Document Management Aligned with SOC 2 Trust Services Criteria — with Access Controls, Audit Logging, Encryption, and Change Management on AWS Infrastructure You Control
Organisations pursuing or maintaining SOC 2 compliance need document management infrastructure that doesn't just store documents securely — it produces the evidence that auditors need. SOC 2 is fundamentally an evidence framework: auditors assess whether your organisation has designed and implemented controls aligned with the Trust Services Criteria, and the primary way they assess this is by examining documentation — policies, access logs, change records, encryption evidence, and retention records.
When your document management platform operates in a vendor-controlled environment, producing this evidence depends on the vendor's willingness and ability to share audit logs, access records, and configuration documentation. When your document management platform deploys into your own AWS account, the evidence is yours — in your CloudTrail logs, your access policies, your KMS key usage records, and your audit trail.
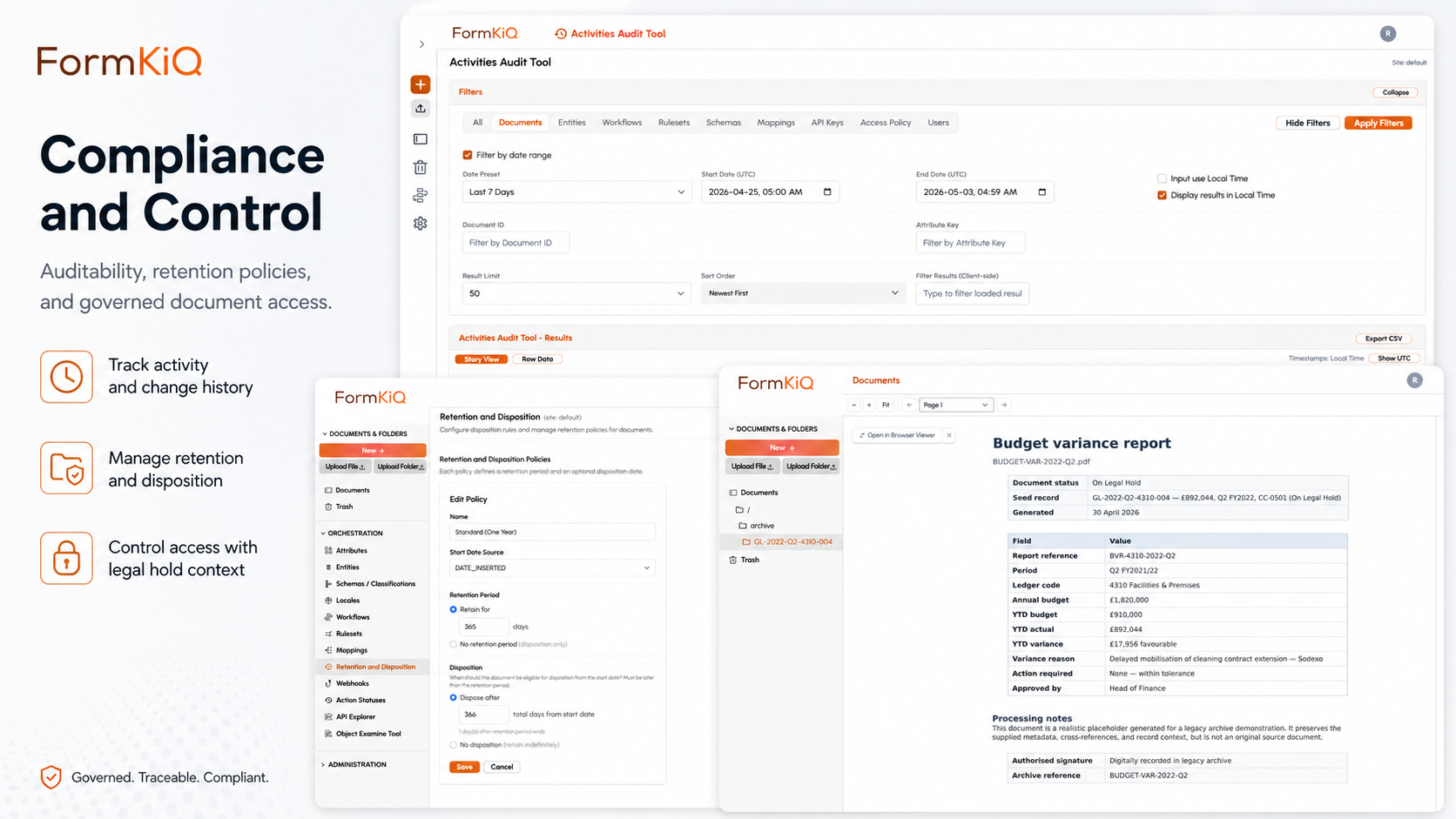
FormKiQ provides document management on AWS with the access controls, audit logging, encryption, change management, and operational monitoring that SOC 2 auditors evaluate — deployed into your own AWS account so the evidence of control effectiveness is in infrastructure you own and can produce directly.
SOC 2 Trust Services Criteria and Document Management
SOC 2 is organised around five Trust Services Criteria (TSC). Not all five are required — Security is always in scope, and organisations select which additional criteria apply based on their services and commitments.
Security (Common Criteria — Always in Scope)
| TSC Reference | Requirement | FormKiQ Capability |
|---|---|---|
| CC6.1 | Logical and physical access controls | ABAC at the document level; Amazon Cognito with SAML SSO; MFA support; unique user identification |
| CC6.2 | Registration and authorisation of new users | User provisioning through Cognito; role assignment; access approval workflows |
| CC6.3 | Modification or removal of user access | Access policy updates with audit trail; user deprovisioning on separation events |
| CC6.6 | Encryption of data in transit | TLS encryption for all API and console communication |
| CC6.7 | Encryption of data at rest | AWS KMS customer-managed keys; every document encrypted at rest |
| CC7.1 | Detection of unauthorised changes | Document versioning with integrity verification; CloudTrail monitoring |
| CC7.2 | Monitoring of system components for anomalies | CloudWatch monitoring; CloudTrail logging; audit trail analysis |
| CC8.1 | Change management for system components | CloudFormation-managed deployment; infrastructure changes tracked and auditable |
Availability
The Availability criteria apply when an organisation makes commitments about system uptime, redundancy, or disaster recovery. For document management, availability means that documents are accessible when authorised users need them, and that the system can recover from disruptions without data loss. FormKiQ's serverless architecture on AWS provides inherent availability advantages — there are no servers to fail, and the underlying services auto-scale with demand:
| TSC Reference | Requirement | FormKiQ Capability |
|---|---|---|
| A1.1 | System meets availability commitments | Amazon S3 eleven-nines durability; AWS Lambda auto-scaling; no single points of failure in serverless architecture |
| A1.2 | Environmental protections and recovery | AWS multi-AZ architecture; S3 cross-region replication available; backup and disaster recovery configurable |
| A1.3 | Recovery planning and testing | CloudFormation enables reproducible deployment; S3 versioning supports point-in-time recovery |
Processing Integrity
The Processing Integrity criteria apply when an organisation commits to processing data completely, accurately, and in a timely manner. For document management, this means that document workflows execute as designed, that document inputs are validated, and that outputs (generated documents, reports, exports) are accurate:
| TSC Reference | Requirement | FormKiQ Capability |
|---|---|---|
| PI1.1 | Processing is complete, accurate, timely, and authorised | Document workflow automation with validation rules; approval workflows with authorisation enforcement; audit-logged processing events |
| PI1.2 | System inputs are complete and accurate | Document type definitions enforce required metadata; completeness validation rules; IDP extraction verification |
| PI1.5 | Outputs are complete and accurate | Document generation from templates with data validation; output verification workflows |
Confidentiality
The Confidentiality criteria apply when an organisation handles information designated as confidential — client data, trade secrets, intellectual property, or any information with restricted access. This is where document-level access controls and sensitivity classification become critical:
| TSC Reference | Requirement | FormKiQ Capability |
|---|---|---|
| C1.1 | Identification and classification of confidential information | Metadata-based classification; AI-powered sensitivity classification; confidentiality tagging |
| C1.2 | Disposal of confidential information | Defensible disposition workflows with audit-logged deletion; S3 lifecycle management |
Privacy
The Privacy criteria apply when an organisation collects, uses, retains, or discloses personal information. Organisations that handle customer PII, employee data, or health information alongside their SOC 2 programme typically include this criteria. FormKiQ's privacy capabilities overlap with GDPR and other data protection framework support:
| TSC Reference | Requirement | FormKiQ Capability |
|---|---|---|
| P1–P8 | Notice, choice, collection, use, access, disclosure, quality, monitoring | Retention controls; access controls; data subject rights workflows; processing audit trails; sensitivity classification |
SOC 2 Evidence Production
The most valuable aspect of deploying document management in your own AWS account for SOC 2 is evidence ownership. Your auditors can examine your infrastructure directly:
| Evidence Type | What Auditors Need | Where It Lives in FormKiQ |
|---|---|---|
| Access control evidence | Who has access to what, and how access was authorised | ABAC policies in FormKiQ; Cognito user pool configuration; IAM policies — all in your AWS account |
| Access logs | Who accessed which documents, when, and how | FormKiQ document-level audit trail + CloudTrail — both in your AWS account |
| Encryption evidence | Proof that data is encrypted at rest and in transit | KMS key configuration and key usage logs — in your AWS account |
| Change management evidence | How system changes are controlled and tracked | CloudFormation stack history; deployment logs — in your AWS account |
| Monitoring evidence | How the system is monitored for anomalies and incidents | CloudWatch alarms, metrics, and logs — in your AWS account |
| Retention and disposal evidence | How data is retained and disposed of according to policy | FormKiQ retention policies, disposition audit logs — in your AWS account |
| Availability evidence | System uptime and recovery capability | CloudWatch metrics, S3 durability reports, deployment configuration — in your AWS account |
In a vendor-controlled SaaS environment, you must:
- Request access logs from the vendor
- Rely on the vendor's SOC 2 report (which covers their controls, not yours)
- Trust the vendor's encryption claims without independent verification
- Accept the vendor's monitoring coverage as sufficient
When FormKiQ runs in your own AWS account:
- Access logs are in your CloudTrail — you query them directly
- Encryption keys are in your KMS — you verify configuration yourself
- Monitoring is in your CloudWatch — you set thresholds and review alerts
- Change history is in your CloudFormation — you audit deployment changes directly
- Your auditors examine your infrastructure, not a vendor's SOC 2 report
Document Types for SOC 2 Programmes
SOC 2 creates a two-sided document management requirement. On one side, your SOC 2 controls protect the documents your organisation manages on behalf of clients and stakeholders — customer data, employee records, financial records. On the other side, your SOC 2 programme itself produces documentation that must be governed — policies, risk assessments, control documentation, audit evidence, and incident records. Most organisations manage these two sides in separate systems, which makes evidence production fragmented and audit preparation painful. FormKiQ manages both within a single governed platform:
Documents Governed Under SOC 2
| Document Category | Examples |
|---|---|
| Customer data documents | Customer records, engagement documentation, service delivery artifacts — the documents your SOC 2 controls protect |
| Employee records | Personnel files, training records, background check results, access authorisation forms |
| Vendor documentation | Vendor assessments, SOC reports, DPAs, security questionnaires, subprocessor agreements |
| Financial records | Transaction documentation, billing records, financial reports |
SOC 2 Programme Documentation
| Document Category | Examples | FormKiQ Governance |
|---|---|---|
| Policies | Information security policy, access control policy, change management policy, incident response policy, data classification policy | Policy lifecycle management — authoring, approval, version control, distribution, acknowledgment tracking |
| Risk assessments | Annual risk assessments, threat analyses, vulnerability assessments | Version control, review tracking, retention |
| Control documentation | Control descriptions, control testing procedures, control testing results | Version control, approval workflows, retention per audit cycle |
| Audit evidence | Access review records, change tickets, incident reports, exception documentation | Classification, retention, search and retrieval for auditor access |
| Training records | Security awareness training completion, role-specific training acknowledgments | Training tracking per employee, acknowledgment records |
| Incident records | Security incident reports, root cause analyses, remediation plans, customer notifications | Incident documentation workflows, retention, legal hold capability |
| Vendor assessments | Annual vendor security assessments, SOC report reviews, risk ratings | Vendor document management, annual review tracking, retention |
Continuous Monitoring Support
The difference between SOC 2 Type I and Type II is continuous evidence. Type I assesses control design at a point in time; Type II assesses control operation over a defined period — typically six to twelve months. This means your document management platform needs to produce evidence continuously, not just when auditors arrive. FormKiQ's deployment on AWS generates this evidence automatically through the platform's normal operation — no manual evidence collection or screenshot gathering required:
| Monitoring Area | What's Monitored | How Evidence Is Collected |
|---|---|---|
| Access | Who accessed which documents; access policy changes; user provisioning/deprovisioning | FormKiQ audit trail + CloudTrail — continuous, automated logging |
| Encryption | Key usage, key rotation, encryption status of documents | KMS key usage logs — continuous, automated |
| Availability | System uptime, error rates, latency | CloudWatch metrics and alarms — continuous, automated |
| Change management | Infrastructure changes, deployment updates, configuration modifications | CloudFormation stack events + CloudTrail — continuous, automated |
| Incident detection | Anomalous access patterns, failed authentication attempts, policy violations | CloudWatch alarms; CloudTrail event analysis; configurable alerting |
Who Uses SOC 2 Document Management on AWS
SOC 2 has become a de facto requirement for technology companies, managed service providers, and any organisation that handles customer data in a cloud environment. Enterprise buyers increasingly require SOC 2 Type II reports before procuring services, making SOC 2 compliance both a regulatory exercise and a sales enablement requirement:
| Organisation Type | SOC 2 Document Needs | Key Drivers |
|---|---|---|
| SaaS and technology companies | Customer data governance, security programme documentation, vendor assessment management | Customer-required SOC 2; enterprise sales enablement; trust centre evidence |
| Managed service providers | Client document governance, operational documentation, security programme management | Client contracts requiring SOC 2; competitive differentiation |
| Financial services and fintech | Transaction documentation, customer records, regulatory compliance documentation | SOC 2 + financial regulatory requirements; client and partner requirements |
| Healthcare technology | PHI handling documentation, security programme evidence, BAA management | SOC 2 + HIPAA; customer due diligence requirements |
| Professional services | Client engagement documentation, internal compliance programme, vendor management | Client-required SOC 2; professional regulatory compliance |
| Data processors and analytics providers | Data handling documentation, processing records, privacy programme evidence | SOC 2 + privacy frameworks (GDPR, CCPA); customer DPA requirements |
FormKiQ Editions for SOC 2 Document Management
| Capability | Core Foundation |
Essentials Operational |
Advanced AI + Automation |
Enterprise Full platform |
|---|---|---|---|---|
| Foundation | ||||
| Document Storage (S3) & API | ||||
| Tagging, Search & Classification | ||||
| OCR (Tesseract) | ||||
| Essentials and above | ||||
| OCR & IDP (Textract) | — | |||
| SSO (SAML — Entra, Google, Auth0) | — | |||
| Workflows, Queues & Rulesets | — | |||
| Encryption (KMS — in-transit & at-rest) | — | |||
| Document Control & Versioning | — | |||
| Antivirus & Anti-Malware | — | |||
| Advanced and Enterprise | ||||
| AI Processing & Sensitivity Classification (Bedrock) | — | — | ||
| Document Generation | — | — | ||
| eSignature Integration | — | — | ||
| Enhanced Full-Text Search (OpenSearch) | — | — | ||
| Multi-Instance & Multi-Region Licensing | — | — | ||
| Enterprise only | ||||
| Vendor-Managed & Hybrid Deployment | — | — | — | |
| Custom SLAs & Compliance Consulting | — | — | — | |
| Support | ||||
| Support | Community (Slack & GitHub) | Support Portal (2-business-day SLA) | Private Slack + videoconference + 40 hrs onboarding | Rapid response (8-business-hour SLA) + strategic architecture support |
Deployment Models
| Model | Description | Availability |
|---|---|---|
| Customer-Managed AWS | Deploys directly into your AWS account via CloudFormation. Full control of infrastructure, networking, encryption keys, and operations. | All editions |
| Vendor-Managed | FormKiQ manages the AWS infrastructure on your behalf — deployment, updates, and operational support. | Enterprise |
| Hybrid | You retain control of specific components (encryption keys, network config) while delegating operational management to FormKiQ. | Enterprise |
Every deployment is a dedicated, isolated instance. FormKiQ does not operate a shared multi-tenant environment.
Getting Started
FormKiQ Core can be deployed to your AWS account in fifteen to twenty minutes. SOC 2-aligned capabilities — including KMS encryption, ABAC, audit trails, workflows, and policy lifecycle management — are available from FormKiQ Essentials onward.
Frequently Asked Questions
Is FormKiQ SOC 2-certified?
SOC 2 is not a certification — it's an audit report. SOC 2 reports are issued for specific service organisations based on an auditor's examination of their controls. FormKiQ provides the technical controls (encryption, access controls, audit trails, change management) and programme documentation support (policy management, training tracking, vendor assessment, incident documentation) that organisations need for their own SOC 2 programmes. FormKiQ deploys into your AWS account, so the controls and evidence are yours — audited as part of your SOC 2 examination.
How does deploying in my own AWS account help with SOC 2?
When document management runs in your AWS account, the evidence of control effectiveness is in infrastructure you own — CloudTrail access logs, KMS encryption records, CloudWatch monitoring, CloudFormation change history. Your auditors examine your infrastructure directly rather than relying on a vendor's SOC 2 report. This gives you direct control over the evidence production and reduces reliance on third-party attestations.
Can FormKiQ manage our SOC 2 programme documentation?
Yes. FormKiQ manages both the documents your SOC 2 controls protect (customer data, employee records, vendor documentation) and the documents your SOC 2 programme produces (policies, risk assessments, control documentation, audit evidence, training records, incident reports). Policy lifecycle management with version control, approval workflows, and acknowledgment tracking is particularly relevant for SOC 2 policy documentation.
How does FormKiQ support SOC 2 Type II continuous monitoring?
SOC 2 Type II requires evidence that controls operated effectively over the audit period. FormKiQ's deployment on AWS produces continuous evidence through CloudTrail (access and change logging), KMS (encryption key usage), CloudWatch (availability and monitoring), and FormKiQ's document-level audit trail — all operating automatically throughout the audit period. This continuous evidence collection is a structural advantage of deploying in your own AWS account versus relying on periodic vendor reports.
What Trust Services Criteria does FormKiQ support?
FormKiQ supports controls across all five Trust Services Criteria: Security (access controls, encryption, audit logging, change management), Availability (S3 durability, serverless auto-scaling, recovery capability), Processing Integrity (workflow validation, approval enforcement, processing audit trails), Confidentiality (sensitivity classification, access controls, defensible disposition), and Privacy (retention controls, data subject rights workflows, processing records). Security is always in scope; the additional criteria are selected based on your organisation's commitments.