Guide quick menu
Data Residency Guide
Document Management with Data Residency
Control where your document data is stored and processed — down to the specific AWS region and jurisdiction.
Data residency is the requirement that certain categories of data be stored and processed within a defined geographic boundary. For organizations subject to GDPR, PIPEDA, Quebec Law 25, Australia's Privacy Act, KSA PDPL, or any number of regional frameworks, residency is not a preference — it is a compliance obligation that must be demonstrable, auditable, and defensible. FormKiQ's regional deployment model makes data residency a structural property of the architecture rather than a vendor assurance that cannot be independently verified.
Who it's for
Organizations with formal or operational obligations to control where document data is stored and processed — including:
- Multinational enterprises managing document programs across jurisdictions with conflicting or complementary data residency requirements
- Government and public sector bodies subject to data sovereignty mandates that specify where citizen and operational data must reside
- Financial services and insurance organizations with regional data control requirements imposed by sector regulators or internal policy
- Healthcare organizations subject to national health data frameworks that restrict where patient records can be stored and processed
- Legal and professional services firms with client confidentiality obligations that include data location requirements
- Technology and SaaS companies building for regulated end customers who impose residency requirements as a condition of procurement
- Organizations subject to cross-border data transfer restrictions that require data to remain within a defined jurisdiction unless specific transfer mechanisms are in place
- Organizations responding to procurement, legal, or audit requirements that demand documented evidence of data location controls
When to use it
When the geographic location of document data is itself a compliance, contractual, or operational consideration. Specifically:
- When regulatory frameworks specify that personal data, health data, financial data, or government data must be stored within defined geographic boundaries
- When cross-border data transfer restrictions require that data not leave a jurisdiction without adequate transfer mechanisms in place
- When procurement or legal processes require documented evidence that document data does not leave a specified region
- When clients, partners, or regulators impose data location requirements as a condition of doing business or granting approval
- When multi-jurisdiction operations require that data for each jurisdiction remain isolated within that jurisdiction's boundaries
- When data sovereignty requirements mean that the jurisdiction governing the data must match the jurisdiction of the data subjects
What data residency means in practice
Data residency is a deceptively simple concept — data must stay in a defined place — that is practically complex to implement and demonstrate in most document management architectures. The complexity arises from several sources:
Where is data actually stored?
In vendor-managed SaaS platforms, the answer to this question depends on the vendor's infrastructure decisions, which may not be fully transparent or independently verifiable. Data may be stored in one region, processed in another, backed up in a third, and indexed in a fourth — with the vendor's residency claims covering some of these locations but not all.
In a customer-managed FormKiQ deployment, the answer is precise and verifiable: documents are stored in S3 buckets in your account in the selected region, metadata is stored in DynamoDB tables in the same region, search indexes are maintained in OpenSearch in the same region, and processing functions run as Lambda functions in the same region. There is no cross-region replication unless you build it, and no vendor-controlled data movement that could take data outside your specified boundary.
Who controls data movement?
In shared infrastructure environments, the vendor controls where data moves — for backup, disaster recovery, performance optimization, or operational reasons. In a customer-managed FormKiQ deployment, data movement is entirely under your control. No data leaves your specified region without your explicit architectural decision.
What counts as data?
Data residency requirements typically apply to personal data, sensitive data, or defined categories of regulated data — not necessarily all data. Document content, metadata, search indexes, audit logs, and processing outputs may each be subject to residency requirements independently or collectively. FormKiQ stores all of these within the deployed region by default, with no components outside the region boundary unless explicitly configured.
Can residency be demonstrated?
Compliance with data residency requirements must be demonstrable to auditors, regulators, and procurement authorities — not just asserted. In a customer-managed FormKiQ deployment, residency can be demonstrated through AWS account configuration, CloudTrail audit logs, and infrastructure documentation that shows exactly where each component is deployed and what data it holds.
How FormKiQ implements data residency
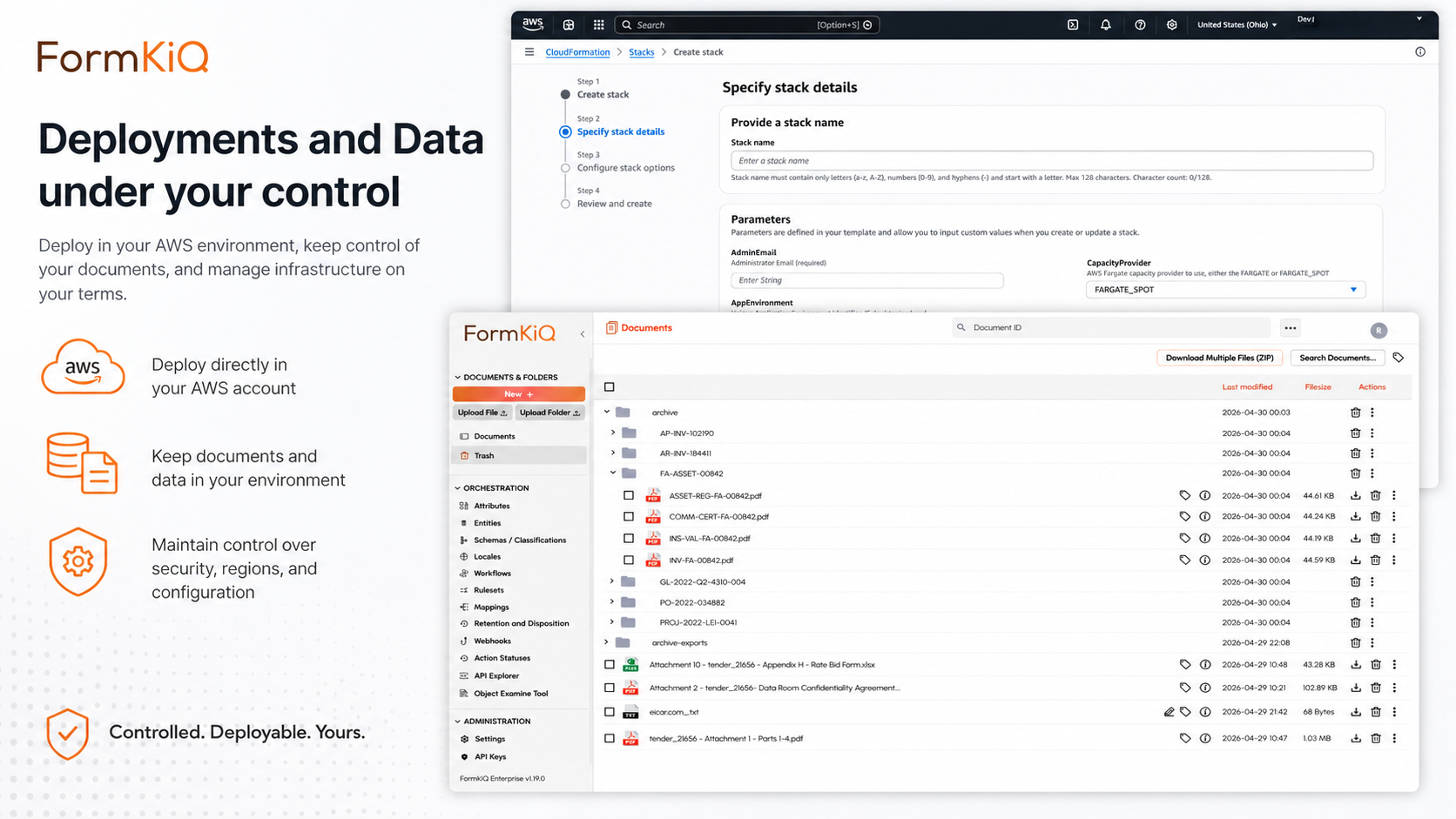
Regional deployment
FormKiQ deploys into individual AWS regions through AWS CloudFormation. Every component of the FormKiQ platform — S3 storage, DynamoDB metadata, Lambda processing, API Gateway, Cognito, CloudFront, OpenSearch, and Bedrock — is deployed within the selected region. Documents, metadata, search indexes, audit logs, and processing outputs all reside within the region where FormKiQ is deployed.
FormKiQ does not replicate data across regions by default. Cross-region replication — for disaster recovery, performance, or operational reasons — requires explicit architectural decisions and configuration by the customer, ensuring that any cross-region data movement is deliberate and documented rather than automatic.
Per-jurisdiction instances
For organizations operating across multiple jurisdictions with different residency requirements, FormKiQ supports separate deployment instances per jurisdiction — each within its own AWS account or organizational unit, deployed in the appropriate regional AWS data center, with its own document collection, metadata, access controls, and audit logs.
Cross-region authentication allows users to operate across jurisdictions where authorized — logging in once and accessing documents in multiple regional instances — while data remains isolated within each regional deployment. This provides a unified user experience without cross-border data movement.
No vendor-controlled data movement
In a customer-managed FormKiQ deployment, FormKiQ has no access to your infrastructure and no ability to move data outside your specified region. Data movement is entirely under your control, through your AWS account configuration. This makes residency verifiable and auditable in a way that vendor assurances cannot match.
Audit and documentation
AWS CloudTrail logs every API call and resource operation across your FormKiQ deployment — providing an independently verifiable record of all data access and movement within your account. Combined with AWS Config's resource inventory and S3 access logging, your residency posture is fully documented and auditable without relying on vendor-provided reports.
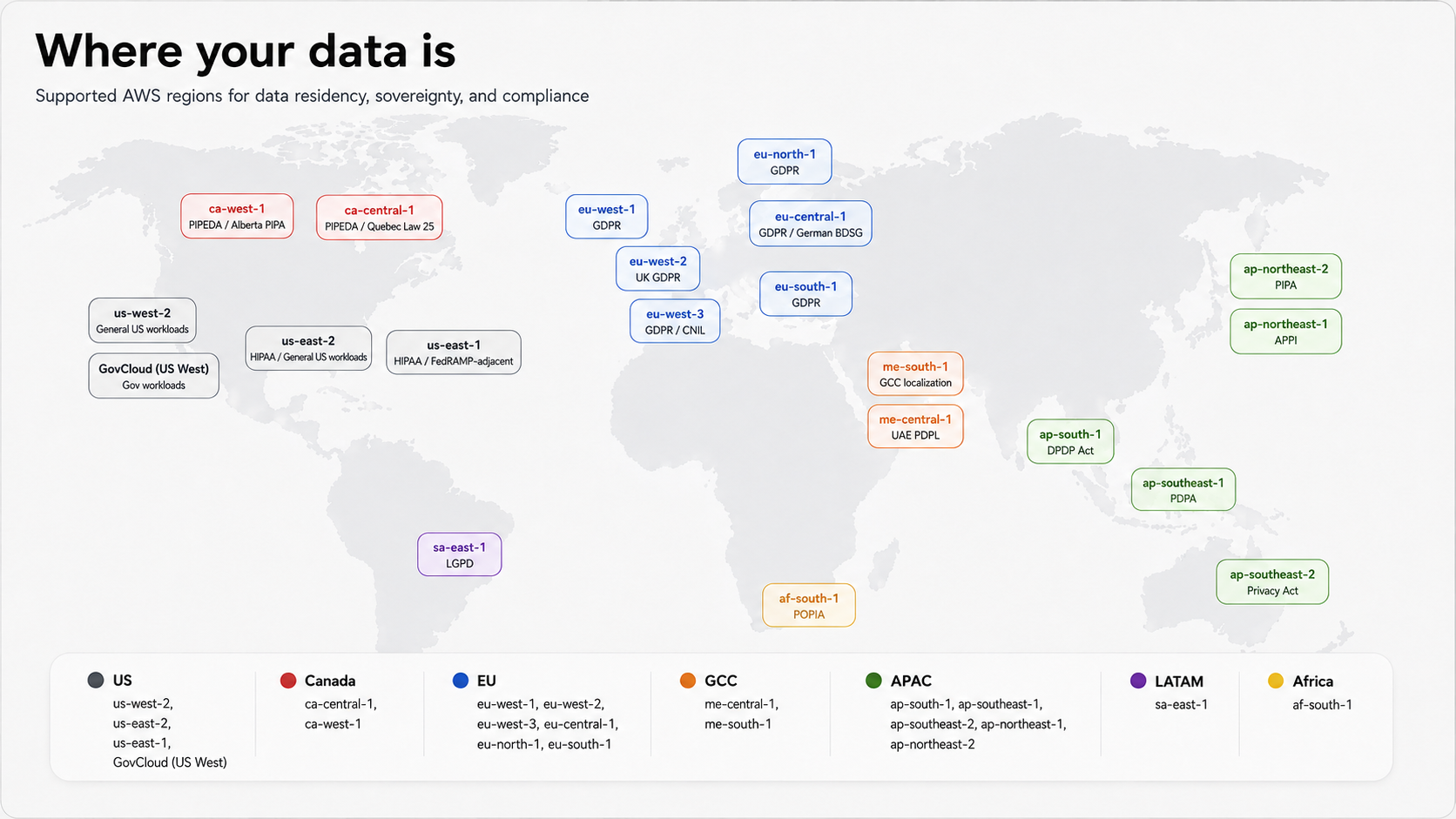
Supported AWS regions and regulatory context
FormKiQ supports deployment in the following AWS regions, each associated with specific regulatory frameworks and jurisdictional requirements:
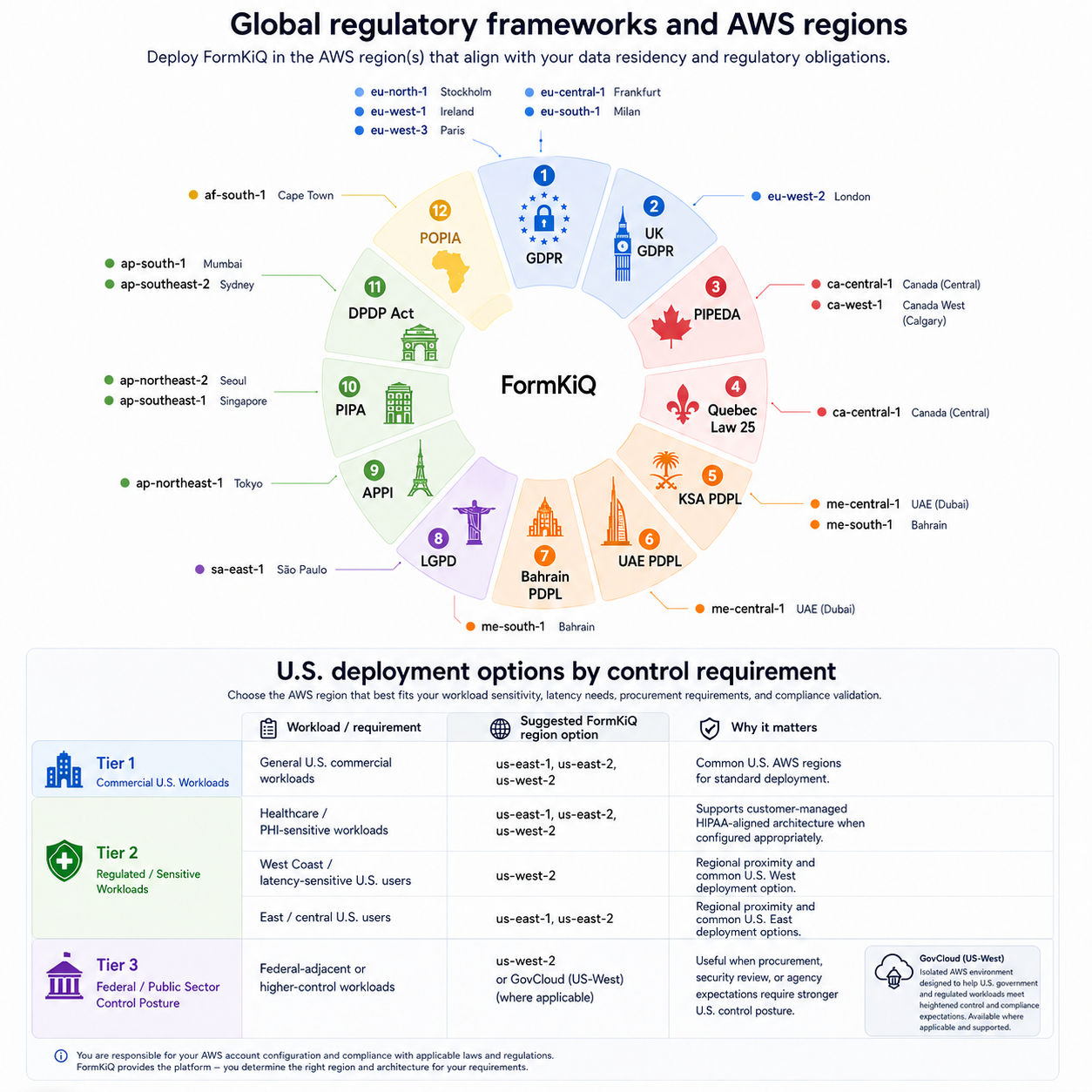
| AWS Region | Location | Key Regulatory Context |
|---|---|---|
| us-east-1 | N. Virginia | HIPAA, FedRAMP-adjacent workloads |
| us-east-2 | Ohio | HIPAA, general US workloads |
| us-west-2 | Oregon | General US workloads, GovCloud-adjacent |
| ca-central-1 | Canada (Central / Montreal) | PIPEDA, Quebec Law 25 |
| ca-west-1 | Canada (West / Calgary) | PIPEDA, Alberta PIPA |
| eu-central-1 | Frankfurt | GDPR, German BDSG |
| eu-west-1 | Ireland | GDPR |
| eu-west-2 | London | UK GDPR post-Brexit |
| eu-west-3 | Paris | GDPR, French CNIL requirements |
| eu-north-1 | Stockholm | GDPR, Nordic data protection requirements |
| eu-south-1 | Milan | GDPR, Italian healthcare and financial services |
| ap-south-1 | Mumbai | India DPDP Act |
| ap-southeast-1 | Singapore | PDPA Singapore |
| ap-southeast-2 | Sydney | Australian Privacy Act |
| ap-northeast-1 | Tokyo | Japan APPI |
| ap-northeast-2 | Seoul | South Korea PIPA |
| af-south-1 | Cape Town | South Africa POPIA |
| sa-east-1 | São Paulo | Brazil LGPD |
| me-central-1 | Middle East (UAE) | UAE PDPL, DIFC/ADGM |
| me-south-1 | Bahrain | GCC data localization requirements |
For unlisted regions, SAM CLI installation is available. FormKiQ Core supports AWS GovCloud (US West) but not East. AWS China installations are not currently supported. FormKiQ Essentials, Advanced, and Enterprise users should use the custom CloudFormation template links provided by the FormKiQ team.
Residency requirements by jurisdiction
European Union and United Kingdom
GDPR requires that personal data of EU residents be processed with appropriate technical and organizational measures, and restricts transfer outside the EEA without adequate safeguards. UK GDPR imposes equivalent requirements for UK residents post-Brexit, with transfer mechanisms diverging from the EU model. FormKiQ's EU and UK regional deployments — across six European AWS regions — support organizations meeting these requirements without cross-border data movement.
Canada
PIPEDA at the federal level and Quebec Law 25 at the provincial level impose requirements for appropriate security safeguards for personal information. Quebec Law 25 is fully in force as of September 2024 and requires privacy impact assessments for new systems processing personal information, with specific obligations when personal information is shared outside Quebec. FormKiQ's Canadian regional deployments — ca-central-1 (Montreal) and ca-west-1 (Calgary) — support Canadian data residency requirements for both federal and provincial frameworks.
United States
Federal sector organizations and defense contractors may be subject to FedRAMP requirements or ITAR restrictions on where certain data can be processed. Healthcare organizations are subject to HIPAA requirements for the security of protected health information. State-level requirements — particularly California's CCPA/CPRA — impose obligations on how personal data is managed that interact with residency considerations. FormKiQ's US regional deployments support these requirements, with GovCloud (US West) available for Core deployments subject to federal security requirements.
Middle East
The KSA PDPL, UAE PDPL, Bahrain PDPL, Oman PDPL, Qatar PDPPL, and Jordan PDPL all impose data localization and cross-border transfer restrictions that require personal data to be stored within the jurisdiction or subject to specific transfer mechanisms. FormKiQ's Middle East regional deployments — me-central-1 (UAE) and me-south-1 (Bahrain) — support residency requirements across the GCC region.
Asia-Pacific
Australia's Privacy Act, Singapore's PDPA, Japan's APPI, South Korea's PIPA, and India's DPDP Act each impose data handling requirements that interact with residency considerations — from mandatory breach notification and impact assessment requirements to specific transfer restrictions. FormKiQ's Asia-Pacific regional deployments support organizations meeting these requirements within each jurisdiction's regulatory framework.
Africa and Latin America
South Africa's POPIA and Brazil's LGPD impose data protection requirements including security safeguards and data subject rights that intersect with residency considerations. FormKiQ's regional deployments in af-south-1 (Cape Town) and sa-east-1 (São Paulo) support organizations operating under these frameworks.
Multi-jurisdiction residency architecture
For organizations operating across multiple jurisdictions with different or overlapping residency requirements, FormKiQ supports several architectural patterns:
Pattern A: Separate instances per jurisdiction
Deploy independent FormKiQ instances in separate AWS regions, each within its own AWS account or organizational unit. Each instance holds only the documents and metadata for its jurisdiction, with no cross-region data movement. Cross-region authentication allows authorized users to access documents in multiple regional instances through a single identity. This pattern provides the strictest residency boundary and is appropriate for organizations with non-overlapping jurisdictional requirements.
Pattern B: Hub and spoke with regional data stores
A central administrative instance handles governance configuration, policy management, and cross-jurisdiction reporting — while regional instances hold the actual document content and metadata for each jurisdiction. Administrative metadata — policy configurations, user assignments, audit summaries — is held centrally, while document data remains in the appropriate regional boundary. This pattern supports centralized governance oversight without centralizing sensitive document data.
Pattern C: Shared global with regional classification
A shared global instance with strict metadata classification and attribute-based access control enforces regional boundaries at the access layer rather than the infrastructure layer — documents are tagged with jurisdiction attributes, and access policies ensure that users in each jurisdiction can only access documents tagged for their jurisdiction. This pattern is appropriate where the regulatory requirement is for access control rather than physical data location, and where the hosting jurisdiction is acceptable to all jurisdictions served.
The right pattern depends on the specific residency requirements of each jurisdiction, the nature of the documents being managed, and the operational model of the organization. FormKiQ's architecture supports all three patterns and variants that combine elements of each.
Residency and the AI processing dimension
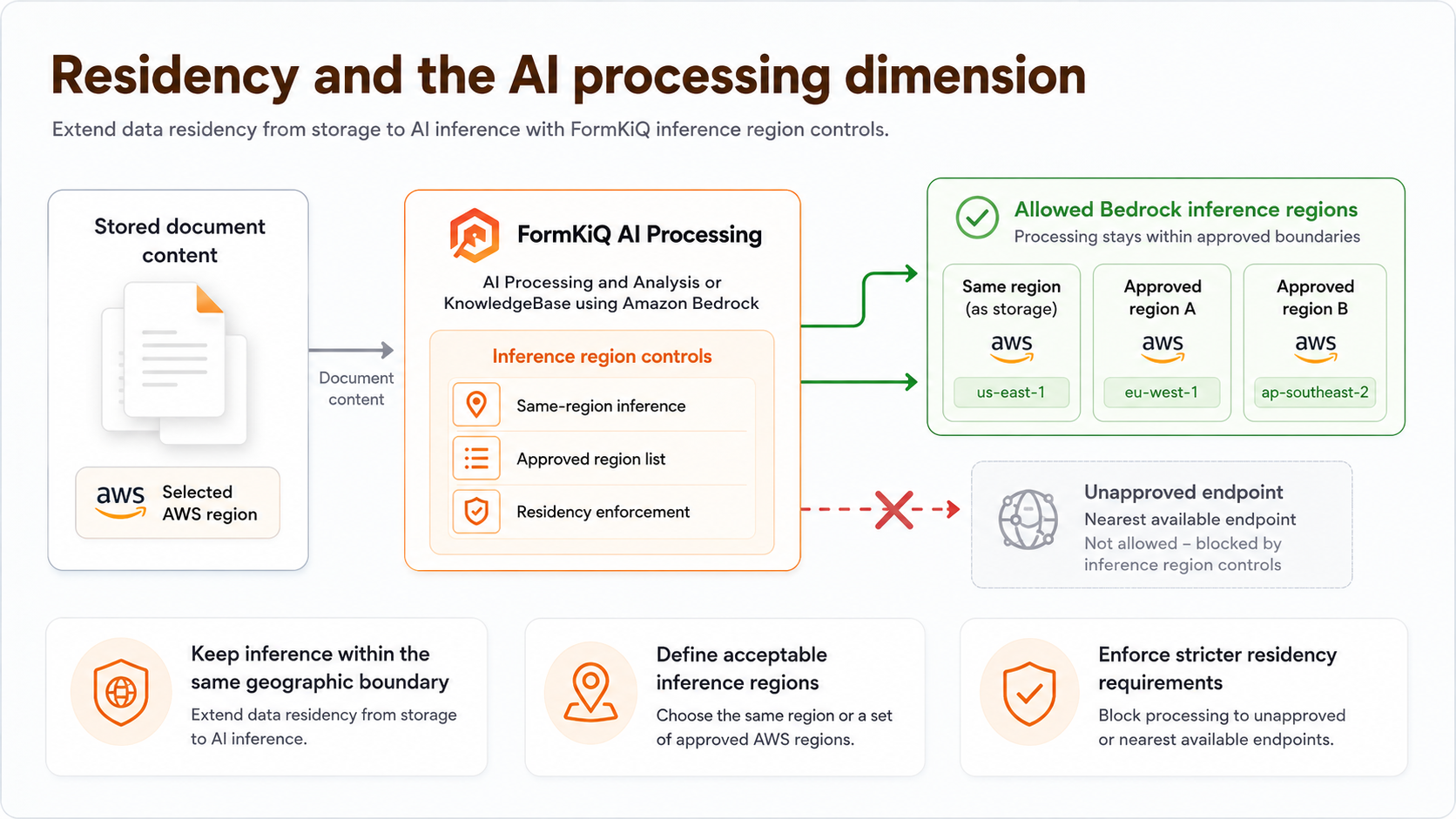
For organizations using FormKiQ's AI Processing and Analysis or KnowledgeBase modules — which process document content through Amazon Bedrock — data residency extends to AI inference. Where document content is submitted to a language model for processing, the region in which that processing occurs matters for residency compliance.
FormKiQ's inference region controls allow you to specify which AWS regions are used for Bedrock model inference — ensuring that document content is processed within the same geographic boundary as where it is stored, or within a defined set of acceptable inference regions, rather than being routed to the nearest available Bedrock endpoint regardless of its location.
For organizations with the strictest residency requirements — where even temporary processing of document content outside the specified region is not acceptable — inference region controls provide the mechanism to enforce this constraint within FormKiQ's AI processing pipeline.
Demonstrating residency to auditors and regulators
One of the practical challenges of data residency compliance is demonstrating it — providing auditors, regulators, and procurement authorities with evidence that residency requirements are being met, not just asserting compliance. In a customer-managed FormKiQ deployment, residency can be demonstrated through:
- AWS account configuration — CloudFormation stack deployment records confirm which region each FormKiQ component is deployed in
- S3 bucket configuration — bucket region settings and replication configuration confirm where documents are stored and whether cross-region replication is enabled
- CloudTrail audit logs — API call records confirm where data access and processing operations occur
- AWS Config resource inventory — continuous recording of resource configuration confirms the deployment state at any point in time
- Security configuration reports — available as an add-on for Advanced customers and included for Enterprise customers, providing documented evidence of the security and deployment configuration of the FormKiQ environment
- Network architecture documentation — available as an add-on for Advanced customers and included for Enterprise customers, providing architectural documentation that supports residency compliance demonstration
Important guardrail
FormKiQ's regional deployment model provides the technical architecture for data residency — ensuring that documents and metadata are stored and processed within the selected AWS region by default. Whether a specific FormKiQ deployment satisfies the data residency requirements of GDPR, PIPEDA, Quebec Law 25, KSA PDPL, or any other framework depends on the complete configuration of the deployment, the categories of data being processed, and the legal interpretation of residency requirements applicable to the organization's specific situation. This must be validated by your legal and compliance teams rather than assumed from the deployment model alone.