Customer-Managed Deployment Guide
Customer-Managed AWS Document Management
Full infrastructure ownership for document programs where control, sovereignty, and auditability are non-negotiable.
Customer-managed AWS deployment means FormKiQ runs entirely within your own AWS account — your data, your encryption keys, your IAM policies, and your operational boundary. No shared infrastructure, no vendor access to production unless you explicitly grant it, and no dependency on a third-party cloud environment for the governance of your most sensitive documents. For organizations where the deployment model itself is a compliance requirement, this is the architecture that makes the rest of the governance story possible.
Who it's for
Organizations where infrastructure control is a compliance requirement, a contractual obligation, or an internal security policy — not just a preference. This includes:
- Regulated organizations subject to frameworks that require demonstrable control over where data lives and who can access the infrastructure processing it — GDPR, HIPAA, PIPEDA, Quebec Law 25, KSA PDPL, SOC 2, ISO 27001, and others
- Government and public sector bodies with data sovereignty requirements that preclude vendor-managed infrastructure for sensitive document programs
- Financial services and insurance organizations where internal security policy or regulatory mandate prohibits third-party access to production document systems
- Healthcare organizations where HIPAA security rule requirements and internal risk management standards require ownership of the full technical safeguard stack
- Legal and professional services firms where client confidentiality obligations require that document infrastructure be operated within the client organization's own environment
- Technology and SaaS companies building regulated document management into their products and requiring infrastructure control as a condition of their own compliance posture
- Enterprise organizations with existing AWS environments who want FormKiQ to operate as a native component of their existing cloud infrastructure rather than a separate hosted service
When to use it
When the deployment model — who operates the infrastructure and who can access it — is itself a compliance or governance consideration. Specifically:
- When internal security policy, regulatory mandate, or contractual obligation requires that vendor personnel cannot access production document data
- When data sovereignty requirements specify that the operational entity controlling document infrastructure must be subject to the same jurisdiction as the data subjects
- When encryption key ownership must remain with the customer — with no vendor access to key material
- When audit and compliance programs require that document infrastructure be subject to the customer's own security tooling, monitoring, and incident response processes
- When existing AWS infrastructure investment, IAM governance, and cloud operations capability make operating FormKiQ within your own account the natural fit
- When procurement, security review, or legal processes require that a vendor's access to production systems be demonstrably zero
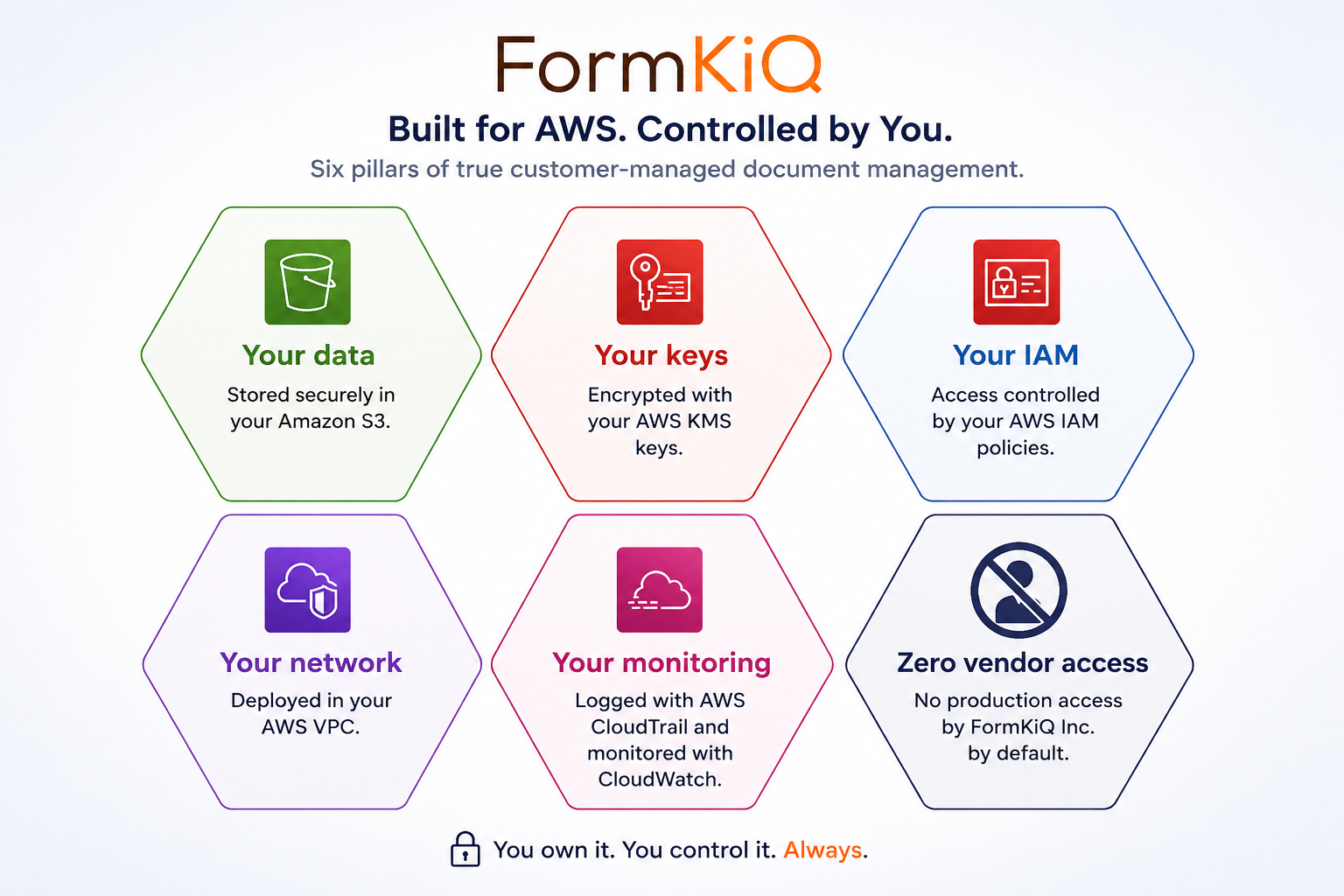
What customer-managed deployment means in practice
Customer-managed deployment is not simply a self-hosted option — it is a specific architectural commitment that FormKiQ is designed to fulfill. Every component of the FormKiQ platform — storage, metadata, search, processing, API, access control, and audit — deploys into your AWS account through AWS CloudFormation, using your account's resources, subject to your account's IAM policies, encryption configuration, and network controls.
Your data, in your account
Documents are stored in S3 buckets in your account. Metadata is stored in DynamoDB tables in your account. Search indexes are maintained in OpenSearch domains in your account. Processing functions run as Lambda functions in your account. Every byte of document content and metadata lives in infrastructure you own and control — not in a shared environment managed by FormKiQ.
Your encryption keys
All data at rest is encrypted using AWS KMS. In a customer-managed deployment, you control the KMS key configuration — whether using AWS-managed keys, customer-managed key stores, or AWS CloudHSM for hardware-level key isolation. FormKiQ has no access to your encryption keys, and cannot decrypt your data without your explicit authorization.
Your IAM policies
All access to FormKiQ's underlying AWS resources is governed by IAM policies in your account. You define who and what can access documents, metadata, processing functions, and administration interfaces — with no IAM policies controlled or modified by FormKiQ without your involvement.
Your network controls
FormKiQ can be deployed within your VPC, with private endpoints, controlled egress, and network security group configurations that reflect your organization's network security architecture. There is no requirement to expose FormKiQ components to public internet endpoints if your security architecture requires fully private deployment.
Your monitoring and audit tooling
CloudTrail, CloudWatch, AWS Security Hub, AWS Config, and GuardDuty all operate across FormKiQ's infrastructure in exactly the same way as they operate across the rest of your AWS environment — because FormKiQ's infrastructure is part of your AWS environment. Security monitoring, compliance checks, and audit log collection require no special configuration or vendor involvement.
Zero vendor access to production
The FormKiQ team has no access to your production environment unless you explicitly grant it. There is no vendor-side administration console, no support tunnel into production, and no FormKiQ-controlled access path to your documents, metadata, or infrastructure. If you choose to invite FormKiQ engineers into a support session, that access is granted and revoked by you, through your IAM configuration.
Compliance framework alignment
Customer-managed deployment directly addresses the infrastructure control dimension of the major regulatory frameworks. The table below maps each framework's relevant articles or controls to the specific customer-managed posture and the FormKiQ feature that supports it.
| Framework | Article / Control | Customer-Managed Control | FormKiQ Feature |
|---|---|---|---|
| GDPR / UK GDPR |
Art. 32 — Technical & organisational measures Art. 44–49 — Restrictions on international transfers |
Infrastructure in your own AWS account in EU or UK region; no third-party access to personal data without authorization | Regional deployment (eu-west-2, eu-central-1, eu-west-3 …) · Customer KMS · ABAC · Audit trail |
| HIPAA | §164.312 — Technical safeguards: access controls, audit controls, integrity, transmission security | Customer-owned IAM; customer-held KMS keys; zero vendor access to ePHI; all technical safeguards owned by covered entity | ABAC · CloudTrail audit log · KMS / CloudHSM · Zero vendor production access |
| Quebec Law 25 / PIPEDA |
Law 25 s.8 — Appropriate security measures PIPEDA Principle 7 — Safeguards |
Deployment in ca-central-1 (Montreal) or ca-west-1 (Calgary); Canadian personal data stays within Canadian infrastructure under customer control | Regional deployment (ca-central-1, ca-west-1) · Customer KMS · ABAC · Retention policies |
| KSA PDPL / GCC |
PDPL Art. 21 — Data localization Art. 29 — Security safeguards and cross-border transfer restrictions |
Deployment in me-central-1 (UAE) or me-south-1 (Bahrain); customer's own AWS account subject to local jurisdiction | Regional deployment (me-central-1, me-south-1) · Customer IAM · Encryption · Audit trail |
| SOC 2 / ISO 27001 |
SOC 2 CC6–CC9 — Logical access, availability, processing integrity ISO 27001 A.9, A.12, A.18 |
FormKiQ infrastructure included in customer's audit scope and ISMS boundary; existing AWS security controls apply directly | CloudTrail / CloudWatch in customer account · ABAC · KMS · Customer-owned audit logs |
| Internal Security Policy |
Zero third-party production access · Data sovereignty · Encryption key ownership requirements | No FormKiQ access to production by default; customer holds all encryption keys; all infrastructure in customer account | Zero vendor production access architecture · Customer-managed KMS · Customer IAM ownership |
Framework alignment depends on complete deployment configuration, operational practices, and validation by your legal, compliance, and security teams.
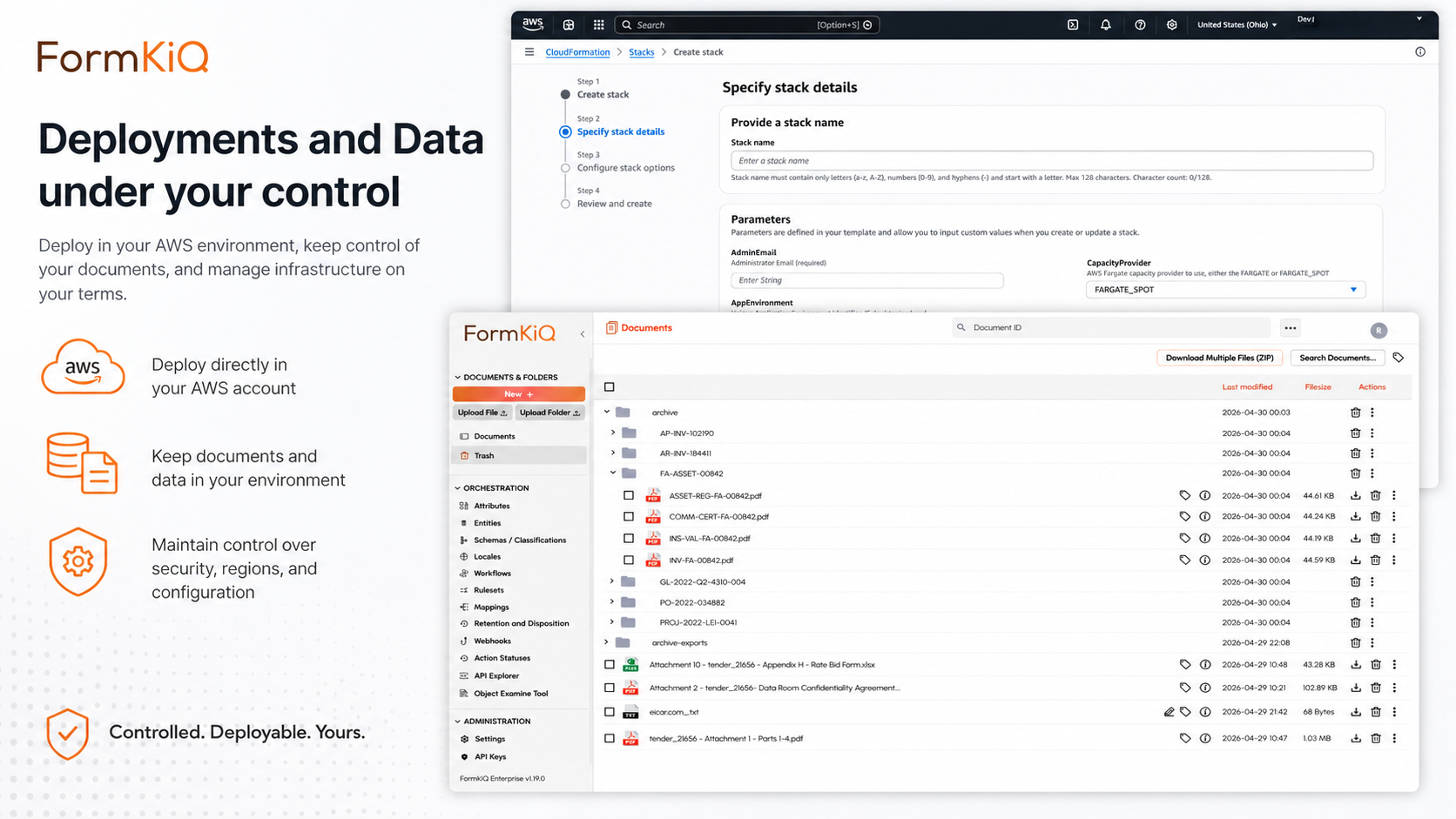
Deployment architecture
FormKiQ deploys via AWS CloudFormation — an infrastructure as code service that provisions all required AWS resources from a tested, versioned template. Deployment is repeatable, consistent, and auditable — the same template produces the same infrastructure every time, with no manual resource creation that could introduce configuration drift.

Core AWS services in a customer-managed FormKiQ deployment
Amazon S3 — document content storage, with versioning enabled for complete document history and protection against accidental overwrites and deletions
Amazon DynamoDB — document metadata storage, providing fast and cost-effective metadata search across collections of any size
AWS Lambda — serverless processing functions for document actions, workflow execution, OCR processing, AI processing, and integration logic
Amazon API Gateway — the secure API endpoint through which all FormKiQ API interactions are routed
Amazon Cognito — identity and access management for user authentication, group assignment, and multi-tenant isolation
AWS CloudFront — content delivery and TLS termination for the FormKiQ Document Console and API endpoints
AWS KMS — encryption key management for data at rest across S3, DynamoDB, and other services
Amazon SNS — document event publication for real-time notification of document lifecycle changes
Amazon OpenSearch — enhanced full-text search (available as an add-on module for Advanced and Enterprise)
Amazon Bedrock — AI processing and KnowledgeBase capabilities (available as add-on modules for Advanced and Enterprise)
AWS CloudTrail — audit logging of all API calls and resource operations across the FormKiQ deployment
Amazon CloudWatch — operational monitoring, logging, and alerting for FormKiQ components
Optional network configuration
- VPC deployment with private subnets for Lambda functions and other compute resources
- VPC endpoints for S3, DynamoDB, and other AWS services to eliminate internet-routed traffic
- Network security groups and NACLs configured to your network security architecture
- AWS WAF integration for API Gateway protection against web-based attacks
Regional deployment
Customer-managed deployment supports any AWS region where FormKiQ services are available — with twenty regions currently supported across North America, Europe, the Middle East, Asia-Pacific, Africa, and Latin America. Organizations with multi-jurisdiction operations can deploy separate FormKiQ instances per region, each within its own customer AWS account or organizational unit, with cross-region authentication but no cross-border data movement.
For organizations with complex multi-region requirements — separate instances per jurisdiction, cross-region authentication, and region-specific retention and access policies — FormKiQ's regional deployment model can be architected to support each jurisdiction's specific requirements within a consistent platform architecture.
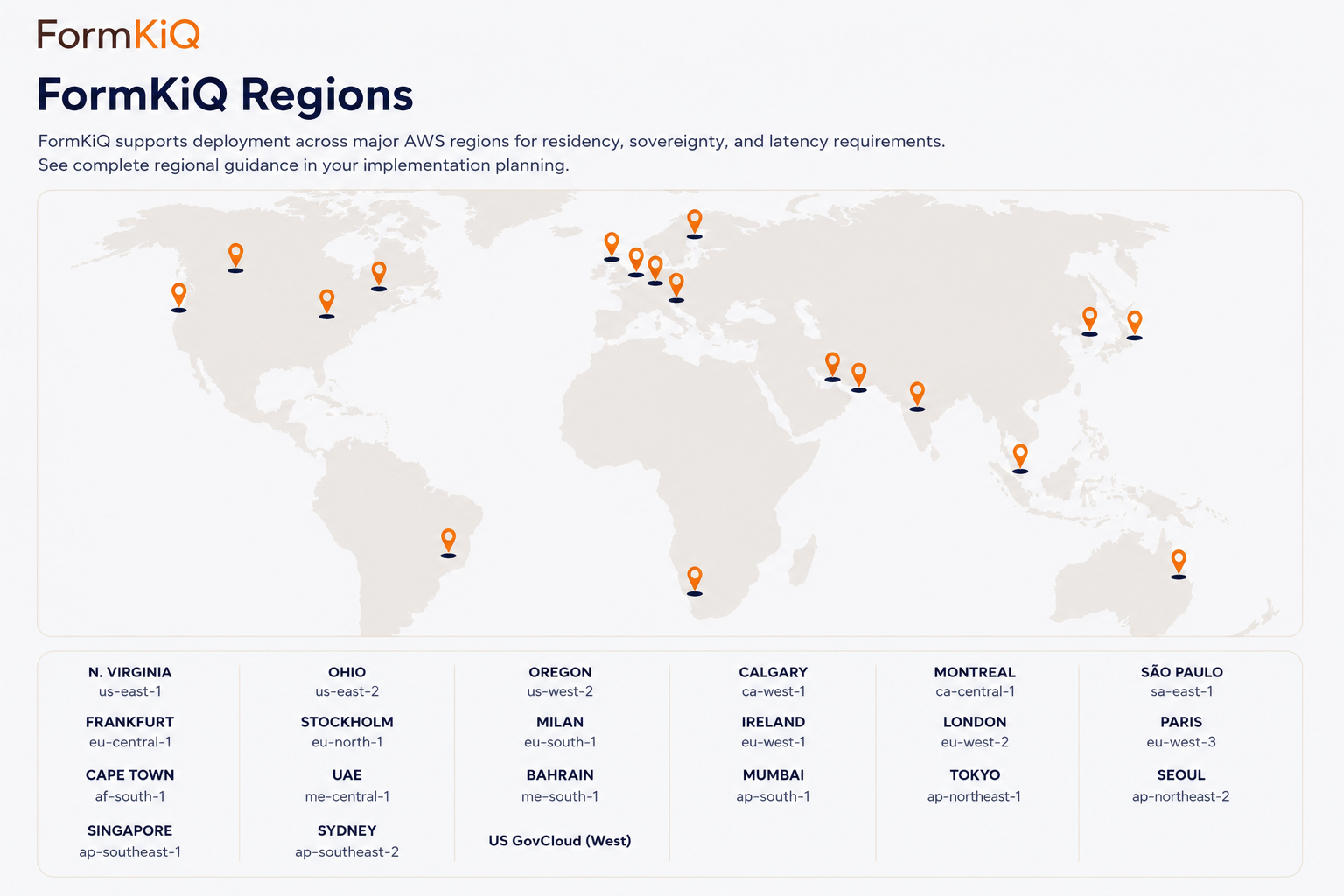
See the Data Residency page for the full list of supported AWS regions and their associated regulatory contexts.
Support model in customer-managed deployments
Customer-managed deployment does not mean unsupported deployment. FormKiQ's support model for Advanced and Enterprise customers includes Level 3 engineering support through the FormKiQ Support Portal, Private Slack Channel, and Videoconferencing — with FormKiQ engineers providing technical guidance, issue diagnosis, and resolution support without requiring access to your production environment.
For issues that benefit from direct access to your environment, FormKiQ engineers can be granted temporary, scoped access through your IAM configuration — at your discretion and revocable at any time. This model gives you complete control over when and how FormKiQ accesses your environment, while ensuring that engineering support is available when you need it.
For Enterprise customers, support structures can be customized to reflect the operational requirements of your deployment — including release coordination, change management processes, and compliance documentation support.
Migration to customer-managed deployment
For organizations moving from a legacy ECM platform or a vendor-managed document management service to customer-managed AWS deployment, FormKiQ supports phased migration that preserves existing workflows and business processes rather than requiring a forced redesign.
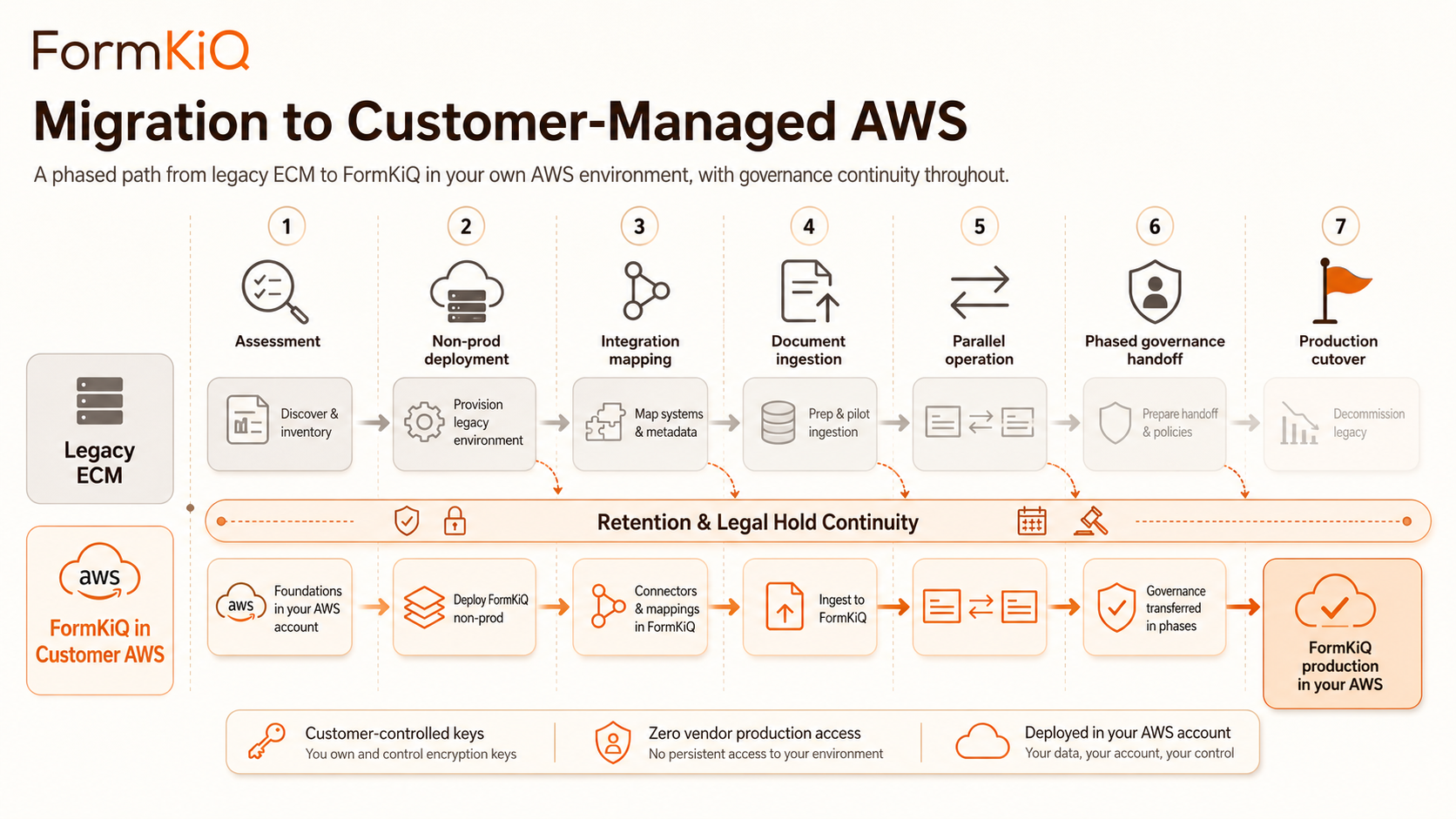
1. Assessment and planning
FormKiQ works with your architecture, legal, compliance, and operations teams to assess your current environment, document existing workflows and integrations, identify data residency and sovereignty requirements, and design a migration plan that maintains compliance continuity throughout.
2. Non-production deployment
FormKiQ is deployed in a non-production environment within your AWS account — allowing your team to validate the platform, test integrations, and build operational familiarity before production cutover. In a hybrid model, FormKiQ engineers can work directly in non-production environments to accelerate implementation while production remains in the existing system.
3. Integration mapping
Existing integrations with ERP, CRM, HRIS, case management, and other systems are mapped to FormKiQ API endpoints and Integration Framework configurations — identifying which connections can be re-pointed directly and which require adapter development.
4. Document ingestion
Documents are ingested from existing stores — legacy ECM platforms, file servers, cloud storage, or other sources — using FormKiQ's CLI, bulk upload capabilities, and Document Gateway modules. Metadata mapping ensures documents arrive in FormKiQ with governance context intact rather than as raw files requiring reclassification.
5. Parallel operation
FormKiQ runs alongside the existing system during the transition period — new documents and workflows move to FormKiQ incrementally while existing records remain accessible in place. Teams adopt the new environment at a pace that matches operational readiness.
6. Phased governance handoff
Governance functions — legal hold, retention management, audit trails, records disposition — are transitioned to FormKiQ in stages, with validation at each phase. Compliance continuity is maintained throughout, with no gap in audit readiness or records accessibility.
7. Production cutover
When the new environment has been validated and operational confidence is established, production traffic is redirected to the FormKiQ deployment and the legacy system is decommissioned or placed in read-only mode for historical reference.
Comparing deployment models
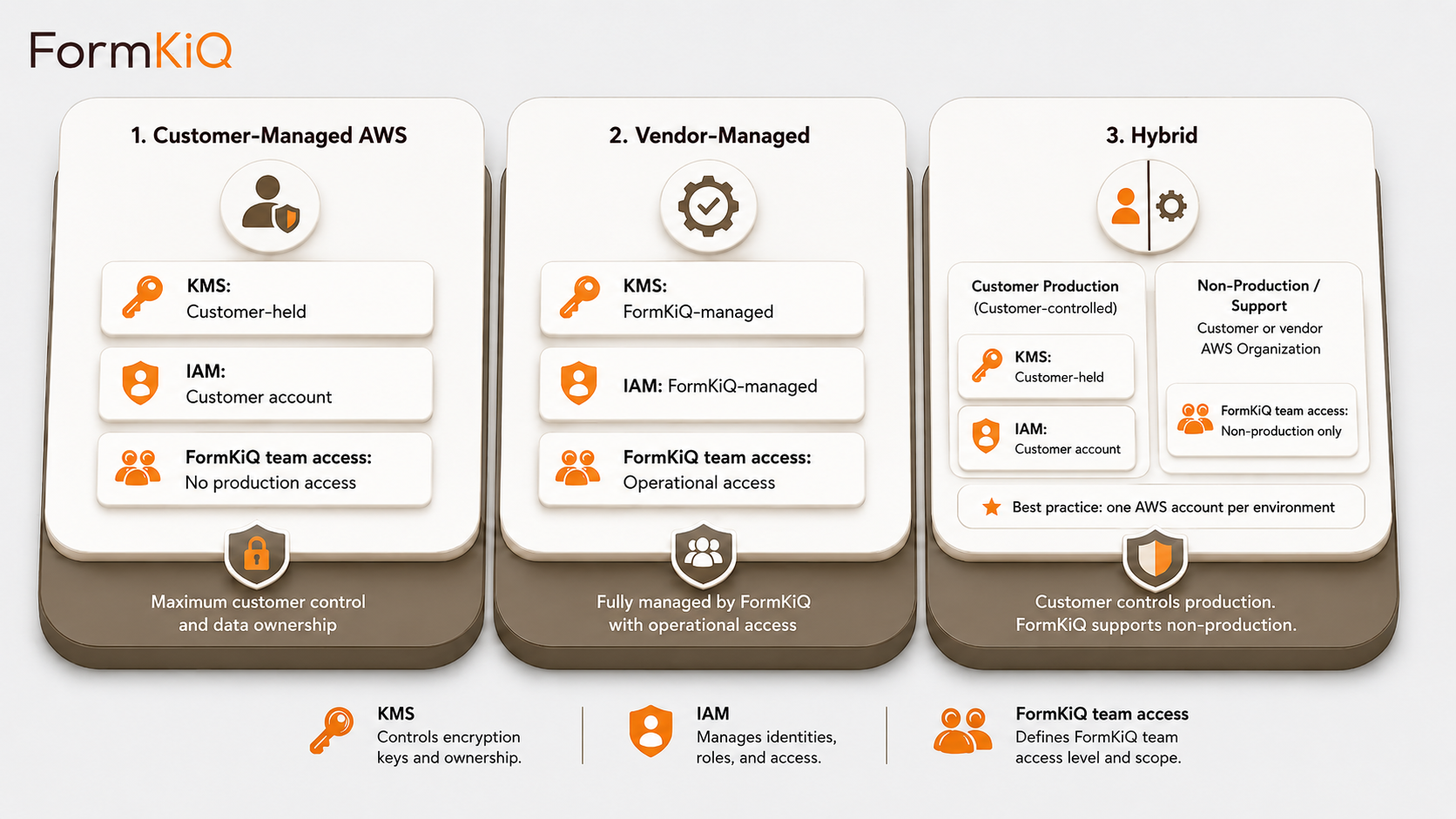
|
Customer-Managed
Maximum control
|
Vendor-Managed
Operational simplicity
|
Hybrid
Phased adoption
|
|
|---|---|---|---|
|
Infrastructure location
|
Your AWS account | Dedicated FormKiQ-hosted account | Split — production in your account |
|
FormKiQ production access
|
Zero unless granted | Operational access | Zero — non-production only |
|
Encryption key ownership
|
Customer | Shared / negotiated | Customer (production) |
|
IAM ownership
|
Customer | FormKiQ | Split |
|
Audit log destination
|
Customer-owned | FormKiQ-managed | Split |
|
Compliance validation
|
Customer | Shared | Customer |
|
AWS account
|
Your account | FormKiQ account | Your account (production) |
|
Best for
|
Maximum sovereignty and control | Fast start / operational simplicity | Phased adoption / migration support |
Important guardrail
Customer-managed deployment provides the infrastructure control posture that regulated document programs require — but infrastructure control alone does not constitute compliance with any specific regulatory framework. Whether a customer-managed FormKiQ deployment satisfies GDPR, HIPAA, SOC 2, Quebec Law 25, KSA PDPL, or any other framework depends on the complete configuration, operational practices, and governance controls applied to that deployment — which must be validated by your legal, compliance, and security teams. FormKiQ's architecture is designed to support that validation process, not to replace it.