Guide quick menu
Governed Policy Lifecycle — Authoring, Approval, Distribution, Acknowledgment Tracking, and Version Control — on AWS Infrastructure You Control
Every regulated organisation depends on internal policies and procedures to define how it operates, complies with legislation, manages risk, and sets expectations for staff conduct. But managing policies as documents — not just as concepts — is where most organisations struggle. Policies are drafted in Word documents emailed between reviewers. Approved versions are uploaded to intranets where they sit alongside outdated drafts. Distribution is an email with an attachment. Acknowledgment tracking is a spreadsheet. And when a regulator, auditor, or tribunal asks for proof that a specific policy was in effect on a specific date and that relevant staff had acknowledged it, the compliance team reconstructs evidence from email archives and best guesses.
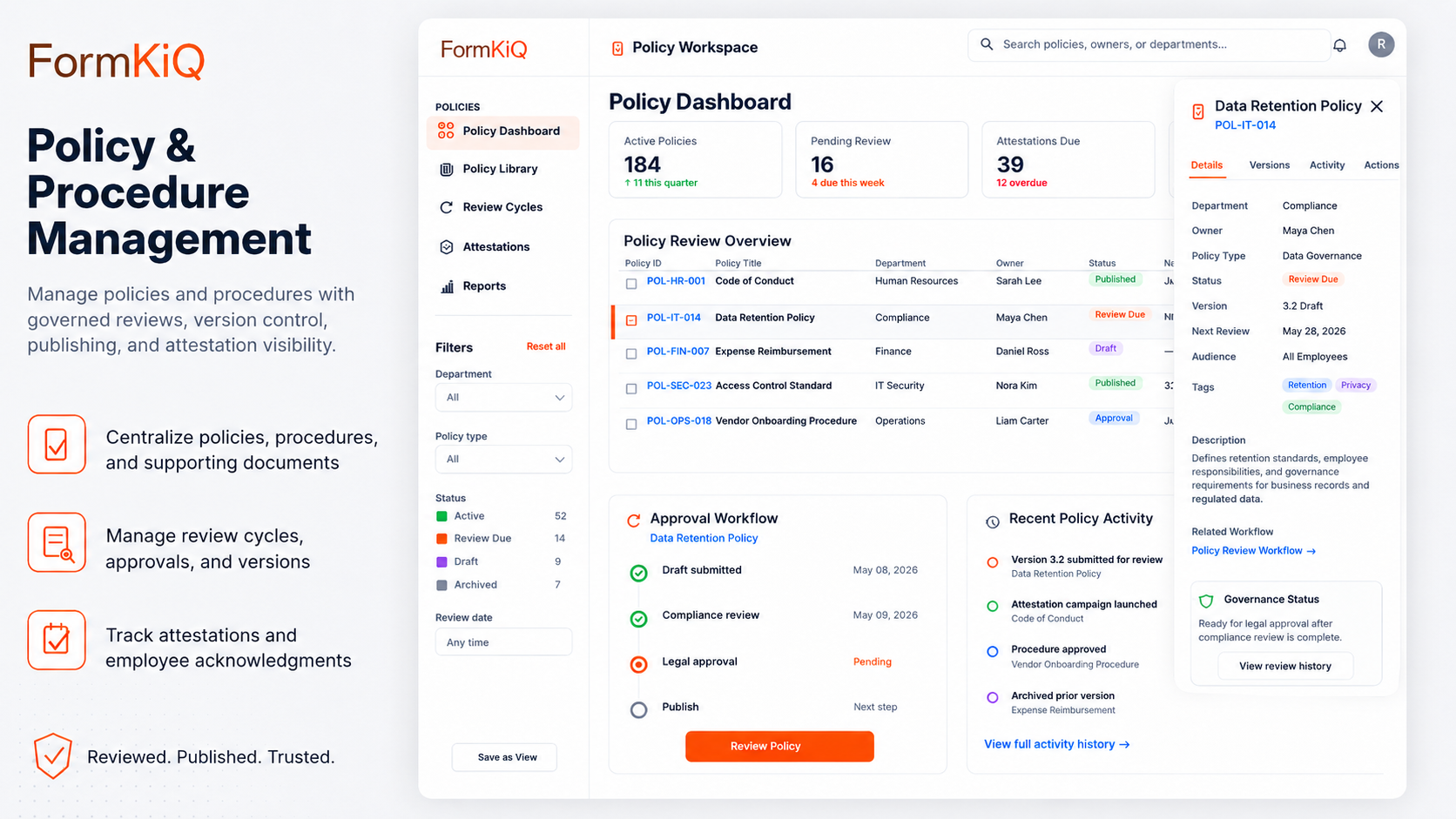
FormKiQ's Policy and Procedure Management solution provides a governed document lifecycle for organisational policies and procedures — from authoring and review through approval, controlled publication, targeted distribution, individual acknowledgment tracking, scheduled review cycles, and version-controlled archival. Deployed directly into your AWS account, FormKiQ gives compliance teams, policy owners, and senior leadership a single auditable system for demonstrating that policies exist, are current, have been properly approved, and have been communicated to the people they apply to.
Why Policy Management Is a Document Management Problem
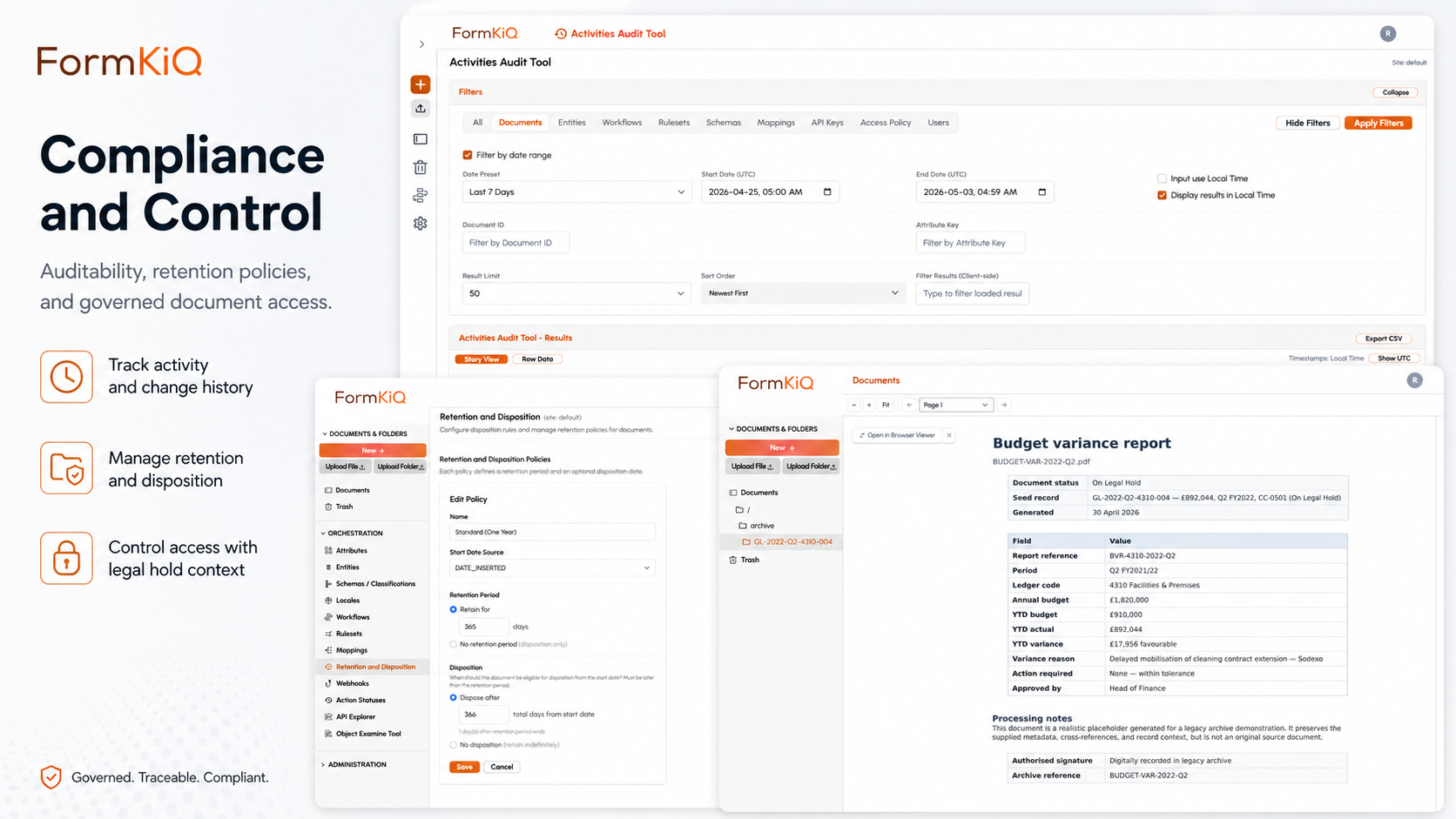
Policy management platforms exist as standalone tools — but they typically operate as workflow and distribution layers on top of unmanaged document storage. The policies themselves lack the governance controls that regulated organisations need: version integrity, document-level audit trails, retention policies, legal hold, and integration with the broader document management and records management programme.
FormKiQ approaches policy management as a governed document lifecycle within the same platform that manages contracts, employee records, vendor documentation, and every other governed document type. This means:
| Standalone Policy Platform | Policy Management in FormKiQ |
|---|---|
| Policy documents stored in platform-specific format with limited export | Policies stored as governed documents in standard formats on S3 — accessible through API, console, or integration |
| Version history maintained by the policy platform only | Version history maintained within the governed document lifecycle with audit trail, retention, and legal hold |
| Acknowledgments tracked in the policy platform's database | Acknowledgments stored as governed documents — individually signed, audit-logged, and retained per policy |
| Retention and archival managed by the policy platform | Retention and archival governed by the same policies that manage all other organisational documents |
| Isolated from other document management and records management | Policies managed alongside contracts, employee records, vendor documents, and case files within a unified governance framework |
The Policy Document Lifecycle
A policy isn't a static document — it moves through a defined lifecycle from initial drafting through eventual retirement, and the governance applied at each stage determines whether the organisation can demonstrate compliance when it matters. Most organisations handle the early stages reasonably well (drafting and approval) but lose control at publication, distribution, and especially review cycles — which is precisely where auditors focus. FormKiQ supports each stage within a governed, auditable platform:
| Lifecycle Stage | What Happens | How FormKiQ Handles It |
|---|---|---|
| Authoring | Policy content drafted by policy owner or subject matter expert | Document creation with metadata (policy type, department, applicable jurisdiction, regulatory reference); version control from first draft |
| Review | Draft reviewed by stakeholders — legal, compliance, HR, operations, subject matter experts | Multi-step review workflows with role-based task assignment; reviewer comments and tracked changes captured in document history |
| Approval | Final draft approved by authorised approver(s) — department head, compliance officer, executive, board | Configurable approval workflows with sequential or conditional approval chains; approval decisions audit-logged with timestamps and approver identification |
| Publication | Approved policy made available to applicable staff | Controlled publication with effective date, supersession of prior version, and access controls governing who can view the current policy |
| Distribution | Policy distributed to applicable staff segments | Targeted distribution based on department, location, role, jurisdiction, or custom attributes; distribution records captured |
| Acknowledgment | Staff acknowledge receipt and understanding of the policy | Individual eSignature acknowledgment with timestamp; completion tracking dashboards; automated follow-up for outstanding acknowledgments |
| Active Period | Policy in effect — referenced by staff, auditors, and management | Full-text search; metadata search; current version clearly distinguished from prior versions; access audit trail |
| Scheduled Review | Policy reviewed at defined intervals to ensure it remains current and compliant | Automated review reminders at configurable intervals (annual, biennial, or custom); review workflow triggered for policy owner |
| Revision | Policy updated based on regulatory changes, operational changes, or review findings | New version created; revision workflow follows same review/approval/publication cycle; prior version archived with full history |
| Retirement | Policy no longer applicable — superseded, withdrawn, or expired | Retirement workflow with approval; retired policy retained in archive with retirement date and reason; access restricted to historical reference |
| Retention & Archive | Retired policies retained per regulatory and organisational requirements | Configurable retention from retirement date; archived to cost-optimised S3 storage; remains searchable and producible for audit |
Version Control for Policies
Policy version control is not just a convenience — it's a compliance requirement. Regulated organisations must be able to demonstrate which version of a policy was in effect on any given date, and what process was followed to approve it. This matters most during investigations, tribunal proceedings, and regulatory examinations, where the question is often "what was the policy at the time of the incident?" — not "what is the policy today?" FormKiQ's version control provides a complete, auditable chain of policy evolution:
| Capability | Description |
|---|---|
| Complete version history | Every version of every policy retained with creation date, approval date, effective date, and supersession date |
| Current version identification | The current effective version is clearly distinguished from prior versions — staff accessing the policy always see the current version unless specifically requesting historical reference |
| Prior version access | Prior versions accessible for historical reference, audit, and legal proceedings — with clear labelling that they are not the current version |
| Version comparison | Ability to identify what changed between versions — supporting review workflows and audit evidence |
| Effective date management | Policies can have future effective dates — approved and ready for publication on a specified date |
| Supersession records | Each version records which prior version it superseded and which subsequent version replaced it — creating a complete chain of policy evolution |
| Audit trail per version | Every version has its own audit trail — authoring, review, approval, publication, distribution, and acknowledgment events all recorded against the specific version |
Distribution and Acknowledgment Tracking
Distribution and acknowledgment are where policy governance either succeeds or fails. FormKiQ provides structured distribution with individual acknowledgment tracking.
Targeted Distribution
Policies are distributed to specific audiences based on metadata-driven rules:
- By department — policies applicable to specific departments distributed only to those departments
- By location / jurisdiction — jurisdiction-specific policies distributed to staff in the applicable jurisdiction
- By role — role-specific policies (e.g., manager policies, clinical policies, financial policies) distributed to staff in the relevant roles
- By employment type — different policy sets for permanent, contract, and temporary staff
- By custom attribute — any metadata-based segmentation supported by the organisation's HR or identity data
Acknowledgment Tracking
Distribution without acknowledgment is distribution without evidence. When a regulator asks whether staff were aware of a policy, "we emailed it to them" is not a defensible answer — "each employee signed an individual acknowledgment on this date, and here's the record" is. FormKiQ treats every acknowledgment as a governed document in its own right, linked to both the specific policy version and the employee's record:
| Capability | Description |
|---|---|
| Individual eSignature | Each staff member signs an electronic acknowledgment specific to the policy version distributed — with timestamp, signer identity, and policy version recorded |
| Completion dashboards | Real-time visibility into acknowledgment completion rates by department, location, role, and individual |
| Outstanding acknowledgments | Clear identification of staff who have not yet acknowledged — with automated reminder workflows at configurable intervals |
| Deadline enforcement | Acknowledgment deadlines with escalation rules — overdue acknowledgments flagged to managers or compliance |
| New hire distribution | Policies automatically distributed to new hires as part of onboarding workflows — with acknowledgment tracked alongside other onboarding documents |
| Re-acknowledgment on revision | When a policy is revised, re-acknowledgment workflows automatically triggered for applicable staff |
| Acknowledgment as governed document | Each signed acknowledgment stored as a governed document in the employee record — retained per policy, subject to audit trail and legal hold |
Scheduled Review Cycles
Policies that are not periodically reviewed become compliance liabilities — and one of the most common audit findings across ISO 27001, SOC 2, and healthcare accreditation programmes is policies that haven't been reviewed since they were first approved. The review cycle isn't optional for most regulatory frameworks, but tracking it manually in spreadsheets or calendars is fragile and easy to neglect. FormKiQ automates the review cycle so that overdue reviews surface on dashboards rather than in audit findings:
| Feature | Description |
|---|---|
| Configurable review intervals | Review periods set per policy — annual, biennial, triennial, or custom intervals based on regulatory requirements |
| Automated review reminders | Policy owners and reviewers notified at configurable advance intervals before the review date |
| Review workflow trigger | When the review date arrives, a review workflow is automatically initiated — routing the policy to the owner and designated reviewers |
| Review outcomes | Three outcomes: confirmed (no changes needed — review date reset), revised (revision workflow initiated), or retired (retirement workflow initiated) |
| Overdue review tracking | Policies past their review date flagged on compliance dashboards — with escalation to compliance leadership |
| Review history | Every review cycle recorded in the policy's audit trail — date, reviewer, outcome, and any resulting action |
AI-Powered Policy Document Processing
As an organisation's policy library grows — across departments, jurisdictions, and regulatory frameworks — keeping policies consistent, complete, and current becomes a significant operational burden. A regulatory change in one jurisdiction may affect multiple policies. A new policy may conflict with existing provisions elsewhere in the library. Gaps in coverage may go unnoticed until an auditor identifies them. FormKiQ's AI Processing and Analysis module — powered by Amazon Bedrock — helps policy teams manage this complexity at scale. All AI processing runs within your AWS account; policy content never leaves your cloud environment.
| AI Capability | Policy Management Application |
|---|---|
| Regulatory change analysis | Analyse regulatory updates against existing policy content — identify policies that may need revision based on legislative or regulatory changes |
| Policy gap analysis | Assess the policy library against regulatory requirements or industry frameworks — identify areas where policies are missing or incomplete |
| Consistency analysis | Analyse policies for internal consistency — identify conflicting provisions across related policies |
| Content summarisation | Generate plain-language summaries of complex policies for distribution to non-specialist audiences |
| Classification | Automatically classify policy documents by type, department, regulatory reference, and jurisdiction |
Policy and Procedure Document Types
"Policies" is a broad category. In practice, an organisation's policy library includes documents at several levels of detail — from high-level governance policies set by the board through operational policies, standard operating procedures, clinical procedures, work instructions, and guidelines. Each level has different authoring, approval, distribution, and review requirements, and FormKiQ's metadata schemas support classification and governance at each level:
| Document Type | Description | Example |
|---|---|---|
| Governance policies | High-level organisational policies set by the board or executive leadership | Code of conduct, anti-bribery and corruption policy, whistleblower policy, data protection policy |
| Operational policies | Policies governing day-to-day operations within departments or functions | Procurement policy, travel and expense policy, remote work policy, acceptable use policy |
| Compliance policies | Policies required by specific regulatory frameworks | Anti-money laundering policy, conflict of interest policy, insider trading policy, clinical governance policy |
| HR policies | Policies governing the employment relationship | Equal opportunity policy, grievance policy, disciplinary policy, leave policy, health and safety policy |
| IT and security policies | Policies governing technology use, data handling, and information security | Information security policy, data classification policy, incident response policy, BYOD policy |
| Standard operating procedures (SOPs) | Step-by-step instructions for specific operational processes | Patient intake procedure, account opening procedure, incident reporting procedure |
| Clinical and care procedures | Procedures governing clinical practice and patient/client care | Medication administration procedure, infection control procedure, safeguarding procedure |
| Work instructions | Detailed instructions for specific tasks — more granular than SOPs | Equipment calibration instructions, quality inspection instructions, safety check procedures |
| Guidelines and standards | Non-mandatory guidance that supports policy implementation | Style guides, communication guidelines, best practice standards |
Access Control for Policies
Not all policies should be visible to all staff. Draft policies undergoing review should not be accessible to the general workforce. Jurisdiction-specific policies should be visible only to staff in that jurisdiction. Sensitive policies — security incident response procedures, executive compensation frameworks, investigation protocols — should be restricted to authorised roles. And prior versions should be clearly marked as non-current while remaining accessible for audit and legal reference:
| Access Layer | What It Controls | Example |
|---|---|---|
| Publication status | Only approved, published policies visible to general staff — drafts and under-review versions restricted to authors and reviewers | Staff see only the current approved version; policy team sees drafts, reviews, and prior versions |
| Audience segmentation | Policies visible only to the staff they apply to | Clinical policies visible to clinical staff; financial policies visible to finance staff |
| Jurisdiction | Jurisdiction-specific policies visible only to staff in that jurisdiction | UK-specific HR policies visible only to UK-based staff |
| Confidentiality | Sensitive policies (executive compensation, security procedures, investigation protocols) restricted to authorised roles | Security incident response procedures restricted to IT security team and senior management |
| Historical access | Prior versions accessible for audit and legal reference — clearly marked as non-current | Auditors can access the version of a policy that was in effect on a specific date |
Integration with Other FormKiQ Solutions
One of the strongest arguments for managing policies within FormKiQ rather than in a standalone policy platform is the connection to other governed document types. Policies don't exist in isolation — they're referenced in contracts, acknowledged by employees, required of vendors, cited in investigations, and managed as organisational records. When policies live in a separate system, these connections are manual and fragile. When they live in FormKiQ, the connections are structural:
| Connected Solution | How Policies Connect |
|---|---|
| HR and Employee Records | Policy acknowledgments filed in the employee record; onboarding policy distribution automated as part of the employee onboarding workflow |
| Contract Management | Policy references embedded in contracts and agreements; policy compliance linked to contractual obligations |
| Vendor and Supplier Document Management | Vendor code of conduct and compliance policy acknowledgments collected and tracked as part of vendor onboarding |
| Case Management | Policies referenced in investigation and complaint proceedings; policy versions in effect at the time of an incident producible for case review |
| Records Management | Policies managed as organisational records — subject to records retention schedules, legal hold, and defensible disposition |
Compliance and Regulatory Alignment
Nearly every regulatory and accreditation framework requires documented policies that are version-controlled, communicated to staff, and periodically reviewed. The specific policies required vary by framework, but the governance model is consistent — and it's the governance model, not just the policy content, that auditors evaluate. FormKiQ's policy lifecycle addresses the common requirements across these frameworks:
| Framework | Policy Management Requirements | FormKiQ Capabilities |
|---|---|---|
| ISO 9001 / ISO 14001 / ISO 27001 | Documented policies, controlled versions, review cycles, evidence of communication | Version control, approval workflows, distribution tracking, acknowledgment records, review cycle automation |
| SOC 2 | Documented information security policies, evidence of communication and acknowledgment | Policy lifecycle management, acknowledgment tracking, audit trail |
| GDPR / UK GDPR | Data protection policies documented, communicated, and reviewed | Policy lifecycle, distribution to applicable staff, acknowledgment tracking, review cycles |
| PIPEDA / Provincial privacy legislation (Canada) | Privacy policies documented and communicated | Policy lifecycle, distribution tracking, acknowledgment records |
| FCA / APRA / OSFI regulatory requirements | Compliance policies documented, approved by senior management, communicated to staff | Approval workflows with audit trail, distribution tracking, acknowledgment records, review cycles |
| Healthcare accreditation (JCI, ACHS, CQC) | Clinical policies and procedures documented, version-controlled, communicated, and periodically reviewed | Full policy lifecycle, version control, distribution, acknowledgment, scheduled review |
| Workplace health and safety legislation | Safety policies documented, communicated, and acknowledged by workers | Policy distribution, individual acknowledgment with eSignature, retention |
| Anti-money laundering regulations | AML policies documented, approved, communicated, and regularly reviewed | Approval workflows, distribution tracking, acknowledgment records, review cycle automation |
| Anti-bribery and corruption legislation | Anti-corruption policies documented, communicated to staff and third parties, with acknowledgment evidence | Distribution to staff and vendors, acknowledgment tracking, vendor policy acknowledgment via vendor portal |
Who Uses Policy and Procedure Management on AWS
Policy and procedure management is a universal need — every regulated organisation has policies, and every audited organisation needs evidence that those policies are governed. The specifics vary by industry: financial services firms manage regulatory policy libraries that change with every legislative cycle; healthcare organisations manage clinical procedures that directly affect patient safety; manufacturers manage SOPs that quality auditors examine in detail. But the underlying requirement — controlled documents, evidenced distribution, tracked acknowledgment, scheduled review — is the same:
| Industry | Policy Management Challenges | Key Drivers |
|---|---|---|
| Financial Services and Insurance | Regulatory policy library spanning multiple jurisdictions; frequent regulatory change driving policy revisions; audit evidence of staff acknowledgment | FCA, APRA, OSFI, FINRA requirements; SOC 2; regulatory examination readiness |
| Healthcare | Clinical policies and procedures requiring version control, scheduled review, and evidence of communication to clinical staff | Accreditation (JCI, ACHS, CQC); clinical governance; patient safety; regulatory compliance |
| Government and Public Sector | Large policy libraries across departments and agencies; multi-jurisdiction policy requirements; evidence of policy communication to public servants | Legislative compliance; audit readiness; transparency requirements |
| Higher Education | Institutional policies spanning academic, administrative, research, and student conduct domains; multi-campus distribution | Accreditation; research compliance; student and staff policy acknowledgment |
| Manufacturing | Safety procedures, quality SOPs, and environmental policies requiring version control, training acknowledgment, and audit evidence | ISO 9001/14001; workplace safety legislation; quality audit readiness |
| Energy and Utilities | Safety policies, operational procedures, and environmental compliance policies across distributed operations | Workplace safety legislation; environmental regulation; operational safety audit |
| Professional Services | Firm-wide policies across offices and jurisdictions; partner-level approval workflows; client-facing policy requirements | Professional regulatory bodies; multi-jurisdiction compliance; client audit requirements |
| Technology | Information security policies, data handling procedures, and compliance policies updated frequently as regulations and threats evolve | SOC 2; ISO 27001; GDPR; customer security assessment responses |

FormKiQ Editions for Policy and Procedure Management
| Capability | Core Foundation |
Essentials Operational |
Advanced AI + Automation |
Enterprise Full platform |
|---|
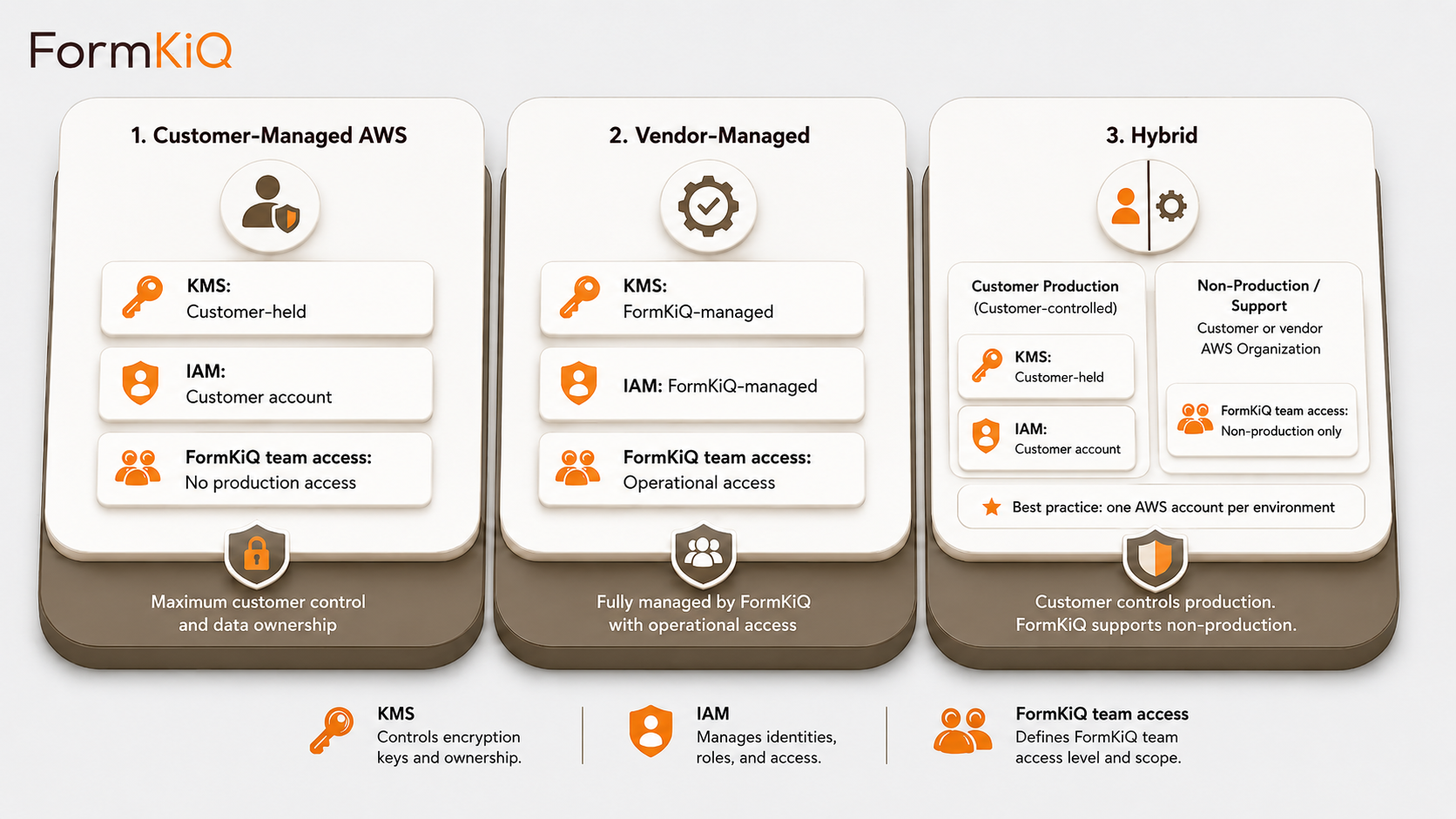
Deployment Models
| Model | Description | Availability |
|---|---|---|
| Customer-Managed AWS | Deploys directly into your AWS account via CloudFormation. Full control of infrastructure, networking, encryption keys, and operations. | All editions |
| Vendor-Managed | FormKiQ manages the AWS infrastructure on your behalf — deployment, updates, and operational support. | Enterprise |
| Hybrid | You retain control of specific components (encryption keys, network config) while delegating operational management to FormKiQ. | Enterprise |
Every deployment is a dedicated, isolated instance in an AWS account owned by or designated by the customer. FormKiQ does not operate a shared multi-tenant environment.
Getting Started
FormKiQ Core can be deployed to your AWS account in fifteen to twenty minutes using a one-click install via AWS CloudFormation. Policy and Procedure Management capabilities — including AI Processing, Document Generation, eSignature Integration, and scheduled review automation — are available on FormKiQ Advanced and Enterprise.
For organisations evaluating policy and procedure management on AWS, FormKiQ offers a Proof-of-Value program — a three-month deployment in a FormKiQ-managed AWS environment that provides full platform access in a non-production setting.
Frequently Asked Questions
What is policy and procedure management on AWS?
Policy and procedure management on AWS refers to managing the full policy document lifecycle — authoring, review, approval, publication, distribution, acknowledgment tracking, scheduled review, version control, and retention — in a governed document management platform deployed within your own Amazon Web Services environment.
Why not use a standalone policy management platform?
Standalone policy platforms manage the policy workflow (authoring, approval, distribution, acknowledgment) but typically store policy documents in platform-specific formats with limited governance. FormKiQ manages policies as governed documents within the same platform that manages contracts, employee records, vendor documents, and all other organisational content — with full version control, audit trails, retention policies, legal hold, and records management integration. Policy acknowledgments are stored as governed documents in the employee record, creating a complete chain of evidence from policy approval through individual acknowledgment.
How does version control work for policies?
Every version of every policy is retained with creation date, approval date, effective date, and supersession date. The current effective version is clearly distinguished from prior versions — staff always see the current version. Prior versions remain accessible for audit and legal reference. Each version has its own audit trail covering authoring, review, approval, publication, distribution, and acknowledgment events.
How does acknowledgment tracking work?
When a policy is published and distributed, each recipient signs an electronic acknowledgment specific to the policy version. Completion dashboards show acknowledgment rates by department, location, role, and individual. Automated reminders are sent to staff with outstanding acknowledgments. Each signed acknowledgment is stored as a governed document — retained per policy, linked to the employee record, and subject to audit trail and legal hold.
Can FormKiQ handle policy distribution across multiple jurisdictions?
Yes. Policies can be distributed to specific audiences based on jurisdiction, department, role, employment type, or any custom attribute. Jurisdiction-specific policies (e.g., UK-specific HR policies or Canadian privacy policies) are distributed only to staff in the applicable jurisdiction. Multi-jurisdiction organisations can manage a single policy library with targeted distribution rules within one FormKiQ deployment.
How does FormKiQ manage scheduled policy reviews?
Review intervals are set per policy — annual, biennial, or custom. Automated reminders notify policy owners before the review date. A review workflow is triggered on the review date, routing the policy to the owner and designated reviewers. Review outcomes (confirmed, revised, or retired) are recorded in the audit trail. Policies overdue for review are flagged on compliance dashboards.
Can FormKiQ analyse policies against regulatory requirements?
Yes. FormKiQ's AI Processing and Analysis module — powered by Amazon Bedrock — can analyse regulatory updates against existing policy content, assess the policy library for gaps, identify inconsistencies across related policies, and generate plain-language summaries. All AI processing runs within your AWS account.
How do policies connect to employee records?
Policy acknowledgments are stored as governed documents within each employee's record in FormKiQ. This means a single employee file contains their signed policy acknowledgments alongside their employment agreement, onboarding documents, performance records, and other governed HR documentation. When an auditor asks for proof that a specific employee acknowledged a specific policy on a specific date, the evidence is in the employee file — not in a separate policy platform's database.