Guide contents
Business Solution Guide
Incident & Investigation Management on AWS
Document-centric evidence management, review, and resolution trails on AWS infrastructure you control.
Incidents and investigations generate some of the most sensitive and legally consequential documents in any organization. Workplace safety incidents, compliance violations, fraud investigations, regulatory inquiries, security breaches, environmental events, and internal complaints all produce evidence files, witness statements, inspection reports, expert assessments, correspondence, and resolution documentation — yet in most organizations, investigation files are managed through spreadsheets, email, shared drives, or standalone case tools with no governed way to secure the evidentiary record, enforce chain of custody, control access to sensitive materials, or demonstrate that the investigation was conducted thoroughly and impartially.
FormKiQ's Incident & Investigation Management solution provides the document layer for the full investigation lifecycle — from initial report and evidence collection through assessment, investigation, findings, resolution, and retention — deployed directly into your AWS account. AI-powered document analysis using Amazon Bedrock classifies incoming evidence, extracts key entities and facts, identifies patterns across related incidents, and flags sensitive content for access restriction. Workflow automation routes investigation tasks through structured review and approval chains. And the entire investigation record — every document, every version, every access event — is stored, encrypted, and auditable within your own AWS environment.

The Investigation Document Lifecycle
FormKiQ supports each stage of the investigation document lifecycle within a governed, auditable platform:
| Stage | What Happens | How FormKiQ Handles It |
|---|---|---|
| Incident Report | An incident is reported through a web portal, hotline transcript, email, or internal submission | Multi-channel intake via API, email connector, or document upload — each report registered with receipt timestamp, reporter information (with anonymity support), and incident classification |
| Evidence Collection | Supporting documents are gathered — photos, video, witness statements, logs, communications, physical evidence records, expert reports | Document upload with classification, tagging by evidence type, chain-of-custody metadata, and association to the investigation case file — with OCR and AI extraction for unstructured documents |
| Assessment & Triage | The incident is assessed for severity, regulatory reporting obligations, and investigation scope | Triage workflow with severity classification, regulatory-reporting-trigger evaluation, investigation-scope determination, and investigator assignment |
| Investigation | Investigators conduct interviews, gather additional evidence, and document findings | Investigation case file with structured access controls — interview records, evidence documents, investigator notes, and expert assessments accessible only to authorized investigation team members |
| Findings & Determination | The investigation team documents findings and makes a determination | Findings report with supporting evidence references, root-cause analysis, determination metadata (substantiated, unsubstantiated, inconclusive), and corrective-action recommendations |
| Resolution & Corrective Action | Corrective actions are documented and tracked to completion | Corrective action plan with task assignments, deadlines, completion tracking, and evidence of remediation — linked to the investigation case file |
| Regulatory Reporting | Required reports are filed with regulatory authorities | Document Generation produces regulatory reports from governed templates — OSHA 301, WCB reports, environmental incident reports, SEC reports, data breach notifications — with filing confirmation metadata |
| Retention & Archive | Completed investigations are retained according to policy and regulatory requirements | Configurable retention policies by incident type, severity, jurisdiction, and regulatory framework — with legal hold for investigations that may lead to litigation |
AI-Powered Evidence Analysis with Amazon Bedrock
Investigation evidence is often voluminous and unstructured — handwritten statements, photographs with captions, email threads, system logs, medical records, and expert reports. FormKiQ's AI Processing and Analysis module — powered by Amazon Bedrock — assists investigators by classifying evidence, extracting key facts, and identifying patterns that may not be apparent from individual documents.
All AI processing runs within your AWS account through Amazon Bedrock, using supported large language models including Anthropic Claude, Amazon Nova, and other available models. Your investigation content never leaves your cloud environment. Inference region controls allow you to specify which AWS regions are used for model processing, ensuring investigation data stays within the geographic boundaries required by your data residency and regulatory program.
What Bedrock Extracts from Investigation Documents
| Extraction Type | What It Captures | How It's Used |
|---|---|---|
| Evidence Classification | Document type — witness statement, incident report, inspection record, photograph, medical record, expert assessment, correspondence, system log, policy document | Classification metadata organizes the evidence record and supports evidence-completeness tracking |
| Key Entities | Individuals involved (reporters, witnesses, subjects, investigators), locations, dates, times, equipment identifiers, organizational units | Entity metadata enables cross-referencing across evidence documents and identification of related incidents |
| Factual Extraction | Incident descriptions, injury details, environmental conditions, sequences of events, contributing factors, policy references | Extracted facts presented to investigators as structured summaries alongside source documents for verification |
| Sensitivity Indicators | Whistleblower-protected content, legally privileged material, personally identifiable information, medically sensitive information, law enforcement-sensitive content | Sensitivity classification drives access controls and handling restrictions within the investigation file |
| Pattern Indicators | Similar incident types, recurring locations, repeated equipment, common contributing factors, related time periods | Pattern metadata enables cross-investigation analysis for systemic risk identification |
How AI Evidence Analysis Works in FormKiQ
Evidence intake
A document is added to the investigation case file via upload, email connector, or API submission
AI processing trigger
A document action triggers Amazon Bedrock analysis based on the evidence type or investigation classification
Classification and extraction
Bedrock classifies the evidence document and extracts key entities, facts, sensitivity indicators, and pattern indicators
Metadata application
Extracted data is applied to the document record as structured metadata within the investigation case file
Case file enrichment
Extracted metadata is aggregated at the case level, enabling investigators to view structured summaries of all evidence collected
Access control enforcement
Sensitivity classifications trigger ABAC rules restricting access to appropriately authorized investigation team members
Human review
All AI-extracted metadata is available for investigator review and correction before being relied upon in findings. AI analysis can be applied selectively to specific evidence types, incident categories, or investigation stages.
Chain of Custody and Evidence Integrity
FormKiQ provides document-level chain-of-custody tracking for investigation evidence:
| Capability | Description |
|---|---|
| Intake provenance | Every evidence document recorded with source, receipt method, receipt timestamp, and receiving officer |
| Version integrity | Document versioning with immutable version history — original evidence preserved, amendments tracked as new versions |
| Access logging | Every access event (view, download, print, share) recorded in the audit trail with user identity, timestamp, and action |
| Transfer tracking | Evidence transfers between investigators, teams, or organizations documented with transfer metadata and acceptance confirmation |
| Legal hold | Investigation files can be placed under legal hold, preventing modification or deletion regardless of retention schedule |
| Export and attestation | Evidence packages can be exported with integrity verification for regulatory submission, legal proceedings, or external review |
Investigation Access Controls
Investigation documents require strict access controls — the subjects of an investigation should not have access to witness statements, and HR investigations require separation between the investigation team and the subject's management chain. FormKiQ's attribute-based access controls (ABAC) enforce these boundaries:
| Scenario | How FormKiQ Handles It |
|---|---|
| Investigation team restriction | Only designated investigation team members can access the case file — access controlled by investigation-team attribute |
| Subject exclusion | The subject of the investigation and their direct management chain are explicitly excluded from the case file through access-denial rules |
| Witness protection | Witness identity information can be classified at a higher sensitivity level than the incident facts, restricting witness-identity access to the lead investigator and legal counsel |
| Regulatory access | Regulatory authorities can be granted read-only access to specific case files or evidence documents through scoped, time-bound access provisions |
| Legal privilege | Legally privileged investigation documents (counsel communications, legal analysis) can be classified separately with privilege-restricted access |
Investigation Metadata and Search
FormKiQ's metadata architecture provides structured classification for investigation records:
| Category | Example Fields |
|---|---|
| Case identity | Investigation case number, incident report number, incident type (safety, compliance, fraud, harassment, security, environmental, regulatory) |
| Parties | Reporter (named or anonymous), subject(s), witnesses, lead investigator, investigation team, legal counsel |
| Incident | Incident date, location, severity, regulatory reporting trigger, business unit, facility |
| Classification | Investigation type, jurisdiction, regulatory framework, complexity tier, litigation status |
| Status | Reported, under assessment, investigation open, pending evidence, findings drafted, findings approved, corrective action in progress, closed, reopened |
| Outcome | Substantiated, unsubstantiated, inconclusive, referred to law enforcement, referred to regulator |
| Corrective Action | Actions assigned, responsible parties, deadlines, completion status |
All metadata fields are searchable — enabling queries such as:
- All open investigations by severity and type
- All investigations at a specific facility in the past 12 months
- All investigations pending corrective-action completion
- All substantiated investigations in a specific category for trend analysis
- All investigations under legal hold or in litigation
- All incidents with specific contributing factors for systemic risk review
Integration with Enterprise Systems
FormKiQ's Integration Framework Modules connect investigation management to the enterprise systems where incident data originates and is consumed:
EHS / Safety Management
Incident documents linked to environmental, health, and safety management systems — investigation outcomes feeding back into hazard registers and risk assessments
HR / HRIS
Workplace investigation documents linked to employee records — with appropriate access controls separating investigation access from general HR access
Compliance / GRC
Investigation findings linked to compliance management and governance, risk, and compliance platforms — supporting regulatory reporting and control-effectiveness assessment
ERP
Investigation-related costs (remediation, fines, settlements) linked to financial records through the Integration Framework
FormKiQ Editions for Incident & Investigation Management
Incident & Investigation Management is available as a Solution Layer on FormKiQ Advanced and Enterprise. The modules that power investigation management — AI Processing and Analysis, Workflow Automation, ABAC, and Integration Frameworks — are Capability Extension Modules available on Advanced and Enterprise editions.
| Capability | Core Foundation |
Essentials Operational |
Advanced AI + Automation |
Enterprise Full platform |
|---|---|---|---|---|
| Foundation | ||||
| Document Storage, API & Web Console | ||||
| Tagging, Search & Classification | ||||
| OCR (Tesseract) & Multi-Tenant Support | ||||
| Essentials and above | ||||
| SSO (SAML — Entra, Google, Auth0) | — | |||
| Workflows, Queues & Rulesets | — | |||
| Encryption (in-transit & at-rest) & Document Control | — | |||
| Advanced and Enterprise | ||||
| AI Processing & Analysis (Bedrock) | — | — | ||
| Document Generation | — | — | ||
| ABAC (Attribute-Based Access Control) | — | — | ||
| Integration Frameworks (EHS, HR, GRC, ERP) | — | — | ||
| Solution Layers (Incident & Investigation) | — | — | ||
| Multi-Instance & Multi-Region Licensing | — | — | ||
| Enterprise only | ||||
| Vendor-Managed & Hybrid Deployment | — | — | — | |
| Custom SLAs & Compliance Consulting | — | — | — | |
| Support | ||||
| Support tier | Community (Slack & GitHub) | Support Portal (2-biz-day SLA) | Private Slack + videoconference + 40 hrs onboarding | Rapid response (8-biz-hr SLA) + strategic architecture support |
Compliance and Regulatory Alignment for Investigations
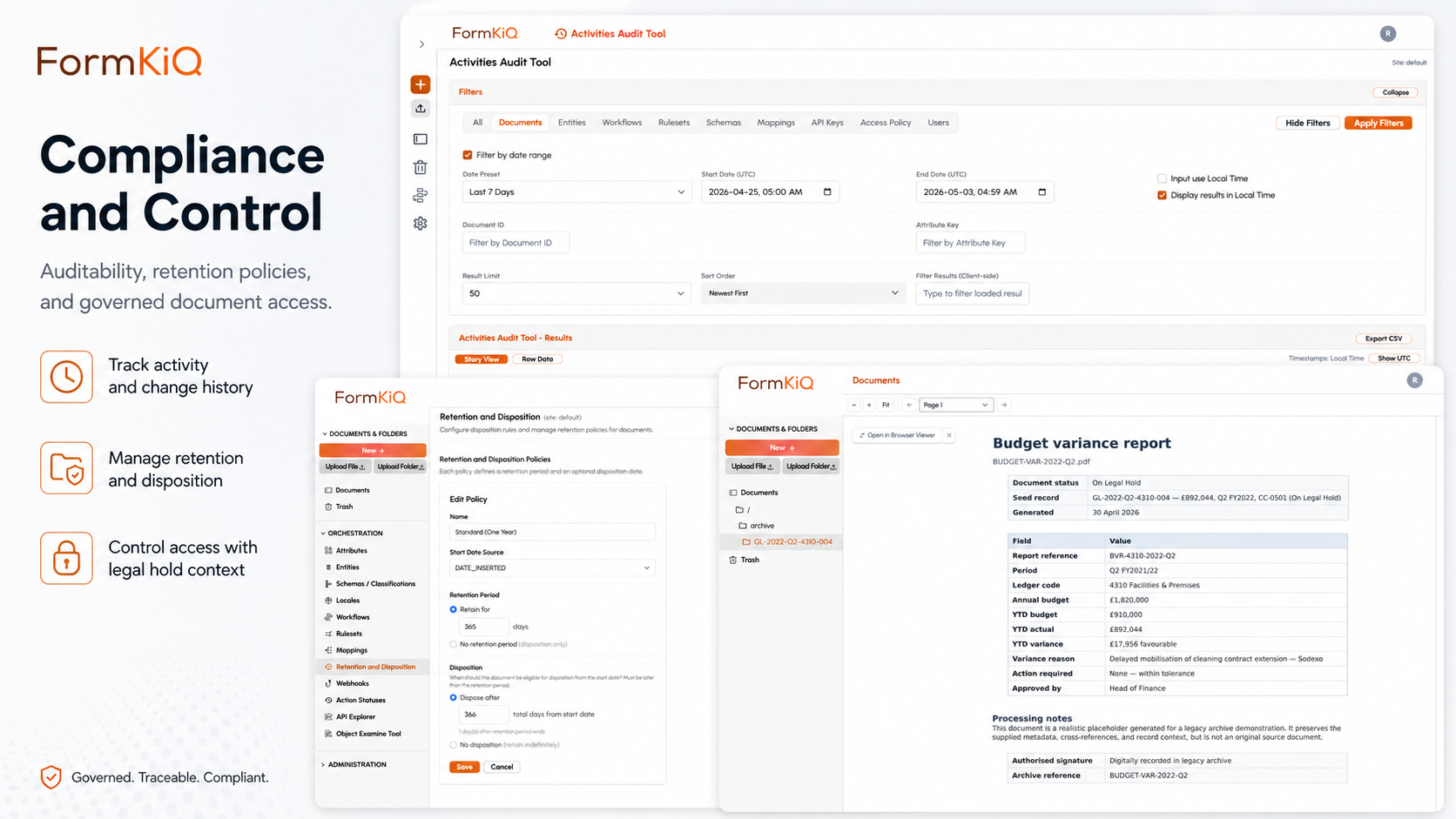
| Framework | Investigation-Specific Requirements | FormKiQ Capabilities |
|---|---|---|
| OSHA (US) | Incident reporting (Form 300/301), investigation documentation, recordkeeping for 5+ years | Document Generation for OSHA forms · Retention enforcement · Audit trails |
| WorkSafe / WCB (Canada, AU) | Workplace incident reporting, investigation documentation, corrective action tracking | Jurisdiction-specific reporting templates · Retention schedules · Corrective-action workflow |
| HSE (UK) | RIDDOR reporting, investigation documentation, risk assessment records | RIDDOR report generation · Retention enforcement · Audit trails |
| SOX | Financial fraud investigation documentation, whistleblower protection records | Access controls · Whistleblower anonymity support · Retention enforcement · Audit trails |
| SEC / DOJ (US) | Securities fraud investigation documentation, cooperation credit documentation | Evidence integrity · Chain of custody · Legal hold · Export for regulatory submission |
| GDPR / UK GDPR | Data breach investigation documentation, notification records, impact assessments | Data residency enforcement · Breach-notification deadline tracking · Retention controls |
| Environmental Regulations | Environmental incident investigation, remediation documentation, regulatory reporting (EPA, CEPA, EA) | Incident classification · Regulatory-report generation · Remediation tracking |
| Whistleblower Statutes | Reporter anonymity, retaliation-protection documentation, investigation independence | Anonymous intake support · Access controls separating reporter identity from investigation facts |
Whether a FormKiQ deployment satisfies any specific framework depends on configuration and must be validated by your legal and compliance teams.
Who Uses Incident & Investigation Management on AWS
Manufacturing & Industrial
Investigation types
Workplace safety incidents, equipment failures, quality incidents, environmental releases
Key drivers
OSHA, EPA, WorkSafe, HSE, quality management systems
Financial Services
Investigation types
Fraud investigations, compliance violations, trading misconduct, AML investigations
Key drivers
SOX, SEC, FINRA, FCA, AML regulations
Healthcare
Investigation types
Patient safety incidents, workplace injuries, compliance investigations, data breach investigations
Key drivers
HIPAA, CMS, state health department regulations, patient safety reporting
Government & Public Sector
Investigation types
Workplace complaints, internal affairs, regulatory enforcement, fraud investigations
Key drivers
Public sector accountability frameworks, whistleblower statutes, administrative law
Energy & Utilities
Investigation types
Safety incidents, environmental incidents, regulatory compliance investigations, operational failures
Key drivers
OSHA, EPA, FERC, state utility commissions, pipeline safety regulations
Technology & Higher Education
Investigation types
Security incidents, data breaches, compliance violations, Title IX investigations, research misconduct
Key drivers
GDPR, SOC 2, data breach notification laws, Title IX, research integrity frameworks
Deployment Models
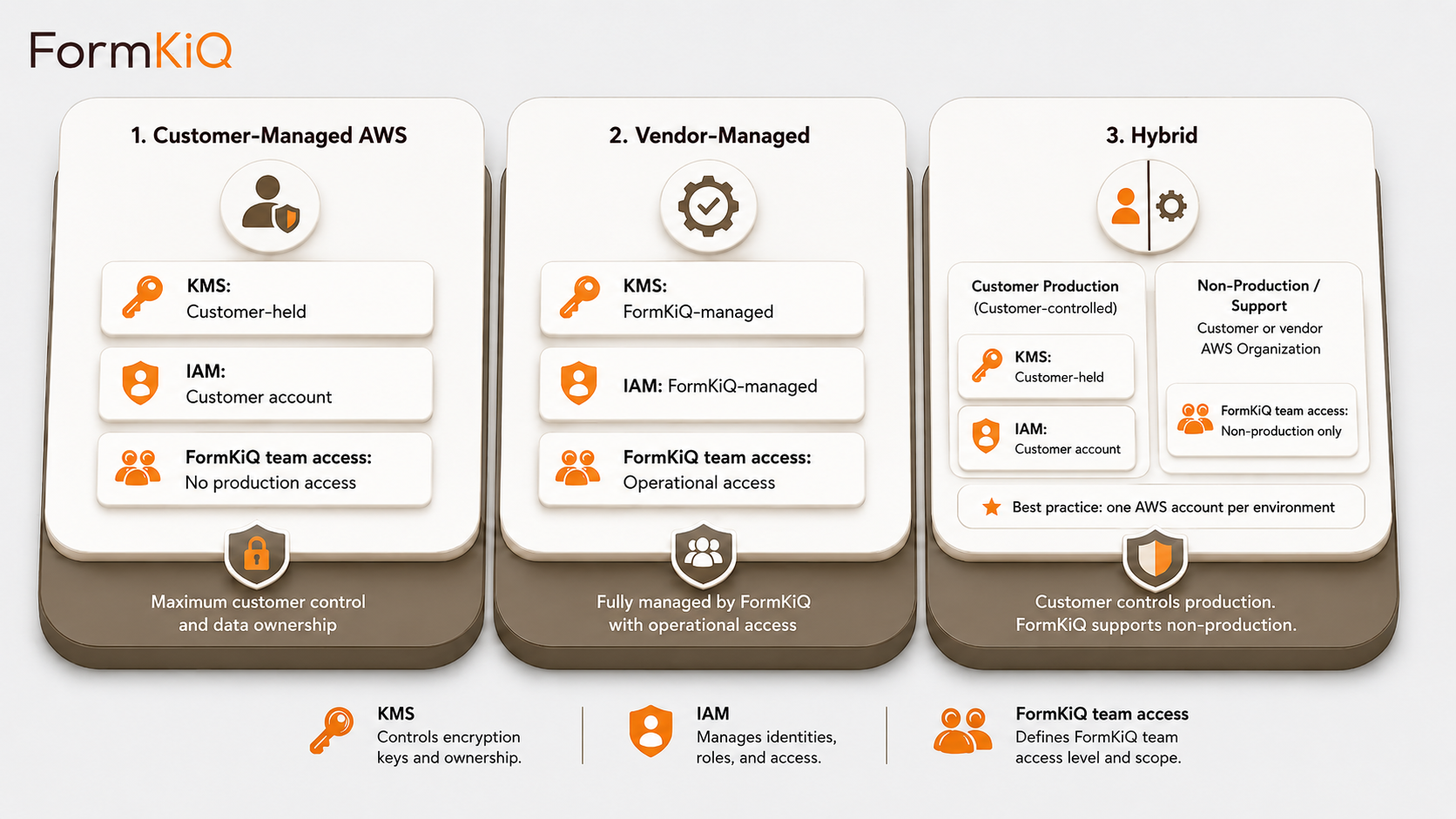
Every deployment is a dedicated, isolated instance in an AWS account owned by or designated by the customer. FormKiQ does not operate a shared multi-tenant environment.
- Customer-Managed AWS — deploys directly into your AWS account via CloudFormation; full control of infrastructure, networking, encryption keys, and operations; available on all editions
- Vendor-Managed — FormKiQ manages the AWS infrastructure on your behalf; available on Enterprise
- Hybrid — you retain control of specific components while delegating operational management to FormKiQ; available on Enterprise
Getting Started
FormKiQ Core can be deployed to your AWS account in fifteen to twenty minutes using a one-click install via AWS CloudFormation. Incident & Investigation Management capabilities — including AI Processing and Analysis, ABAC, Document Generation, and Workflow Automation — are available on FormKiQ Advanced and Enterprise.
For organizations evaluating investigation management on AWS, FormKiQ offers a Proof-of-Value program — a three-month deployment in a FormKiQ-managed AWS environment that provides full platform access in a non-production setting.
Start with FormKiQ Core
The open-source foundation — API-first, deployable into your own AWS account, and free to use. Right for architecture validation and early implementation.
Get Started Free →Deploy Advanced or Enterprise
Production-ready editions with AI Processing, ABAC, and Integration Frameworks. Start with a Proof-of-Value deployment or go straight to production.
Explore Options →Frequently Asked Questions
What is incident and investigation management on AWS?
Incident and investigation management on AWS refers to managing the document layer of the investigation lifecycle — incident reporting, evidence collection, assessment, investigation, findings, corrective action, and retention — on a platform deployed within your own Amazon Web Services environment. This gives organizations full control over investigation records, encryption, access, and audit trails without depending on a vendor-hosted platform.
How does FormKiQ use Amazon Bedrock for investigation management?
FormKiQ's AI Processing and Analysis module uses Amazon Bedrock to analyze investigation evidence and extract structured data — evidence classification, key entities, factual summaries, sensitivity indicators, and pattern indicators — automatically. All AI processing runs within your AWS account using Bedrock's supported large language models. Investigation content never leaves your cloud environment, and inference region controls ensure processing stays within your data residency boundaries.
How does FormKiQ protect investigation confidentiality?
FormKiQ's attribute-based access controls (ABAC) restrict investigation case files to designated investigation team members. Subjects of investigations and their management chains can be explicitly excluded. Witness identity information can be classified at a higher sensitivity level than incident facts. Whistleblower reporter identity can be protected through anonymized intake. All access events are recorded in the audit trail.
Can FormKiQ maintain chain of custody for evidence?
Yes. Every evidence document is recorded with source, receipt method, receipt timestamp, and receiving officer. Document versioning preserves the original evidence with immutable version history. Every access event is logged. Evidence transfers are documented with transfer metadata and acceptance confirmation. Evidence packages can be exported with integrity verification for legal proceedings or regulatory submission.
Does FormKiQ replace a dedicated EHS or case management system?
No. FormKiQ provides the governed document layer for investigations — evidence storage, classification, AI analysis, access controls, chain of custody, and retention. It integrates with EHS, HR, GRC, and case management systems through the Integration Framework, so investigation documents are linked to incident records, employee records, and compliance cases while FormKiQ serves as the system of record for the governed investigation file.
How does FormKiQ support regulatory reporting for incidents?
FormKiQ's Document Generation module produces regulatory reports from governed templates — OSHA 301 forms, WCB reports, RIDDOR reports, environmental incident reports, data breach notifications, and other required filings. Variable fields are populated from investigation metadata, incident data, and findings. Generated reports are stored within the investigation case file with filing confirmation metadata and full audit trail.