Controlling Who Can Access, Modify, Classify, and Dispose of Documents — with Policy-Driven Enforcement and Complete Audit Trails on AWS
Document governance is the framework of policies, controls, and processes that determines how documents are managed throughout their lifecycle. It answers the questions that matter most to regulated organisations: who can access this document? Who approved it? Has it been modified since it was signed? How long must it be retained? Who is allowed to delete it? And can we prove all of the above to an auditor, regulator, or court?
Without governance, documents are just files. They sit in shared drives and email inboxes with no access controls beyond folder permissions, no version history beyond filename suffixes, no retention rules beyond "someone will clean this up eventually," and no audit trail beyond "I think Sarah emailed it to someone last quarter." The moment a regulator asks for proof that a document was handled properly, the organisation discovers that file storage is not document governance.
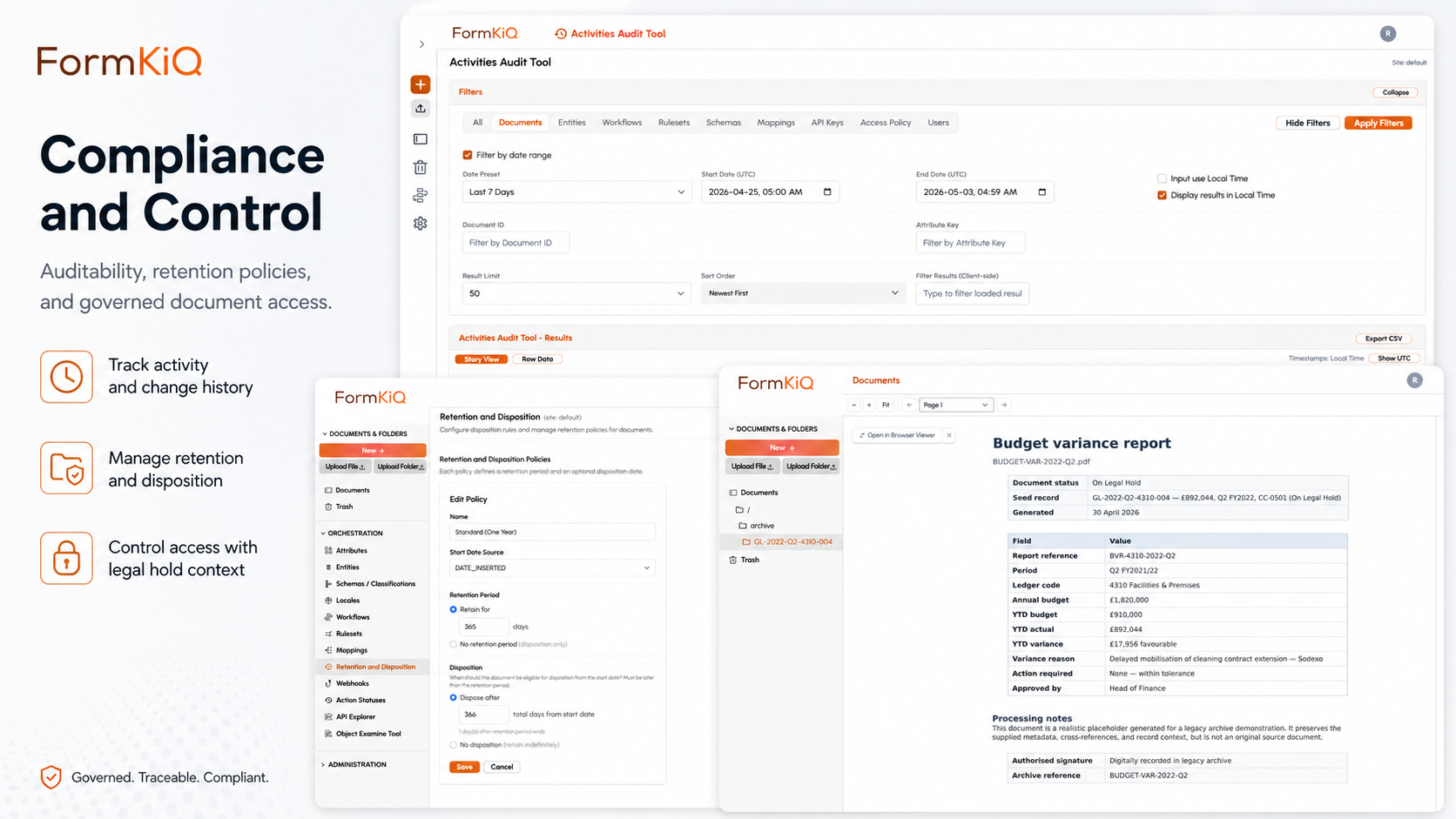
FormKiQ provides document governance as a foundational capability — not as a bolt-on module or a premium feature. Every document in FormKiQ is governed from the moment it enters the platform: classified with structured metadata, protected by attribute-based access controls, tracked by a document-level audit trail, and managed under configurable retention policies. And because FormKiQ deploys into your own AWS account, the governance infrastructure itself — the access policies, the encryption keys, the audit logs, the retention enforcement — is in your environment, under your control, and auditable by your team.
The Four Pillars of Document Governance
Document governance rests on four foundational pillars. Each must be in place for governance to be effective — and each must produce evidence that it's operating as designed.
1. Access Control
Access control determines who can see, modify, download, share, and delete documents. Effective governance requires access controls that operate at the document level — not just at the folder, repository, or system level.
| Access Control Approach | What It Controls | Governance Strength |
|---|---|---|
| System-level access | Who can log into the platform | Weakest — everyone with system access can see everything |
| Folder-level access | Who can access documents in a specific folder | Moderate — but documents in the wrong folder are exposed, and all documents in a folder share the same permissions |
| Role-based access control (RBAC) | Who can access documents based on their job role | Better — but static roles can't accommodate document-level sensitivity or contextual access needs |
| Attribute-based access control (ABAC) | Who can access documents based on document attributes, user attributes, and contextual conditions | Strongest — access decisions based on metadata values, enabling dynamic, fine-grained controls at the individual document level |
FormKiQ uses ABAC — document visibility is tied to metadata values (department, classification level, sensitivity, project, jurisdiction, or any custom attribute) combined with user attributes (role, department, location, clearance level). This means a single document collection can contain documents with different access rules: a patient file where clinical notes are visible to the care team but psychiatric records are restricted to the treating psychiatrist; a vendor file where contracts are visible to procurement but financial statements are restricted to the finance team.
2. Classification and Metadata
Classification is how governance rules are applied to documents. Without classification, governance is manual — someone has to look at each document and decide how to handle it. With structured classification, governance rules apply automatically based on what a document is, not where it happens to be stored.
FormKiQ's classification architecture includes:
- Tag schemas and composite keys — consistent metadata applied across document types, enabling governance rules to operate on metadata values rather than folder locations
- Document type definitions — templates that enforce required metadata fields when documents are created or ingested, ensuring every document is classified at the point of entry
- AI-powered classification — Amazon Bedrock automatically identifies document types, extracts entities, and applies sensitivity classifications at the point of ingestion, reducing manual classification burden and eliminating classification gaps
- Hierarchical and flat organisation — documents can be organised in folder structures, flat tag-based taxonomies, or composite approaches — classification is independent of organisation
3. Audit Trail
An audit trail is the evidentiary backbone of document governance. Without it, governance claims are assertions without proof. With it, every access, modification, classification change, and disposition event is recorded with the detail needed to satisfy auditors, regulators, and courts.
FormKiQ records audit events at two levels:
| Audit Level | What It Records | Where It's Stored |
|---|---|---|
| Infrastructure audit | API calls, authentication events, configuration changes, service interactions | AWS CloudTrail — in your AWS account |
| Document audit | Document access (view, download), modification, classification change, workflow transition, approval decision, retention event, disposition event | FormKiQ audit log — in your AWS account |
Both audit levels are stored within your AWS account, encrypted with your KMS keys, and retained per your audit log retention policy. When an auditor asks for proof that a specific document was accessed by a specific person on a specific date, the evidence is in your infrastructure — not in a vendor's.
4. Retention and Disposition
Retention and disposition complete the governance lifecycle. Retention policies determine how long documents must be kept; disposition policies determine what happens when the retention period ends. Without retention governance, organisations either keep everything forever (creating storage cost, legal risk, and eDiscovery burden) or delete things ad hoc (creating compliance risk and defensibility gaps).
FormKiQ provides:
- Configurable retention policies — applied at the document, folder, or document-type level with automatic enforcement
- Multiple retention triggers — retention clock starts from document creation, a business event (contract expiry, employee separation, case closure), or a metadata value change
- Legal hold — suspends normal disposition to preserve documents for litigation, investigation, or regulatory proceedings — overrides retention schedules
- Defensible disposition — audit-logged deletion with record of the document identifier, disposition action, applicable retention policy, timestamp, and authorising actor
- Permanent preservation — documents designated for permanent retention are protected from disposition indefinitely
Why Governance Requires Infrastructure Control
Document governance is only as trustworthy as the infrastructure it runs on. When governance controls — access policies, encryption keys, audit logs, retention enforcement — operate in a vendor-controlled environment, the organisation trusts the vendor to enforce them correctly and to produce evidence on request. This creates a dependency that weakens governance at exactly the moment it matters most: during audits, litigation, and regulatory proceedings.
| Governance Function | In a Vendor-Hosted Platform | In FormKiQ on Your AWS Account |
|---|---|---|
| Access policies | Defined in the vendor's platform; enforced by the vendor's code | Defined in Cognito/IAM and FormKiQ ABAC; enforced in your account; auditable by your team |
| Encryption | Keys managed by the vendor; you trust their key management practices | Keys managed in your KMS; you control key policies, rotation, and access |
| Audit logs | Stored in the vendor's infrastructure; you request access or reports | Stored in your CloudTrail and FormKiQ audit log; you query directly |
| Retention enforcement | Executed by the vendor's system; you trust their implementation | Executed within your account; you verify and audit the enforcement directly |
| Disposition evidence | Generated by the vendor's reporting tools | Generated within your audit trail; you own the disposition records |
Governance by Document Lifecycle Stage
Governance applies differently at each stage of the document lifecycle. The table below maps governance controls to lifecycle stages:
| Lifecycle Stage | Key Governance Questions | FormKiQ Controls |
|---|---|---|
| Creation / Ingestion | Is the document classified? Is required metadata captured? Is it scanned for malware? | Document type definitions enforce metadata; AI classification at ingestion; antivirus scanning |
| Active Use | Who can access it? Who has accessed it? Has it been modified? | ABAC access controls; document-level audit trail; version control with integrity verification |
| Review and Approval | Was the review process followed? Who approved it? When? | Configurable workflows with audit-logged approval decisions; role-based task assignment |
| Distribution | Who received it? Did they acknowledge it? | Distribution tracking; eSignature acknowledgment; delivery audit trail |
| Retention | How long must it be kept? What triggers the retention clock? Is it under legal hold? | Configurable retention policies; event-triggered retention; legal hold override |
| Disposition | Can it be disposed of? Who authorised it? Is there evidence? | Defensible disposition workflows; hold-check before deletion; audit-logged disposition |
Governance Frameworks and Standards
Document governance supports compliance with a wide range of regulatory and standards frameworks. The governance model doesn't change by framework — the same four pillars (access control, classification, audit trail, retention) serve all of them:
| Framework | What It Requires from Document Governance |
|---|---|
| ISO 15489 | Records lifecycle management — creation, classification, retention, disposition with audit evidence |
| ISO 27001 | Controlled documented information — version control, access control, review cycles, retention |
| SOC 2 | Access controls, audit logging, encryption, change management, retention for Trust Services Criteria |
| GDPR / UK GDPR | Data protection by design — access controls, retention limits, processing records, data subject rights |
| HIPAA | PHI safeguards — access controls, audit controls, integrity controls, encryption |
| PIPEDA | Personal information governance — consent, access controls, retention limits |
| ISO 9001 | Quality records — document control, version management, audit trails |
| DoD 5015.02 | Records management — declaration, classification, retention scheduling, disposition |
Document Governance in FormKiQ: Edition Capabilities
| Capability | Core Foundation |
Essentials Operational |
Advanced AI + Automation |
Enterprise Full platform |
|---|---|---|---|---|
| Foundation | ||||
| Document storage with metadata | ||||
| Tagging, search & classification | ||||
| OCR (Tesseract) | ||||
| Essentials and above | ||||
| OCR & IDP (Textract) | — | |||
| SSO (SAML) | — | |||
| Encryption (KMS — at rest & in transit) | — | |||
| Workflows, queues & rulesets | — | |||
| Document control & versioning | — | |||
| Antivirus & anti-malware | — | |||
| Advanced and Enterprise | ||||
| AI classification & sensitivity detection (Bedrock) | — | — | ||
| Enhanced full-text search (OpenSearch) | — | — | ||
| eSignature integration | — | — | ||
| Document Gateway Modules | — | — | ||
| Integration Framework Modules | — | — | ||
| Multi-instance & multi-region licensing | — | — | ||
| Enterprise only | ||||
| Vendor-managed & hybrid deployment | — | — | — | |
| Compliance consulting | — | — | — | |
| Support | ||||
| Support | Community | 2-business-day SLA | Private Slack + 40 hrs onboarding | 8-business-hour SLA + strategic support |
Getting Started
FormKiQ Core can be deployed to your AWS account in fifteen to twenty minutes using a one-click install via AWS CloudFormation. Document governance capabilities — including ABAC, encryption, versioning, workflows, and audit trails — are available from Essentials onward. AI-powered classification and sensitivity detection are available on Advanced and Enterprise.
Frequently Asked Questions
What is document governance?
Document governance is the framework of policies, controls, and processes that determines how documents are managed throughout their lifecycle — who can access them, how they're classified, how long they're retained, and how they're disposed of. It encompasses access control, classification, audit trails, and retention management, and it produces the evidence that organisations need to demonstrate compliance with regulatory and standards frameworks.
What is the difference between document management and document governance?
Document management is the operational handling of documents — storage, retrieval, search, collaboration, and workflow. Document governance is the control framework that sits on top of document management — determining who can access documents, how they're classified, how long they're kept, and ensuring that every action is auditable. FormKiQ provides both: document management as the operational layer and document governance as the control layer.
Why does document governance need to be in my own AWS account?
Because governance is only as trustworthy as the infrastructure it runs on. When access policies, encryption keys, audit logs, and retention enforcement operate in a vendor-controlled environment, you depend on the vendor to enforce them correctly and produce evidence on request. When they operate in your own AWS account, your team controls, verifies, and audits the governance infrastructure directly — and your auditors examine your infrastructure, not a vendor's attestation.
What is attribute-based access control (ABAC)?
ABAC is an access control model where access decisions are based on attributes — properties of the document (classification, sensitivity, department, project), properties of the user (role, department, location, clearance), and contextual conditions (time, location, device). Unlike folder-level or role-based access, ABAC enables document-level access decisions that adapt to the specific document and user context, making it the strongest model for governing sensitive and regulated document collections.
How does FormKiQ handle legal hold?
Legal hold suspends normal disposition to preserve documents relevant to anticipated or active litigation, investigation, or regulatory proceedings. Documents under legal hold cannot be modified, deleted, or disposed of regardless of their retention schedule — they are protected until all holds are released. Hold application, scope, and release are audit-logged with timestamps and authorising party identification.