HIPAA-Aligned Document Management — with PHI Encryption, Access Controls, Audit Trails, and BAA-Eligible AWS Services — Deployed into Your Own AWS Account
Organisations that create, receive, maintain, or transmit protected health information (PHI) face a specific document management challenge: every document containing PHI must be stored, accessed, shared, and retained under the technical, administrative, and physical safeguards required by HIPAA. Traditional document management platforms either lack the controls HIPAA demands or operate in vendor-controlled environments where the organisation cannot independently verify that safeguards are in place.
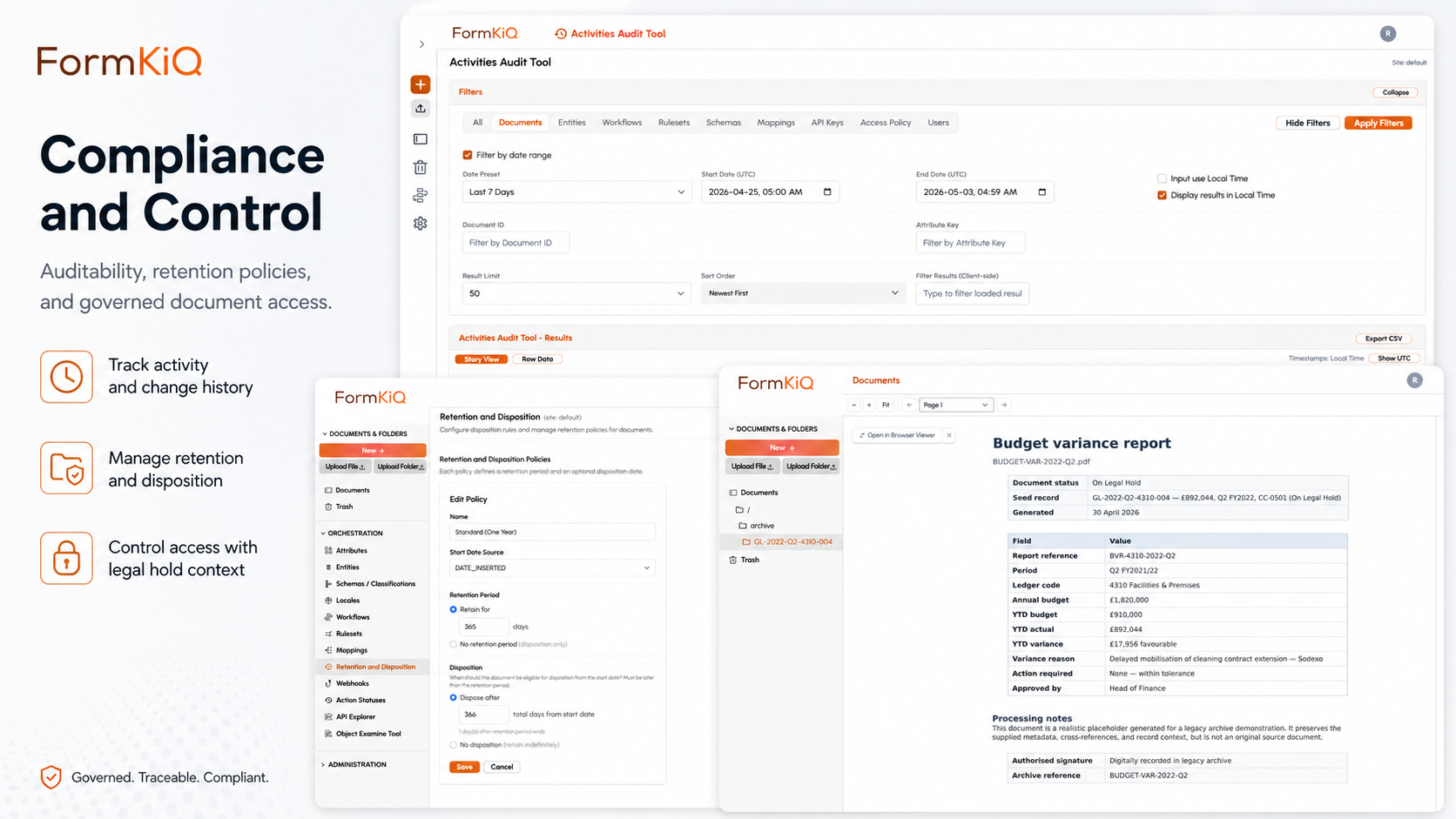
FormKiQ provides document management on AWS infrastructure built entirely on BAA-eligible AWS services — deployed into your own AWS account, encrypted with customer-managed keys, and governed by access controls, audit trails, and retention policies designed to support HIPAA compliance. Your PHI stays in your environment. Your security team controls the keys, the identity layer, and the access policies. And every document access event is recorded in an audit trail you own.
What HIPAA Requires for Document Management
HIPAA's Security Rule specifies safeguards that directly affect how documents containing PHI are managed. The challenge for most organisations isn't understanding what HIPAA requires — it's implementing those requirements within a document management platform that operates under your control rather than a vendor's. The table below maps the Security Rule's key requirements to specific FormKiQ capabilities, showing how each safeguard is addressed within your own AWS environment:
| HIPAA Requirement | Security Rule Reference | FormKiQ Capability |
|---|---|---|
| Access controls | § 164.312(a)(1) | Attribute-based access control (ABAC) at the document level — PHI documents visible only to authorised roles; unique user identification; automatic logoff via session management |
| Audit controls | § 164.312(b) | Every document access, view, download, modification, and disposition event logged with timestamps, actor identification, and action type |
| Integrity controls | § 164.312(c)(1) | Document versioning with integrity verification; mechanisms to authenticate that PHI has not been improperly altered or destroyed |
| Transmission security | § 164.312(e)(1) | Encryption in transit (TLS) for all API and console communication; encrypted document delivery |
| Encryption at rest | § 164.312(a)(2)(iv) | AWS KMS customer-managed encryption keys — every document encrypted at rest with keys you own and control |
| Person or entity authentication | § 164.312(d) | Amazon Cognito with SAML SSO integration (Microsoft Entra, Google IdP, Auth0); multi-factor authentication support |
| Contingency planning | § 164.308(a)(7) | Amazon S3 eleven-nines durability; configurable backup and disaster recovery; multi-region deployment available |
| Workforce security | § 164.308(a)(3) | Role-based and attribute-based access policies; access termination procedures; access review capabilities |
| Security incident procedures | § 164.308(a)(6) | Audit trail analysis; access anomaly detection; incident documentation within the platform |
| Business associate agreements | § 164.308(b)(1) | FormKiQ operates on BAA-eligible AWS services; AWS BAA covers the underlying infrastructure; FormKiQ executes BAAs with covered entities and business associates |
PHI Document Types Managed in FormKiQ
PHI appears across a broader range of document types than most organisations initially recognise. Beyond the obvious clinical records, PHI is present in insurance correspondence, administrative forms, vendor agreements, compliance programme documentation, and research files. FormKiQ provides governed storage for all of these document categories — with classification, access controls, and retention policies tailored to the specific HIPAA considerations each type presents:
| Document Category | Examples | Key HIPAA Considerations |
|---|---|---|
| Patient records | Clinical notes, lab results, imaging reports, discharge summaries, care plans | Minimum necessary access; patient right of access; retention per state/provincial requirements |
| Insurance and billing | Claims, EOBs, prior authorisation documentation, billing statements | Access restricted to billing/finance roles; retention per payer and regulatory requirements |
| Administrative records | Enrolment forms, eligibility documentation, consent forms, HIPAA authorisations | Consent tracking; authorisation management; retention tied to patient relationship |
| Business associate documentation | BAAs, vendor compliance assessments, subcontractor agreements, security questionnaires | BAA lifecycle management; vendor compliance tracking; retention through business relationship |
| Compliance documentation | Risk assessments, security policies, training records, incident reports, breach notifications | Policy versioning; training acknowledgment tracking; incident documentation; retention per HIPAA requirements |
| Research records | IRB protocols, informed consent documents, de-identified data sets, research correspondence | IRB approval tracking; consent management; de-identification verification; research data retention |
How FormKiQ Supports HIPAA Compliance on AWS
The Security Rule's requirements translate into four technical capability areas for document management: encryption, access controls, audit trails, and sensitivity classification. FormKiQ addresses each of these within your own AWS account — meaning your security team can verify the implementation directly rather than relying on vendor attestations.
Encryption
Encryption is the foundation of PHI protection. HIPAA requires both encryption at rest and encryption in transit, with the organisation maintaining control over its encryption keys. FormKiQ's encryption architecture uses AWS KMS, keeping key ownership and key policy management entirely within your account:
| Encryption Layer | Implementation |
|---|---|
| At rest | Every document encrypted using AWS KMS customer-managed keys — you own and control the encryption keys in your AWS account |
| In transit | TLS encryption for all API communication, console access, and document transfer |
| Key management | AWS KMS provides hardware-backed key storage, automatic key rotation, and key usage audit logging — all within your account |
| Key access control | KMS key policies restrict key usage to authorised services and roles — preventing decryption by unauthorised parties |
Access Controls
HIPAA's minimum necessary standard requires that workforce members access only the PHI they need to perform their job functions. This is difficult to enforce in traditional document management platforms that apply access controls at the folder or repository level. FormKiQ provides document-level access controls through ABAC — meaning that individual documents within a patient file can have different access rules based on their sensitivity, the role of the person requesting access, and the context of the access:
- Attribute-based access control (ABAC) — document visibility tied to metadata values (department, role, patient identifier, sensitivity classification)
- Minimum necessary enforcement — access policies configured to limit PHI exposure to the minimum necessary for each role's function
- Document-level restrictions — individual documents restricted independently within collections (e.g., psychiatric notes restricted within a general patient file)
- Temporal access — access rules that change based on patient status, treatment completion, or relationship end
- Emergency access — configurable break-glass procedures for emergency PHI access with mandatory audit logging and post-access review
Audit Trail
HIPAA requires audit controls that record and examine activity in systems containing PHI. In a vendor-hosted platform, audit logs are in the vendor's environment — you request them rather than querying them directly. FormKiQ's audit trail operates within your AWS account, giving your security and compliance teams direct access to every document-level event:
| Audit Capability | What It Records |
|---|---|
| Document access | Who viewed, downloaded, or accessed each PHI document — with timestamp, user identity, and access method |
| Document modification | Who created, edited, or deleted PHI documents — with before/after state and timestamp |
| Access control changes | Who changed access permissions on PHI documents — with prior and new permission state |
| Authentication events | Login attempts, session creation, and session termination — logged through Amazon Cognito and CloudTrail |
| Administrative actions | Configuration changes, policy updates, and system administration activities |
Audit logs are stored in AWS CloudTrail and FormKiQ's document-level audit log — both within your AWS account, encrypted, and retained per your audit log retention policy.
Sensitivity Classification
FormKiQ's AI Processing and Analysis module — powered by Amazon Bedrock — can automatically identify documents containing PHI. All AI processing runs within your AWS account; PHI content never leaves your cloud environment.
- PHI detection — incoming documents scanned for patient names, medical record numbers, dates of service, diagnoses, treatment information, and other PHI elements
- Classification tagging — documents containing PHI automatically tagged with sensitivity metadata, triggering HIPAA-specific access controls
- Handling rules — configurable actions on PHI detection (restrict access, apply encryption enforcement, route to compliance review)
BAA-Eligible AWS Services
A critical requirement for any cloud-based system handling PHI is that the underlying infrastructure services are covered by a Business Associate Agreement. AWS offers a BAA that covers a defined list of eligible services, and organisations must ensure their architecture uses only BAA-eligible services for PHI workloads. FormKiQ is built entirely on services included in the AWS BAA:
| AWS Service | Role in FormKiQ | BAA-Eligible |
|---|---|---|
| Amazon S3 | Document storage | ✓ |
| Amazon DynamoDB | Metadata storage | ✓ |
| Amazon Cognito | Identity and authentication | ✓ |
| AWS Lambda | Serverless compute | ✓ |
| Amazon OpenSearch | Full-text search | ✓ |
| AWS KMS | Encryption key management | ✓ |
| AWS CloudTrail | Infrastructure audit logging | ✓ |
| Amazon Textract | OCR and document extraction | ✓ |
| Amazon Bedrock | AI processing and analysis | ✓ |
| Amazon SNS | Event notifications | ✓ |
| Amazon SQS | Message queuing | ✓ |
HIPAA Document Workflows
Beyond the technical safeguards, HIPAA compliance requires operational processes — patient record intake, business associate management, risk assessment documentation, and workforce training tracking. These processes are inherently document-centric, and FormKiQ provides configurable workflows for each:
Patient Record Management
- Clinical document intake — patient documents captured via API, web console, email, SFTP, or scanner with PHI sensitivity classification at the point of ingestion
- Access-controlled distribution — clinical documents accessible only to authorised clinical, billing, and administrative roles based on ABAC policies
- Patient right of access — workflows supporting patient requests for access to their records, with identity verification, document compilation, and delivery tracking
BAA and Vendor Compliance
- BAA lifecycle management — business associate agreements drafted from templates, routed through legal review, executed via eSignature, and tracked with expiry monitoring
- Vendor compliance tracking — vendor security assessments, compliance certifications, and BAA status managed within vendor document collections
- Subcontractor management — subcontractor BAAs and compliance documentation collected and governed alongside primary BAAs
Compliance Programme Documentation
- Risk assessment documentation — HIPAA risk assessments stored with version control, review tracking, and retention
- Policy management — HIPAA-related policies managed through the full policy lifecycle (authoring, approval, distribution, acknowledgment, review)
- Training records — HIPAA training completion and acknowledgment tracked per workforce member
- Incident documentation — security incidents and breach notifications documented with required elements and timeline tracking
Who Uses HIPAA Document Management on AWS
HIPAA applies to covered entities (healthcare providers, health plans, and healthcare clearinghouses) and to the business associates who process PHI on their behalf. The scope is broader than most organisations expect — any vendor, contractor, or service provider that creates, receives, maintains, or transmits PHI in the course of performing services for a covered entity is a business associate with its own HIPAA obligations:
| Organisation Type | HIPAA Document Needs | Key Drivers |
|---|---|---|
| Healthcare providers | Patient records, clinical documentation, billing records, compliance documentation | Direct HIPAA covered entity obligations |
| Health plans and insurers | Member records, claims documentation, enrolment records, provider credentialing | Covered entity obligations; state insurance regulations |
| Business associates | Client PHI processed on behalf of covered entities, BAA management, compliance evidence | Business associate obligations; client audit requirements |
| Health IT vendors | Customer PHI in SaaS environments, BAA management, security documentation | Business associate obligations; customer security assessments |
| Clinical research organisations | Research records containing PHI, IRB documentation, informed consent management | HIPAA research provisions; IRB requirements; sponsor requirements |
| Public health organisations | Population health data, surveillance records, reporting documentation | HIPAA public health provisions; reporting requirements |
FormKiQ Editions for HIPAA Document Management
| Capability | Core Foundation |
Essentials Operational |
Advanced AI + Automation |
Enterprise Full platform |
|---|---|---|---|---|
| Foundation | ||||
| Document Storage (S3) & API | ||||
| Tagging, Search & Classification | ||||
| OCR (Tesseract) | ||||
| Essentials and above | ||||
| OCR & IDP (Textract) | — | |||
| SSO (SAML — Entra, Google, Auth0) | — | |||
| Workflows, Queues & Rulesets | — | |||
| Encryption (KMS — in-transit & at-rest) | — | |||
| Document Control & Versioning | — | |||
| Antivirus & Anti-Malware | — | |||
| Advanced and Enterprise | ||||
| AI Processing & PHI Classification (Bedrock) | — | — | ||
| Document Generation | — | — | ||
| eSignature Integration | — | — | ||
| Document Gateway Modules | — | — | ||
| Enhanced Full-Text Search (OpenSearch) | — | — | ||
| Multi-Instance & Multi-Region Licensing | — | — | ||
| Enterprise only | ||||
| Vendor-Managed & Hybrid Deployment | — | — | — | |
| Custom SLAs & Compliance Consulting | — | — | — | |
| Support | ||||
| Support | Community (Slack & GitHub) | Support Portal (2-business-day SLA) | Private Slack + videoconference + 40 hrs onboarding | Rapid response (8-business-hour SLA) + strategic architecture support |
Deployment Models
| Model | Description | Availability |
|---|---|---|
| Customer-Managed AWS | Deploys directly into your AWS account via CloudFormation. Full control of infrastructure, networking, encryption keys, and operations. | All editions |
| Vendor-Managed | FormKiQ manages the AWS infrastructure on your behalf — deployment, updates, and operational support. | Enterprise |
| Hybrid | You retain control of specific components (encryption keys, network config) while delegating operational management to FormKiQ. | Enterprise |
Every deployment is a dedicated, isolated instance. FormKiQ does not operate a shared multi-tenant environment.
Getting Started
FormKiQ Core can be deployed to your AWS account in fifteen to twenty minutes. HIPAA-aligned capabilities — including KMS encryption, ABAC, AI-powered PHI classification, and BAA lifecycle management — are available on FormKiQ Essentials, Advanced, and Enterprise.
Frequently Asked Questions
Is FormKiQ HIPAA-certified?
There is no formal HIPAA certification. HIPAA compliance is the responsibility of covered entities and business associates — it's demonstrated through the implementation of required safeguards and documented through risk assessments, policies, and audit evidence. FormKiQ provides the technical safeguards (encryption, access controls, audit trails, integrity controls) and operates on BAA-eligible AWS services. FormKiQ executes Business Associate Agreements with covered entities and business associates who deploy the platform for PHI management.
Does FormKiQ sign a BAA?
Yes. FormKiQ executes Business Associate Agreements with covered entities and business associates. The BAA covers FormKiQ's obligations as a business associate or subcontractor in relation to PHI managed within the platform. AWS separately provides a BAA covering the underlying infrastructure services.
Where is PHI stored?
PHI is stored in Amazon S3 within your own AWS account, in the AWS region you select. Metadata is stored in Amazon DynamoDB, and search indexes in Amazon OpenSearch — all within your account, all encrypted with your KMS keys. PHI never leaves your AWS environment.
How does FormKiQ handle the minimum necessary standard?
FormKiQ's attribute-based access control (ABAC) enables minimum necessary enforcement at the document level. Access policies can be configured to limit PHI exposure based on role, department, treatment relationship, or any custom attribute — ensuring that each workforce member sees only the PHI necessary for their job function.
Can FormKiQ support patient right of access requests?
Yes. FormKiQ's search and retrieval capabilities, combined with configurable workflows, support the process of receiving, verifying, compiling, and fulfilling patient access requests. Documents can be compiled by patient identifier across the repository and delivered through governed channels with audit-logged fulfillment.
How does FormKiQ handle PHI retention?
HIPAA does not specify a single retention period — retention requirements come from state/provincial law, payer requirements, and organisational policy. FormKiQ supports configurable retention policies by document type, jurisdiction, and regulatory requirement. Documents under legal hold are protected from disposition regardless of retention schedule.