — deploys directly into your AWS account via CloudFormation; full control of infrastructure, networking, encryption keys, and operations; available on all editions
- Vendor-Managed — FormKiQ manages the AWS infrastructure on your behalf; available on Enterprise
- Hybrid — you retain control of specific components while delegating operational management to FormKiQ; available on Enterprise
Getting Started
FormKiQ Core can be deployed to your AWS account in fifteen to twenty minutes using a one-click install via AWS CloudFormation. Claims Management capabilities — including AI Processing and Analysis, Document Generation, and Integration Frameworks — are available on FormKiQ Advanced and Enterprise.
For organizations evaluating claims document management on AWS, FormKiQ offers a Proof-of-Value program — a three-month deployment in a FormKiQ-managed AWS environment that provides full platform access in a non-production setting.
Start with FormKiQ Core
The open-source foundation — API-first, deployable into your own AWS account, and free to use. Right for architecture validation and early implementation.
Get Started Free →Deploy Advanced or Enterprise
Production-ready editions with AI Processing, Document Generation, and Integration Frameworks. Start with a Proof-of-Value deployment or go straight to production.
Explore Options →Frequently Asked Questions
What is claims management on AWS?
Claims management on AWS refers to managing the document layer of the claims lifecycle — intake, evidence collection, assessment, adjudication, correspondence, and retention — on a platform deployed within your own Amazon Web Services environment. This gives organizations full control over claims data, encryption, access, and audit trails without depending on a vendor-hosted claims document platform.
How does FormKiQ use Amazon Bedrock for claims document analysis?
FormKiQ's AI Processing and Analysis module uses Amazon Bedrock to analyze claims documents and extract structured data — document type, key entities, coverage-relevant facts, monetary values, and inconsistency indicators — automatically. All AI processing runs within your AWS account using Bedrock's supported large language models. Claims content never leaves your cloud environment, and inference region controls ensure processing stays within your data residency boundaries.
Does FormKiQ replace our core claims platform?
No. FormKiQ provides the governed document layer for claims — document storage, classification, evidence management, AI analysis, correspondence generation, and retention. It integrates with your existing claims platform or policy administration system through the Integration Framework, so claim documents are linked to claim and policy records while FormKiQ serves as the system of record for the governed document.
How does FormKiQ handle multi-channel claims intake?
FormKiQ accepts claim documents through multiple channels — web portal uploads, email connectors, API submissions, and scanned mail — each registered with receipt timestamp, channel metadata, and claimant reference. AI classification can be triggered automatically on intake to classify the document type and extract key data before routing to the appropriate adjuster or queue.
Can FormKiQ generate claims correspondence?
Yes. FormKiQ's Document Generation module produces determination letters, request-for-information notices, acknowledgment letters, and status updates from governed templates. Variable fields are populated from claim metadata, policy records, and adjudication decisions. Generated correspondence is stored within the claim file with full audit trail and routed through approval workflows before dispatch.
How does FormKiQ handle claims involving protected health information?
Claims documents containing PHI are encrypted at rest and in transit within your AWS account using KMS keys you control. Attribute-based access controls (ABAC) restrict access to PHI-classified documents based on user role, business unit, and document sensitivity. All access events are recorded in the audit trail. FormKiQ deploys on BAA-eligible AWS services.
Can FormKiQ track evidence completeness for a claim?
Yes. Claim files in FormKiQ carry evidence-checklist metadata — indicating which required evidence types have been received and which are outstanding. AI classification can automatically update the checklist when new documents are received and classified. Workflow rules can trigger request-for-information correspondence when required evidence has not been received within defined timeframes.