ISMS Documentation, Controlled Policies, Internal Audit Evidence, and Risk Treatment Records — on AWS Infrastructure Within Your Certification Boundary
ISO 27001 is a documentation-intensive standard. Certification requires not just that your organisation has implemented an information security management system (ISMS) — it requires that the ISMS is documented, that documents are controlled, that evidence of control operation is retained, and that all of this is producible for surveillance audits, recertification audits, and internal review. The standard's documented information requirements touch every aspect of the ISMS: policies, risk assessments, statements of applicability, risk treatment plans, procedures, work instructions, internal audit records, management review minutes, corrective action records, and evidence of competence.
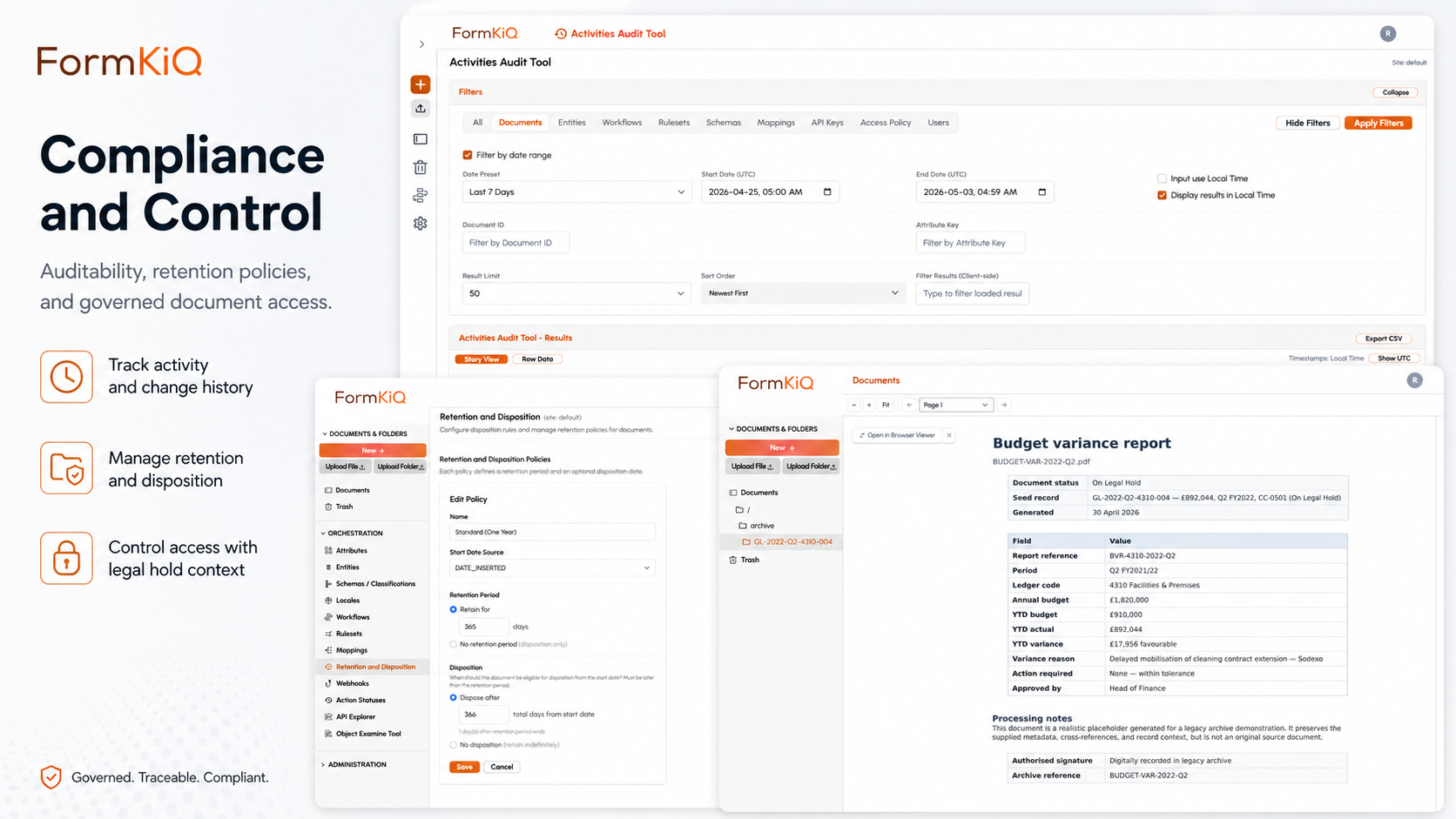
Most organisations pursuing or maintaining ISO 27001 certification manage these documents across shared drives, wikis, SharePoint sites, and standalone policy platforms — none of which provide the controlled document lifecycle that the standard actually requires. Documents get updated without version control. Policies are distributed without acknowledgment tracking. Internal audit evidence sits in email. Risk treatment records are spreadsheets. And when the certification auditor arrives, the ISMS manager spends days assembling evidence from multiple sources. FormKiQ provides document management on AWS with the controlled document lifecycle, version management, access controls, audit trails, and retention policies that ISO 27001 demands — deployed into your own AWS account so the ISMS infrastructure itself falls within your certification boundary and your existing AWS security controls apply directly.
ISO 27001 Documentation Requirements
ISO 27001:2022 specifies mandatory documented information and expects additional documentation to support control implementation. FormKiQ manages both categories.
Mandatory Documented Information
| ISO 27001 Clause | Required Documentation | FormKiQ Support |
|---|---|---|
| 4.3 | Scope of the ISMS | Document with version control, approval workflow, and publication — accessible to all relevant parties |
| 5.2 | Information security policy | Policy lifecycle management — authoring, review, approval, distribution, acknowledgment tracking, scheduled review |
| 6.1.2 | Information security risk assessment process | Process document with version control; risk assessment results stored as governed records |
| 6.1.3 | Information security risk treatment process | Risk treatment plan with version control; linked to Statement of Applicability |
| 6.1.3 d) | Statement of Applicability (SoA) | Governed document with version history; each version linked to the risk assessment that produced it |
| 6.2 | Information security objectives | Documented objectives with version control and review tracking |
| 7.2 | Evidence of competence | Training records, certifications, and competence assessments stored per employee with acknowledgment tracking |
| 8.1 | Operational planning and control | Procedures and work instructions with controlled versioning and distribution |
| 8.2 | Results of information security risk assessments | Risk assessment records retained with full version history, review dates, and reviewer identification |
| 8.3 | Results of information security risk treatment | Risk treatment records linked to risk assessments, SoA, and implementation evidence |
| 9.1 | Results of monitoring and measurement | Monitoring reports, metrics, and measurement records retained with timestamps |
| 9.2 | Internal audit programme and results | Audit plans, audit reports, findings, and corrective action records — see Internal Audit section below |
| 9.3 | Management review results | Management review minutes, decisions, and action items with attendee records and timestamps |
| 10.2 | Nonconformities and corrective actions | Nonconformity records, root cause analyses, corrective action plans, and evidence of effectiveness verification |
Annex A Control Documentation
Beyond the mandatory documented information, ISO 27001:2022 Annex A contains 93 controls across four themes — organisational, people, physical, and technological. While not all Annex A controls require formal documentation, many do, and auditors expect to see evidence that controls are implemented and operating. The table below shows the documentation commonly needed for each control theme:
| Annex A Theme | Example Controls | Documentation Needs |
|---|---|---|
| Organisational (A.5) | A.5.1 Policies, A.5.2 Roles, A.5.10 Acceptable use, A.5.31 Legal requirements | Policy documents, role descriptions, acceptable use policies, legal/regulatory registers |
| People (A.6) | A.6.1 Screening, A.6.2 Employment terms, A.6.3 Awareness/training, A.6.5 Termination | Background check records, employment agreements, training records, offboarding checklists |
| Physical (A.7) | A.7.1 Perimeters, A.7.4 Monitoring, A.7.10 Storage media | Physical security procedures, monitoring logs, media handling procedures |
| Technological (A.8) | A.8.1 User devices, A.8.5 Authentication, A.8.9 Configuration, A.8.24 Cryptography | Device policies, authentication procedures, configuration baselines, encryption policies |
Controlled Document Lifecycle
ISO 27001 Clause 7.5 specifies requirements for documented information — creation, updating, and control. This is where most organisations fail their audits. FormKiQ provides the controlled document lifecycle that Clause 7.5 requires:
| Clause 7.5 Requirement | What It Means | FormKiQ Capability |
|---|---|---|
| 7.5.2 — Creating and updating | Documents must be identified, described, formatted, reviewed, and approved | Metadata schemas for document identification; configurable review and approval workflows with audit trail |
| 7.5.3 — Control of documented information | Documents must be available and suitable for use where and when needed | Full-text and metadata search; ABAC controlling who can access which documents; current version always identifiable |
| 7.5.3 — Protection | Documents must be protected from loss of confidentiality, improper use, or loss of integrity | KMS encryption at rest and in transit; ABAC access controls; document versioning with integrity verification |
| 7.5.3 — Distribution, access, retrieval, and use | Controlled distribution with access appropriate to the audience | Targeted distribution by role, department, and classification; access audit trail; retrieval via search |
| 7.5.3 — Storage and preservation | Documents stored durably with preservation of legibility | Amazon S3 eleven-nines durability; format-agnostic storage; archival tiering |
| 7.5.3 — Control of changes | Changes tracked and version history maintained | Full version history with creation date, approval date, effective date, and supersession chain; version comparison |
| 7.5.3 — Retention and disposition | Documents retained as long as required and disposed of when no longer needed | Configurable retention policies; defensible disposition with audit trail; legal hold capability |
Internal Audit Documentation
Internal audits are one of the most document-intensive aspects of ISO 27001 maintenance. Clause 9.2 requires a planned audit programme, individual audit plans, audit reports with findings, and corrective action records with evidence of effectiveness verification. The quality of this documentation is one of the first things certification body auditors examine — if the internal audit programme documentation is weak, auditors question whether the ISMS itself is functioning effectively.
Audit Programme Management
| Document Type | What It Contains | FormKiQ Governance |
|---|---|---|
| Audit programme | Annual or multi-year audit schedule covering all ISMS processes and controls | Version control; approval workflow; scheduled review |
| Audit plans | Scope, objectives, criteria, and schedule for individual audits | Document generation from templates; metadata linking to audit programme |
| Audit checklists | Control-specific evaluation criteria and evidence requirements | Templates with version control; linked to SoA and control documentation |
| Audit reports | Findings, observations, evidence summaries, and conclusions | Structured reports with metadata classification (finding type, severity, control reference); approval workflow |
| Finding records | Individual nonconformities or observations with evidence references | Classification by type (major nonconformity, minor nonconformity, observation, opportunity for improvement); linked to corrective action records |
| Corrective action records | Root cause analysis, planned actions, implementation evidence, effectiveness verification | Workflow tracking from finding through closure; deadline monitoring; evidence of effectiveness linked to the original finding |
Auditor Access Control
- Auditor role — internal auditors granted time-limited read access to documents within the audit scope, without access to documents outside scope
- Audit independence — ABAC policies prevent auditors from accessing areas where they have operational responsibility (supporting auditor independence per Clause 9.2)
- External auditor access — certification body auditors granted temporary, scoped, read-only access with all access events audit-logged
- Audit evidence collection — documents identified as audit evidence linked to the finding or observation they support, with the linkage recorded in the audit trail
Risk Assessment and Treatment Documentation
The risk assessment is the engine of the ISMS — it determines which controls are needed, drives the Statement of Applicability, and justifies every security decision the organisation makes. ISO 27001 Clauses 6.1.2, 6.1.3, 8.2, and 8.3 require that both the risk assessment process and its results are documented and retained. Because risk assessments are repeated periodically and after significant changes, version control and historical access are essential — auditors need to see not just the current risk assessment, but the trajectory of how risk treatment decisions have evolved:
| Document Type | Description | FormKiQ Governance |
|---|---|---|
| Risk assessment methodology | Documented process for identifying, analysing, and evaluating information security risks | Policy lifecycle management with version control and scheduled review |
| Risk register | Register of identified risks with likelihood, impact, risk level, and treatment decisions | Governed document with version history; each assessment cycle produces a new version |
| Statement of Applicability (SoA) | List of all Annex A controls with inclusion/exclusion justification and implementation status | Governed document with full version history; linked to risk assessment; each version approved and dated |
| Risk treatment plan | Planned actions for treating identified risks, with owners, timelines, and resource requirements | Workflow tracking for treatment actions; deadline monitoring; evidence of treatment linked to the risk |
| Risk acceptance records | Documented acceptance of residual risks by authorised management | Approval workflow with signatory identification; retained as governed records |
Management Review Documentation
Management reviews are where senior leadership demonstrates their engagement with the ISMS — a requirement that auditors take seriously. Clause 9.3 specifies the inputs that management reviews must consider (status of actions, changes to the ISMS, feedback, risk assessment results) and requires that the results — decisions and actions — are documented. Weak or missing management review records are one of the most common findings in ISO 27001 surveillance audits:
| Document Type | What It Contains | FormKiQ Governance |
|---|---|---|
| Management review agenda | Topics for review as specified in Clause 9.3 — status of actions, changes, feedback, risk assessment results, opportunities for improvement | Document generation from templates; distribution to attendees |
| Management review minutes | Decisions, actions, and conclusions from the management review | Approval workflow (chair/secretary sign-off); distribution to attendees; retention per ISMS documentation retention policy |
| Action items | Actions arising from management review with owners and deadlines | Workflow tracking; deadline monitoring; evidence of completion linked to the originating review |
Policy Lifecycle for ISO 27001
ISO 27001 requires documented policies (Clause 5.2, Annex A.5.1) that are communicated, available, and reviewed. FormKiQ's Policy and Procedure Management capabilities directly support this:
- Authoring and approval — policies drafted, reviewed, and approved through configurable workflows with audit trail
- Version control — every version retained with effective date, approval date, and supersession chain
- Distribution and acknowledgment — policies distributed to applicable staff with individual eSignature acknowledgment and completion tracking
- Scheduled review — configurable review intervals (annual or custom) with automated reminders and review workflow
- Retirement — superseded or withdrawn policies retired with controlled access for historical reference
- Annex A.5.1 compliance — the policy lifecycle itself provides evidence that policies are defined, approved, published, communicated, and reviewed as the control requires
AI-Powered ISMS Document Processing
Managing an ISMS document library manually becomes increasingly difficult as the system matures — the volume of policies, procedures, audit records, risk assessments, and corrective actions grows with each audit cycle, and maintaining consistency and completeness across the library requires constant attention. FormKiQ's AI Processing and Analysis module — powered by Amazon Bedrock — automates the classification, analysis, and quality assurance tasks that ISMS managers typically perform manually. All AI processing runs within your AWS account; ISMS documentation content never leaves your cloud environment.
| AI Capability | ISMS Application |
|---|---|
| Document type classification | Automatically classify incoming ISMS documents — policies, procedures, audit reports, risk assessments, corrective action records — and file to the correct section of the ISMS document library |
| Gap analysis | Analyse the ISMS document library against ISO 27001:2022 requirements — identify missing mandatory documentation or controls without supporting evidence |
| Consistency analysis | Identify inconsistencies between related ISMS documents (e.g., policy conflicts, procedure/policy misalignment, SoA inconsistency with risk treatment plan) |
| Content summarisation | Summarise lengthy audit reports, risk assessments, or management review minutes for executive briefing |
| Control evidence mapping | Analyse control documentation against SoA requirements — identify controls with insufficient implementation evidence |
Including FormKiQ in Your ISMS Boundary
A key advantage of deploying FormKiQ in your own AWS account: the document management platform itself falls within your ISMS certification boundary. This eliminates the supplier management complexity that vendor-hosted document management platforms create. With a vendor-hosted DMS, the vendor is a third party whose security controls you must assess under Annex A.5.19–A.5.22 — and whose controls you cannot directly verify. With FormKiQ in your own account, the platform is part of your ISMS, covered by your controls, and auditable by your certification body as part of your own certification:
| Aspect | Vendor-Hosted DMS | FormKiQ in Your AWS Account |
|---|---|---|
| ISMS scope | DMS is outside your ISMS boundary — you rely on the vendor's own ISO 27001 certificate (if they have one) | FormKiQ is inside your ISMS boundary — covered by your own controls, your own risk assessment, your own audit programme |
| Access controls | Managed by the vendor; you review their controls via their SOC 2 or ISO 27001 report | Managed by you in Cognito/IAM; your auditor examines your controls directly |
| Encryption | Managed by the vendor; you trust their key management | Managed by you in KMS; your keys, your key policies, your rotation schedule |
| Monitoring | Managed by the vendor; you review their monitoring reports | Managed by you in CloudWatch/CloudTrail; your thresholds, your alerts, your incident response |
| Change management | Managed by the vendor; you rely on their change control process | Managed by you via CloudFormation; your change process, your approval, your testing |
| Supplier management (A.5.19–A.5.22) | The DMS vendor is a supplier you must assess and monitor under Annex A supplier controls | FormKiQ runs in your account — AWS is the supplier you assess (and AWS carries its own ISO 27001 certification) |
Compliance with Related Standards
ISO 27001 rarely exists in isolation. Most organisations implementing an ISMS are also pursuing SOC 2, complying with GDPR, aligning with NIST CSF, or running an integrated management system alongside ISO 9001 or ISO 14001. The documentation overlap between these frameworks is substantial — a well-managed policy lifecycle, internal audit programme, and risk assessment process serves multiple standards simultaneously. FormKiQ supports documentation across the ISO 27000 family and adjacent frameworks, enabling organisations to maintain a single governed document library rather than duplicating documentation per framework:
| Standard / Framework | Relationship to ISO 27001 | FormKiQ Support |
|---|---|---|
| ISO 27002:2022 | Controls guidance — detailed implementation guidance for Annex A controls | Control documentation, procedure management, evidence retention |
| ISO 27701 | Privacy Information Management System (PIMS) — extends ISO 27001 for privacy | Privacy policy management, processing records, data subject rights workflows, DPIA documentation |
| ISO 27017 | Cloud security controls — additional controls for cloud environments | Cloud security policy management, shared responsibility documentation |
| ISO 27018 | PII protection in public clouds — additional controls for cloud-based PII processing | PII handling procedures, consent records, processing documentation |
| ISO 9001 | Quality management system — overlapping documentation and audit requirements | Integrated document control; shared internal audit programme documentation |
| SOC 2 | Trust services criteria — complementary to ISO 27001 controls | Shared evidence base; policies and audit records serving both frameworks |
| NIST CSF | Cybersecurity framework — mappable to ISO 27001 controls | Documentation supporting both ISO 27001 Annex A and NIST CSF categories |
Who Uses ISO 27001 Document Management on AWS
ISO 27001 certification has become a baseline expectation across industries — driven by customer requirements, regulatory frameworks, and the competitive need to demonstrate security maturity. The organisations pursuing certification share a common challenge: the ISMS documentation burden grows with the organisation's size and complexity, and managing that documentation in shared drives or wikis creates the exact kind of uncontrolled document environment that the standard is designed to prevent:
| Organisation Type | ISMS Documentation Needs | Key Drivers |
|---|---|---|
| Technology and SaaS | ISMS documentation for customer assurance; controlled policies; internal audit records; vendor assessments | Customer requirements; competitive differentiation; enterprise sales enablement |
| Financial services | ISMS integrated with regulatory compliance documentation; audit evidence across ISO 27001 and financial regulations | Regulatory requirements (FCA, APRA, OSFI); client due diligence; multi-framework compliance |
| Healthcare and life sciences | ISMS integrated with health data protection; GxP documentation; clinical system qualification | ISO 27001 + HIPAA/GDPR; regulatory submission support; clinical data integrity |
| Professional services | Multi-office ISMS documentation; client confidentiality controls; partner-level governance | Client requirements; professional body requirements; multi-jurisdiction operations |
| Manufacturing | Integrated management systems (ISO 27001 + ISO 9001 + ISO 14001); supply chain security documentation | Customer requirements; supply chain security; integrated management system efficiency |
| Government and public sector | ISMS documentation for government security requirements; controlled document management for classified environments | National security frameworks; procurement requirements; inter-agency compliance |
| Education and research | Research data security; institutional ISMS; student data protection | Research funder requirements; institutional accreditation; data protection legislation |
| Managed service providers | ISMS documentation supporting client assurance; evidence production for client audits | Client contractual requirements; market differentiation; multi-client evidence management |
FormKiQ Editions for ISO 27001 Document Management
| Capability | Core Foundation |
Essentials Operational |
Advanced AI + Automation |
Enterprise Full platform |
|---|---|---|---|---|
| Foundation | ||||
| Document Storage (S3) & API | ||||
| Tagging, Search & Classification | ||||
| OCR (Tesseract) | ||||
| Essentials and above | ||||
| OCR & IDP (Textract) | — | |||
| SSO (SAML — Entra, Google, Auth0) | — | |||
| Workflows, Queues & Rulesets | — | |||
| Encryption (KMS — in-transit & at-rest) | — | |||
| Document Control & Versioning | — | |||
| Antivirus & Anti-Malware | — | |||
| Advanced and Enterprise | ||||
| AI Processing & Analysis (Bedrock) | — | — | ||
| Document Generation | — | — | ||
| eSignature Integration | — | — | ||
| Document Gateway Modules | — | — | ||
| Enhanced Full-Text Search (OpenSearch) | — | — | ||
| Multi-Instance & Multi-Region Licensing | — | — | ||
| Enterprise only | ||||
| Vendor-Managed & Hybrid Deployment | — | — | — | |
| Custom SLAs & Compliance Consulting | — | — | — | |
| Support | ||||
| Support | Community (Slack & GitHub) | Support Portal (2-business-day SLA) | Private Slack + videoconference + 40 hrs onboarding | Rapid response (8-business-hour SLA) + strategic architecture support |
Deployment Models
| Model | Description | Availability |
|---|---|---|
| Customer-Managed AWS | Deploys directly into your AWS account via CloudFormation. Full control of infrastructure, networking, encryption keys, and operations. Falls within your ISMS certification boundary. | All editions |
| Vendor-Managed | FormKiQ manages the AWS infrastructure on your behalf — deployment, updates, and operational support. | Enterprise |
| Hybrid | You retain control of specific components (encryption keys, network config) while delegating operational management to FormKiQ. | Enterprise |
Every deployment is a dedicated, isolated instance. FormKiQ does not operate a shared multi-tenant environment.
Getting Started
FormKiQ Core can be deployed to your AWS account in fifteen to twenty minutes. ISO 27001 ISMS documentation capabilities — including policy lifecycle management, AI-powered gap analysis, document generation, and eSignature integration — are available on FormKiQ Advanced and Enterprise.
For organisations pursuing or maintaining ISO 27001 certification, FormKiQ offers a Proof-of-Value program — a three-month deployment in a FormKiQ-managed AWS environment that provides full platform access in a non-production setting.
Frequently Asked Questions
Is FormKiQ ISO 27001-certified?
FormKiQ deploys into your own AWS account, which means it falls within your ISMS certification boundary — covered by your own controls and audited as part of your own ISO 27001 certification. AWS, as the underlying infrastructure provider, carries its own ISO 27001 certification. FormKiQ as an application does not carry an independent ISO 27001 certificate because it runs in your environment, not ours.
How does deploying in my own AWS account help with ISO 27001?
When FormKiQ runs in your AWS account, the document management platform is inside your ISMS boundary. Your existing AWS security controls — access management, encryption, monitoring, incident response, change management — apply directly to FormKiQ. Your internal auditors and certification body auditors examine your infrastructure, not a vendor's. This eliminates the supplier management complexity of relying on a vendor-hosted document management platform.
Can FormKiQ manage the full set of ISO 27001 mandatory documented information?
Yes. FormKiQ supports all 14 categories of mandatory documented information specified in ISO 27001:2022 — from the ISMS scope and information security policy through risk assessment results, internal audit records, management review minutes, and corrective action records. Each document type is managed within a controlled lifecycle with version control, approval workflows, and retention policies.
How does FormKiQ support Clause 7.5 requirements for controlled documented information?
Clause 7.5 requires that documented information is identified, described, reviewed, approved, available, protected, distributed with controlled access, stored durably, change-controlled, and retained appropriately. FormKiQ provides all of these capabilities through metadata schemas (identification), approval workflows (review and approval), ABAC (access control), KMS encryption (protection), full-text search (availability and retrieval), version control (change management), and configurable retention policies (retention and disposition).
How does FormKiQ support the internal audit programme?
FormKiQ manages the audit documentation lifecycle — audit programmes, audit plans, checklists, audit reports, finding records, and corrective action records — with workflows tracking findings from identification through root cause analysis, corrective action, and effectiveness verification. Auditor access controls support auditor independence by restricting access to documents within the audit scope. Certification body auditors can be granted temporary, scoped, read-only access with all access events audit-logged.
Can FormKiQ support integrated management systems (ISO 27001 + ISO 9001 + ISO 14001)?
Yes. Organisations operating integrated management systems can manage all documentation within a single FormKiQ deployment — sharing common document control, internal audit, management review, and corrective action processes across management system standards. This eliminates documentation duplication and supports the integrated audit approach.
How does FormKiQ handle the transition from ISO 27001:2013 to ISO 27001:2022?
Organisations transitioning from the 2013 to 2022 version need to update their SoA, revise documentation to reflect the new Annex A control structure (four themes replacing 14 domains, 93 controls replacing 114), and demonstrate implementation of 11 new controls. FormKiQ's version control maintains the complete documentation history — both the pre-transition and post-transition versions — with audit evidence of the review, approval, and implementation process.